At Scan N More, we understand the critical importance of hard disk drive destruction in today’s digital landscape. Improper disposal of storage devices can lead to devastating data breaches, legal consequences, and reputational damage.
In this guide, we’ll explore effective methods for securely destroying hard drives and protecting sensitive information. We’ll also share best practices to help you develop a robust data destruction policy that safeguards your organization’s valuable data.
Why Secure Hard Drive Destruction Matters
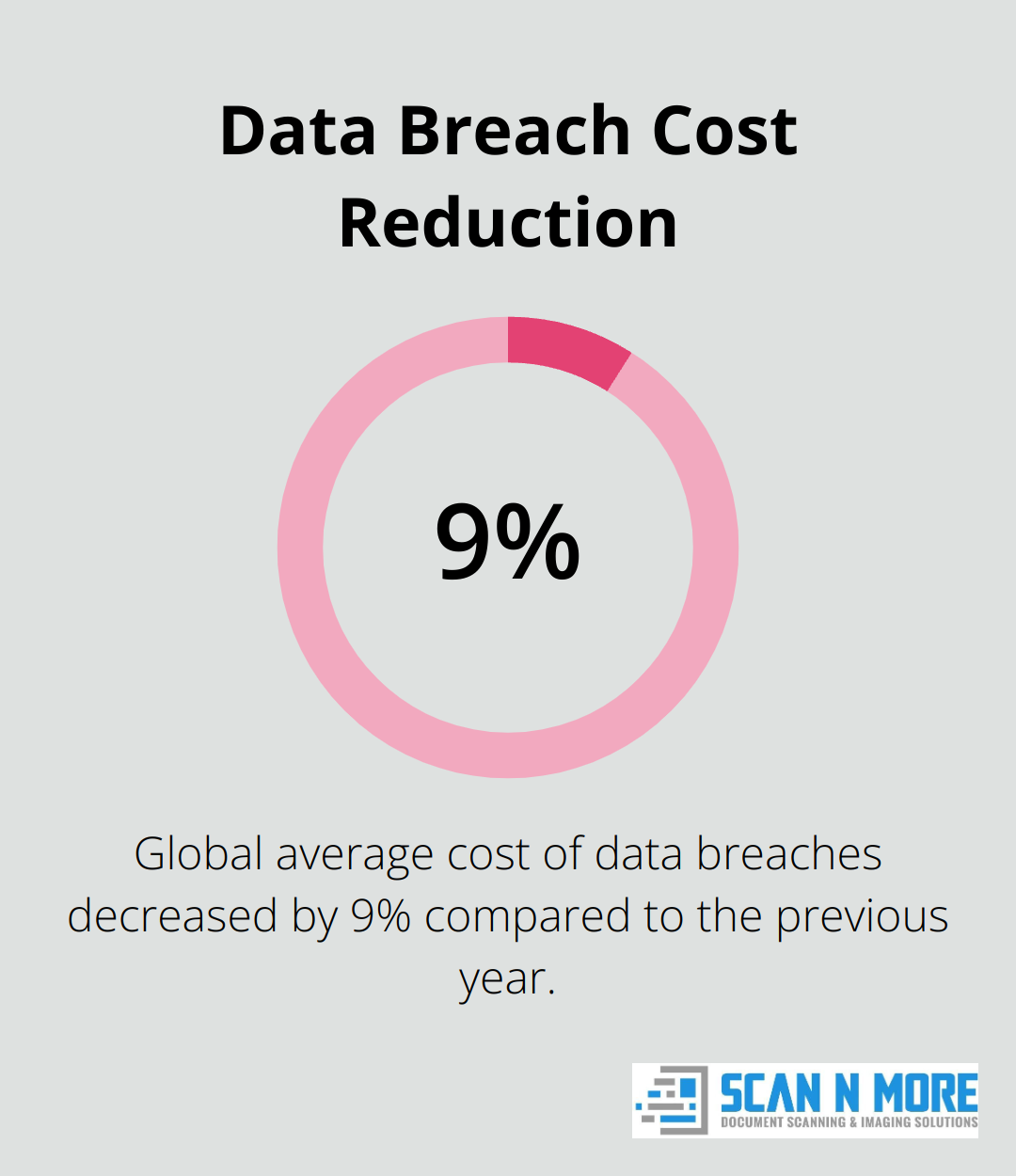
The High Cost of Data Breaches
In the digital age, data forms the foundation of businesses and individuals alike. Data breaches from improperly disposed hard drives can lead to severe consequences. IBM’s Cost of a Data Breach Report reveals that the global average cost of a data breach decreased by 9% compared to the previous year, driven by faster identification and containment. This figure represents more than just financial loss; it includes reputational damage, legal fees, and lost business opportunities.
Legal Ramifications of Improper Disposal
The legal landscape of data protection presents complex and unforgiving challenges. Regulations such as GDPR (Europe), CCPA (California), and HIPAA (healthcare) mandate strict data protection measures. Violations can result in hefty fines (up to €20 million or 4% of global turnover under GDPR). Proper data disposal doesn’t just avoid penalties; it maintains trust and integrity in business operations.
Types of Sensitive Data at Risk
Hard drives often contain more sensitive information than many realize. Common examples include:
- Financial records
- Customer databases
- Proprietary business strategies
- Personal employee information
- Patient records (in healthcare settings)
Even seemingly innocuous data can provide malicious actors with the pieces to create comprehensive profiles for identity theft or corporate espionage.
The Importance of Professional Destruction Services
Professional hard drive destruction services ensure that your information is permanently and securely erased, protecting you, your business, and your clients. These processes typically include multiple stages of verification and documentation, providing clients with peace of mind.
Cost-Benefit Analysis of Secure Destruction
The cost of proper destruction pales in comparison to the potential fallout of a data breach. Investing in secure hard drive destruction protects businesses, customers, and future operations. This small investment can prevent massive financial losses and irreparable damage to reputation.
As we move forward, we’ll explore the various methods available for destroying hard drives, each with its own set of advantages and considerations.
How to Destroy Hard Drives Effectively
At Scan N More, we understand the critical importance of proper hard drive destruction. Let’s explore the most effective methods to ensure your sensitive data remains protected.
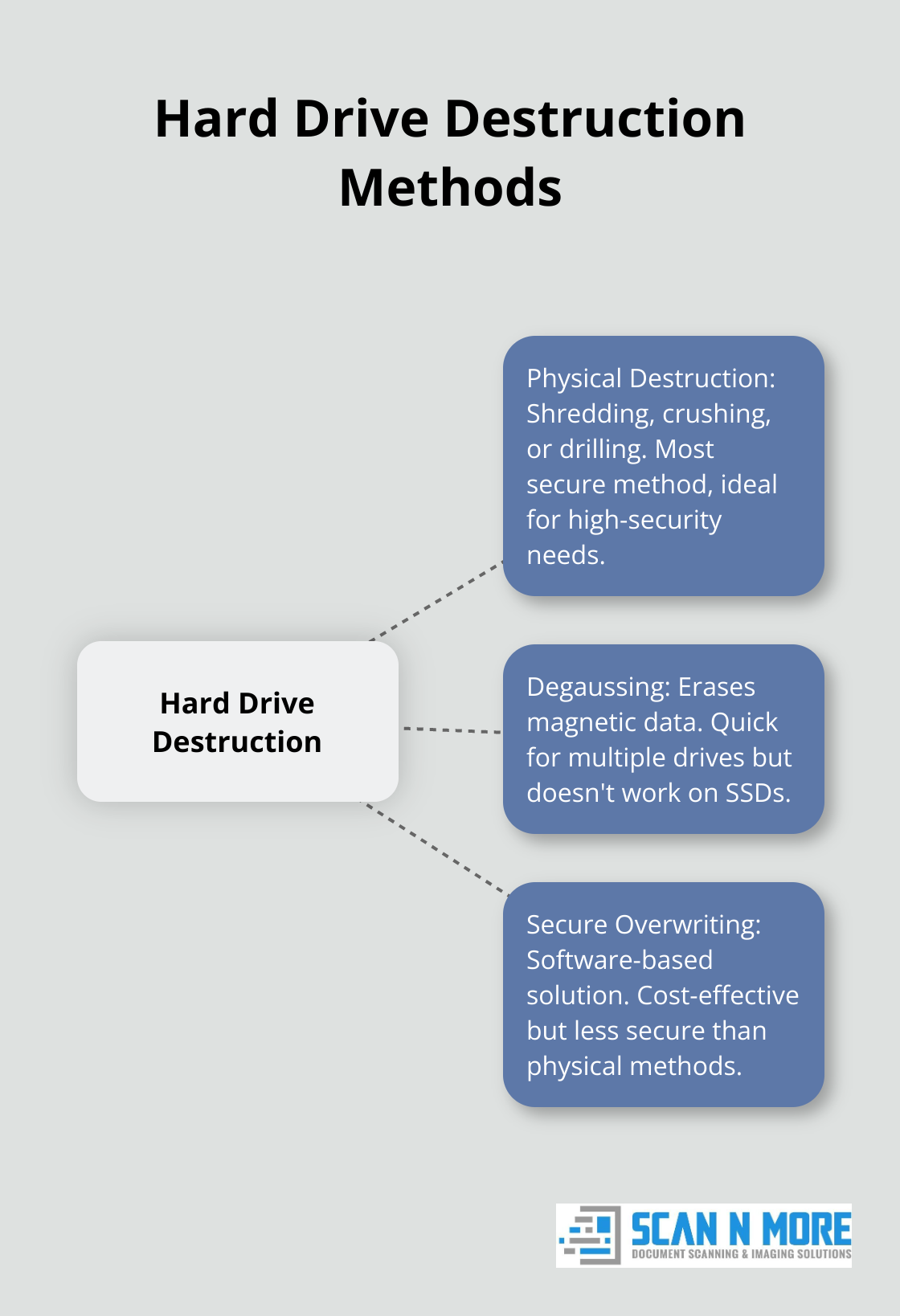
Physical Destruction: The Ultimate Solution
Physical destruction provides the most foolproof way to render a hard drive unusable. Shredding stands out as particularly effective, reducing drives to tiny fragments that defy reassembly. Industrial shredders process hundreds of drives per hour, making this method ideal for large-scale destruction.
Crushing and drilling offer alternatives for smaller operations. Hydraulic crushers apply immense pressure to warp and break internal components. Multiple holes drilled through the platters can prevent data recovery, but this method requires penetration of the entire disk surface.
Degaussing: Erasing Magnetic Data
Degaussing is a process used to permanently erase data from magnetic storage media, such as hard drives, tapes, and floppy disks. This method processes multiple drives quickly. However, it doesn’t work for solid-state drives (SSDs) and some high-coercivity drives.
The National Security Agency (NSA) recommends degaussers with field strengths of at least 14,000 oersteds for most drives. Always verify that your degausser meets these standards for optimal security.
Secure Overwriting: Software-Based Solutions
For reusable drives, secure overwriting software presents an option. These programs repeatedly write random data over the entire drive, making original data unrecoverable. While the U.S. Department of Defense previously recommended a 3-pass overwrite (DoD 5220.22-M), modern standards like NIST 800-88 suggest a single overwrite may suffice for most purposes.
Popular tools include DBAN (Darik’s Boot and Nuke) for HDDs and manufacturer-specific utilities for SSDs. However, software methods generally offer less security than physical destruction or degaussing.
Comparing Methods: Effectiveness vs. Cost
The choice of destruction method requires consideration of both security and budget. Physical destruction offers the highest security but can prove costly for large volumes. Degaussing works efficiently for HDDs but requires specialized equipment. Software overwriting costs the least but also provides the least security.
For maximum security, we recommend a combination approach: degauss or overwrite drives first, then physically destroy them. This ensures data remains irrecoverable even if individual steps fail.
The cost of proper destruction pales in comparison to the potential fallout of a data breach. Investing in secure methods protects not just your data, but your reputation and financial stability as well.
Now that we’ve covered the most effective methods for hard drive destruction, let’s move on to discuss best practices for implementing these techniques in your organization.
Implementing a Robust Hard Drive Destruction Strategy
Create a Comprehensive Data Destruction Policy
Organizations must draft a detailed policy that outlines every step of their hard drive destruction process. This document should clearly define roles, responsibilities, destruction methods, and timelines. A study by the Ponemon Institute revealed that the risk of data breach is especially great due to employees’ loss of a laptop or other mobile data-bearing devices.
The policy should address:
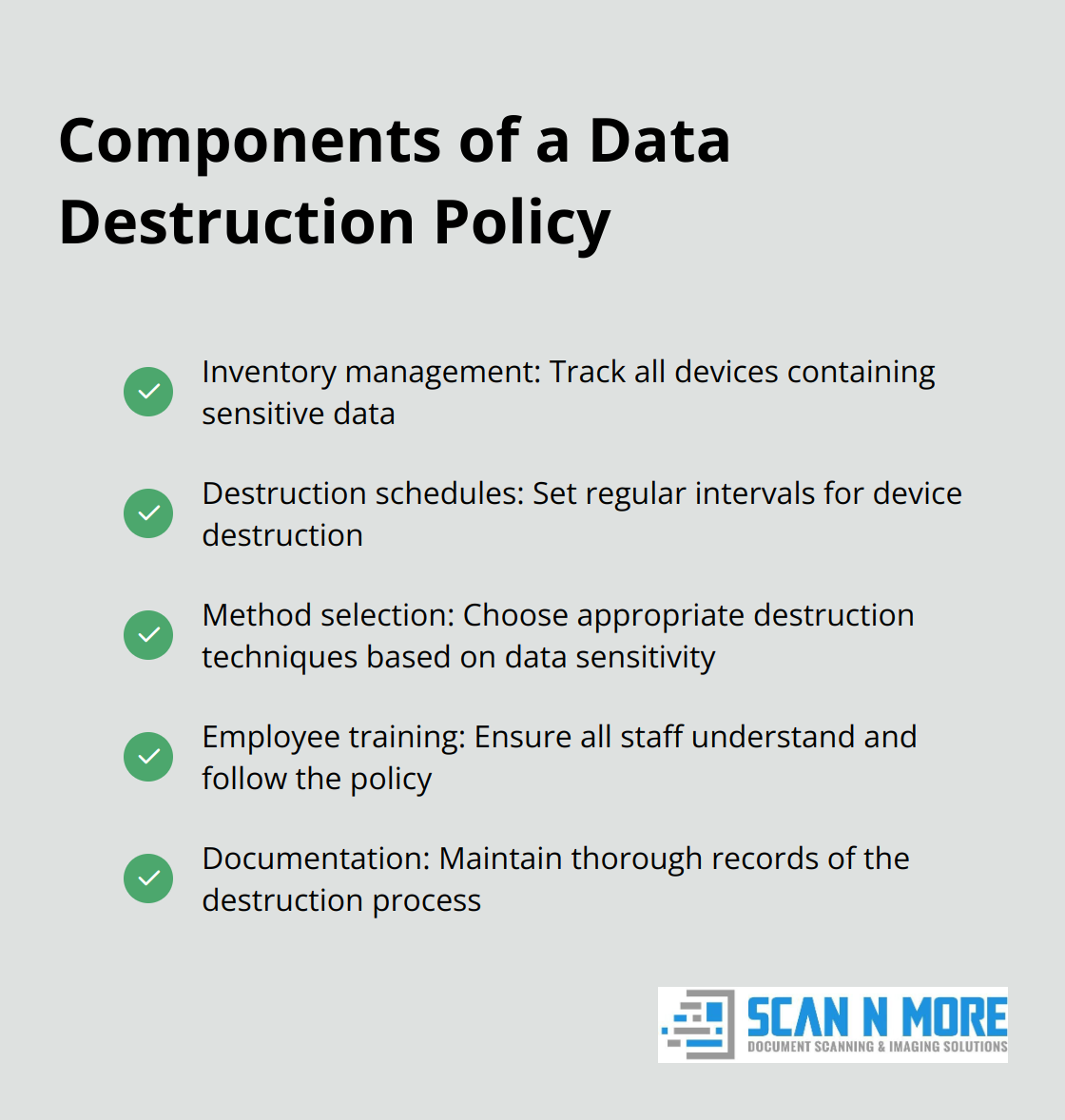
Maintain Proper Documentation
Thorough documentation is essential for both compliance and security. Organizations should implement a chain of custody system that tracks each hard drive from decommissioning to final destruction. This system should record:
- Device serial numbers
- Date and time of collection
- Responsible personnel at each stage
- Destruction method used
- Date and time of destruction
Select a Certified Destruction Service Provider
While in-house destruction might seem cost-effective, partnering with a certified provider often offers superior security and compliance. When choosing a provider, organizations should look for:
- NAID AAA Certification (verifies secure data destruction companies’ services’ compliance with all known data protection laws through scheduled and surprise audits)
- On-site destruction capabilities
- Verifiable destruction methods
- Secure transport (if off-site destruction is necessary)
Prioritize Environmental Responsibility
Responsible recycling is a critical component of any hard drive destruction strategy. E-waste contains harmful materials that can damage the environment if not properly handled. Organizations should partner with R2 (Responsible Recycling) or e-Stewards certified recyclers to ensure their destroyed devices are processed safely and sustainably.
For organizations dealing with sensitive data subject to regulations like HIPAA, hard drive shredding is a reliable and compliant destruction method. Industrial-grade shredders can reduce hard drives to tiny fragments, ensuring complete data destruction.
Final Thoughts
Hard disk drive destruction protects organizations from data breaches, identity theft, and legal consequences. Physical destruction, degaussing, and secure overwriting offer different levels of security and cost-effectiveness. Organizations must choose the method that best fits their needs and security requirements.
A comprehensive hard drive destruction strategy includes a detailed policy, proper documentation, and certified service providers. Environmental responsibility also plays a key role in the safe disposal of destroyed devices. The cost of proper destruction is minimal compared to the potential fallout of a data breach.
Scan N More offers expert hard drive destruction services as part of our document management solutions. We ensure your sensitive data remains protected throughout the destruction process (and beyond). Our team provides peace of mind and safeguards your organization’s reputation and financial stability.

