Data breaches cost businesses an average of $4.45 million in 2023, according to IBM’s Cost of a Data Breach Report. Organizations face mounting pressure from regulators and customers to protect sensitive information.
We at Scan N More understand that data security and compliance isn’t optional anymore. Modern businesses need robust frameworks that protect documents while meeting strict regulatory standards across industries.
Data Security Fundamentals for Business Operations
What Attacks Target Your Business Data
External actors cause 83% of data breaches according to Verizon’s 2023 Data Breach Investigations Report, with 73% involving human elements like employee errors or permission misuse. Ransomware attacks increased 41% in 2022, while phishing remains the top attack vector that targets business credentials. Organizations must recognize that email compromise, insider threats, and third-party vendor vulnerabilities represent the highest risk categories for document-heavy operations.
Multi-Factor Authentication Blocks 99.9% of Attacks
Microsoft data shows multi-factor authentication blocks 99.9% of automated attacks that target user accounts. Deploy MFA across all document management systems, email platforms, and cloud storage solutions immediately. Role-based access controls should limit document permissions to specific job functions only. Zero-trust architecture requires verification for every access request and treats internal networks as potentially compromised. Regular access reviews must occur quarterly to remove unnecessary permissions and inactive accounts.
Security Training Cuts Human Error by 70%
Organizations with comprehensive security awareness programs experience 70% fewer security incidents that human error causes. Monthly phishing simulations should test employee responses to suspicious emails and documents. Focus training on how to recognize social engineering tactics, proper password management, and secure document handling procedures. Document classification training helps employees identify sensitive information that requires special protection measures (particularly for healthcare and financial records). Create clear escalation procedures for reporting suspicious activities or potential security incidents within your organization.
Access Controls Protect Sensitive Documents
Implement the principle of least privilege across all document systems to restrict access to only necessary personnel. Network segmentation isolates critical document repositories from general business systems. Regular permission audits help identify and remove excessive access rights that accumulate over time. Monitor file access patterns to detect unusual behavior that might indicate compromised accounts or insider threats.
The foundation you build with these security protocols directly impacts your ability to meet specific compliance requirements that vary significantly across different industries.
Compliance Requirements and Regulations
Healthcare organizations face HIPAA penalties while law firms risk state bar disciplinary action for client data breaches. Financial institutions must navigate overlapping requirements from SOX, PCI-DSS, and state banking regulations that each carry million-dollar penalty structures. The complexity increases when organizations operate across multiple industries or handle documents for clients in regulated sectors.
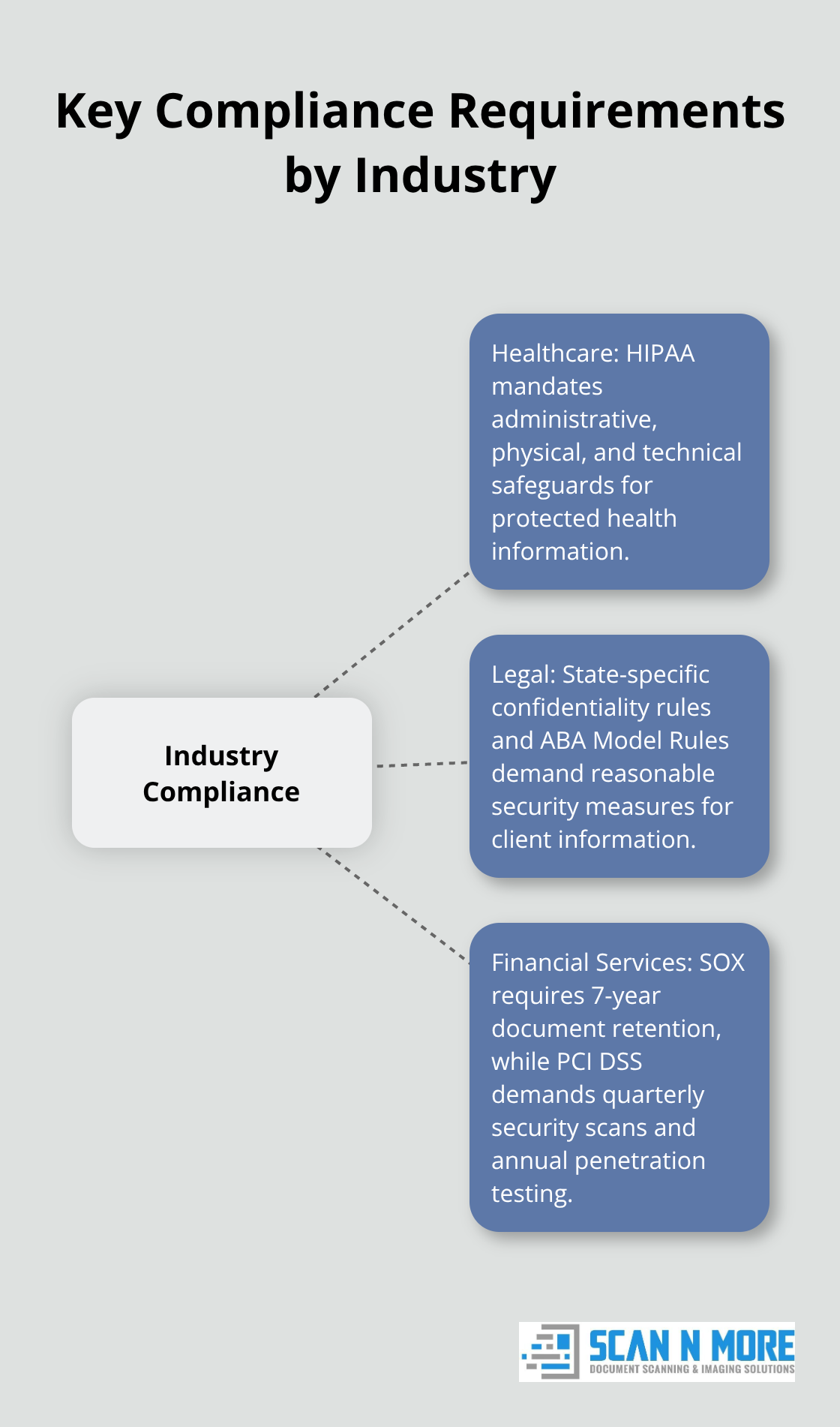
HIPAA Requires Complete Document Control
HIPAA mandates that healthcare organizations implement administrative, physical, and technical safeguards for all protected health information. Covered entities must conduct risk assessments every 12 months and document all PHI access attempts through comprehensive audit logs. Business associate agreements must specify exact security requirements for any vendor that handles medical documents (including professional scanning services). The minimum necessary rule restricts access to only the information required for specific job functions, which means organizations need granular permission controls for different document types. Breach notification requirements mandate that organizations report incidents that affect 500 or more individuals to HHS within 60 days, which makes rapid incident detection systems essential for healthcare document management.
Legal Professionals Face Strict Confidentiality Rules
Legal professionals must comply with state-specific confidentiality rules that often exceed federal privacy standards, with attorney-client privilege that requires absolute protection of client communications and case documents. The American Bar Association Model Rules demand reasonable security measures, but courts increasingly expect law firms to implement enterprise-grade encryption and access controls. State bar associations now investigate data breaches as potential ethical violations, which can result in professional sanctions or license suspension for attorneys who fail to protect client information adequately.
Financial Services Navigate Multiple Regulatory Frameworks
Financial services organizations under SOX must maintain document retention schedules for seven years and prove internal controls prevent unauthorized access to financial records. PCI DSS compliance requires quarterly security scans and annual penetration testing for any organization that processes credit card data (with fines reaching $100,000 per month for non-compliance). Banking regulations mandate real-time fraud monitoring and suspicious activity reports for document access patterns that deviate from normal business operations.
These regulatory requirements create specific technical demands that organizations must address through their document management systems and security protocols.
Best Practices for Secure Document Management
Document Encryption Standards Protect Data
AES-256 encryption protects documents at rest while TLS 1.3 secures transmission, but organizations must implement both simultaneously to prevent data exposure during transfers. The National Institute of Standards and Technology recommends AES-256 as the gold standard for document encryption, with key rotation every 12 months to maintain security effectiveness. End-to-end encryption prevents unauthorized access even when documents traverse multiple networks or cloud platforms.
Organizations should deploy certificate pinning for mobile applications and implement perfect forward secrecy to protect historical communications if encryption keys become compromised. Database-level encryption adds another protection layer for document metadata and information that attackers often target.
Complete Audit Trails Track Every Document Action
Complete audit trails record every document access, modification, and share event with timestamps, user identifications, and IP addresses to meet regulatory requirements. Organizations that implement comprehensive logs reduce breach investigation time by 287 days according to IBM’s Cost of a Data Breach Report 2024. Real-time systems should flag unusual access patterns like bulk downloads outside business hours or geographic anomalies that suggest compromised accounts.
Document version control maintains historical records of all changes while automated backup systems create recovery points every four hours for critical files. Immutable log storage prevents tampering with audit records and provides forensic evidence during security investigations or compliance audits.
Monthly Security Assessments Prevent Most Exploits
Security assessments must occur monthly rather than annually because new vulnerabilities emerge constantly, with the average time between discovery and exploitation at just 15 days. Automated penetration tests identify configuration weaknesses in document management systems while manual tests reveal business logic flaws that automated scans miss.
Third-party security audits provide independent validation of security controls and often identify blind spots that internal teams overlook. Organizations should maintain current software versions across all document systems and implement emergency patch procedures for critical vulnerabilities within 72 hours of disclosure (particularly for systems that handle sensitive documents).
Final Thoughts
Data security and compliance demands immediate action from organizations across all industries. The statistics paint a clear picture: businesses that implement comprehensive security frameworks reduce breach costs by millions while those that ignore compliance face escalating penalties and reputational damage. Organizations must foster security-conscious cultures where employees understand their role in protecting sensitive information.
Regular training programs, clear policies, and consistent enforcement create environments where security becomes second nature rather than an afterthought. The path forward involves continuous improvement and adaptation. Threat landscapes evolve rapidly, and regulatory requirements become more stringent each year (with new frameworks emerging quarterly across different sectors).
Organizations that treat security as an ongoing process rather than a one-time project position themselves for long-term success. We at Scan N More help organizations transform paper-based processes while maintaining strict security standards and regulatory compliance. Our professional document scanning services provide the foundation businesses need to build robust data security and compliance frameworks that grow with their operations.
