Data center breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 Cost of a Data Breach Report. The stakes are high, and choosing the wrong data center security solution can leave your infrastructure exposed to threats you didn’t anticipate.
We at Scan N More know that selecting the right protection requires understanding both the threats you face and the features that actually matter. This guide walks you through the essential criteria for evaluating security providers so you can make a decision based on facts, not marketing promises.
The Real Threats Inside Your Data Center
Unauthorized Access Remains the Primary Attack Vector
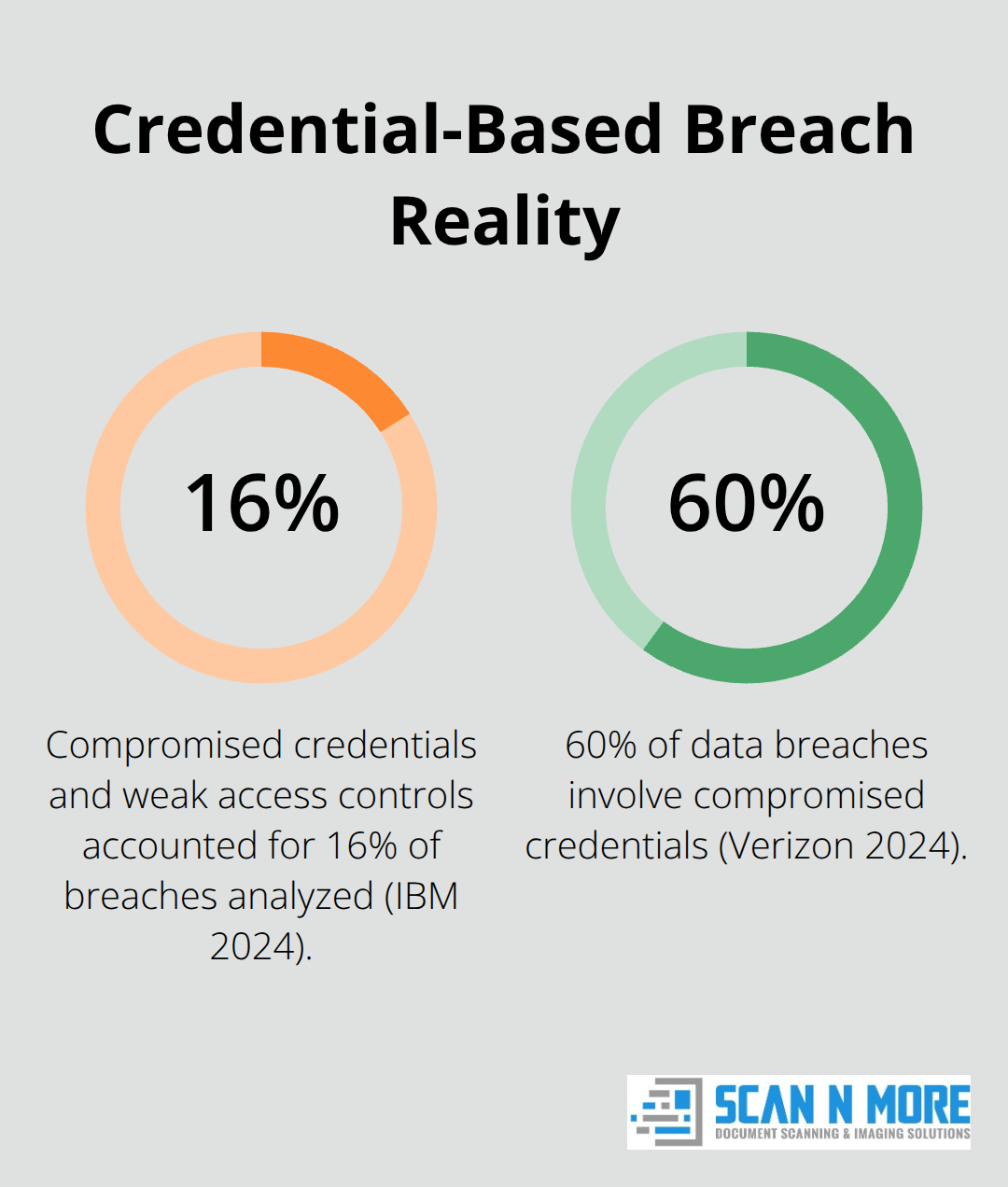
Unauthorized access causes the most data center breaches. IBM’s 2024 Cost of a Data Breach Report shows that compromised credentials and weak access controls accounted for 16% of all breaches analyzed, making them the leading attack vector. Organizations regularly discover that former employees, contractors, or attackers with stolen credentials maintained access to critical systems months after initial compromise.
This persistence happens because most teams fail to revoke access promptly or monitor for unusual account activity. The damage compounds when attackers use legitimate credentials to move through your infrastructure undetected.
Physical Security Gaps Create Direct Attack Pathways
Physical security breaches expose your data center to immediate, catastrophic risk. A single unlocked server room, an unmonitored loading dock, or inadequate visitor controls gives attackers direct access to hardware. They can install malware, steal data, or sabotage infrastructure without triggering a single alert. These incidents happen regularly in organizations that treat physical security as secondary to digital controls.
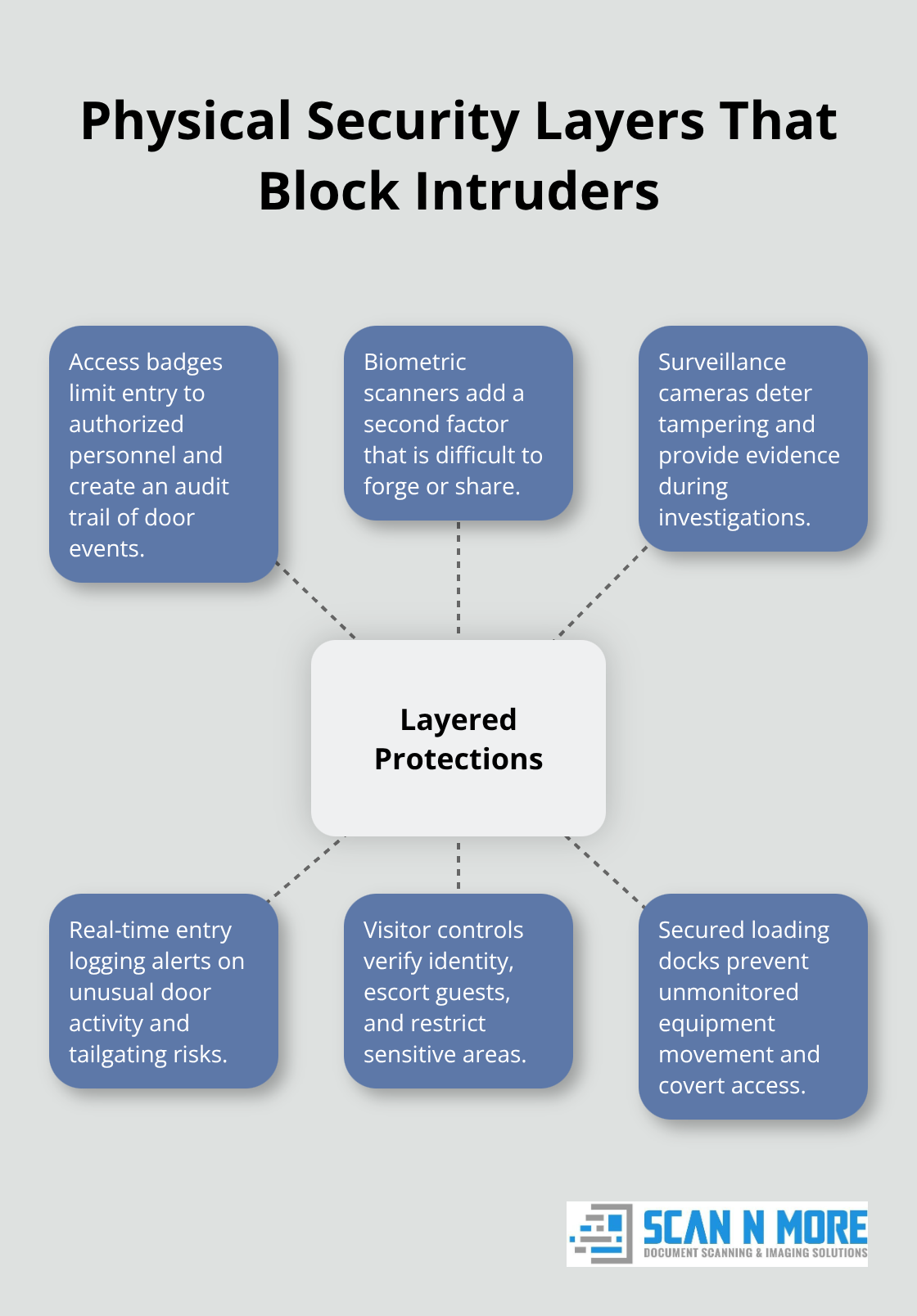
Layered physical protections-including access badges, biometric scanners, surveillance cameras, and real-time entry logging-stop attackers before they reach your systems.
Malware and Ransomware Exploit Hidden Traffic Channels
Attackers now use encrypted channels like TLS 1.3 to hide malicious traffic inside your data center, making detection difficult without proper decryption capabilities and analysis tools. Ransomware specifically targeting data centers has increased in sophistication and cost. Once attackers gain entry through a compromised account or physical access, they move freely between servers, databases, and applications unless your infrastructure includes microsegmentation and strict intrazone traffic controls.
Lateral Movement Detection Determines Your Response Speed
Most organizations lack real-time visibility into lateral movement, discovering breaches only weeks or months after initial compromise. The cost difference is dramatic-organizations that detect breaches within 30 days spend significantly less on remediation than those taking 90+ days, according to incident response data. Your choice of security solution directly impacts detection speed and ultimately determines how much damage attackers inflict before you stop them. Real-time monitoring and threat detection capabilities separate solutions that protect your infrastructure from those that merely react to incidents after the fact.
What Security Features Actually Stop Data Center Breaches
Multi-Layer Authentication Stops Unauthorized Access
Multi-layer authentication stops unauthorized access cold, but most organizations implement it poorly. Requiring passwords plus a second factor like biometric scanning or hardware keys cuts unauthorized access incidents dramatically, yet 60% of data breaches still involve compromised credentials according to Verizon’s 2024 Data Breach Investigations Report. The weakness isn’t the technology-it’s enforcement. Your solution must enforce authentication across every access point: user logins, administrative accounts, API connections, and inter-server communication. Teams that skip authentication for internal traffic assume that traffic is safe. It isn’t.
Real-Time Monitoring Catches Attackers Within Minutes
Real-time monitoring tracks failed login attempts, unusual access patterns, and credential misuse before attackers cause damage. When someone accesses servers outside their normal geographic location or time zone, or when they suddenly request files they’ve never touched before, your system should flag this immediately. Solutions that log access comprehensively-recording who accessed what, when, and from where-give your incident response team the evidence needed to trace attacks back to their source and prevent recurrence. Detection speed matters more than you might think. Companies that contain a breach in less than 30 days save more than $1 million in comparison to those who take longer.
Compliance Certifications Prove Security Actually Works
Compliance with industry standards matters less as a checkbox and more as proof that your provider has actually built security correctly. ISO 27001, SOC 2 Type 2, and NIST 800-53 certifications indicate independent auditors have verified the provider’s controls work as claimed. Don’t accept marketing claims about compliance; request the actual audit reports or certifications. PCI DSS compliance is non-negotiable if you process payment data, HIPAA if you store healthcare information, and GDPR if you handle European customer data.
Encryption and Data Isolation Protect Your Infrastructure
The provider should offer encryption at rest and in transit as standard, not as an add-on. They should segment your data from other customers’ data using network isolation, not just logical separation. Real-time dashboards showing your security posture, compliance status, and remediation progress separate providers serious about security from those that hide problems until audits force disclosure. When evaluating providers, demand evidence through customer references and ask specifically about detection speed-how fast they identified their last customer breach and how long remediation took.
Your choice of security features directly determines whether your data center remains protected or becomes a liability. The next section walks you through how to assess which providers actually deliver these capabilities versus those that merely promise them.
Evaluating and Comparing Data Center Security Providers
Certifications Prove Security Controls Actually Work
Certifications matter, but not in the way most organizations think. A provider with ISO 27001 or SOC 2 Type 2 attestation has undergone independent audit verification that their security controls actually work. This means auditors tested access controls, encryption implementation, and incident response procedures and confirmed they function as designed. Vague marketing claims about security mean nothing. Demand to see the actual audit reports or third-party certifications before moving forward. If a provider hesitates to share these documents, that hesitation tells you everything you need to know.
Track Record Determines Detection Speed and Breach Containment
Track record comes down to one critical question: how fast do they detect and contain breaches in their own customer environments? Ask prospective providers directly about their average detection time for breaches among existing clients, then cross-reference this with industry benchmarks.
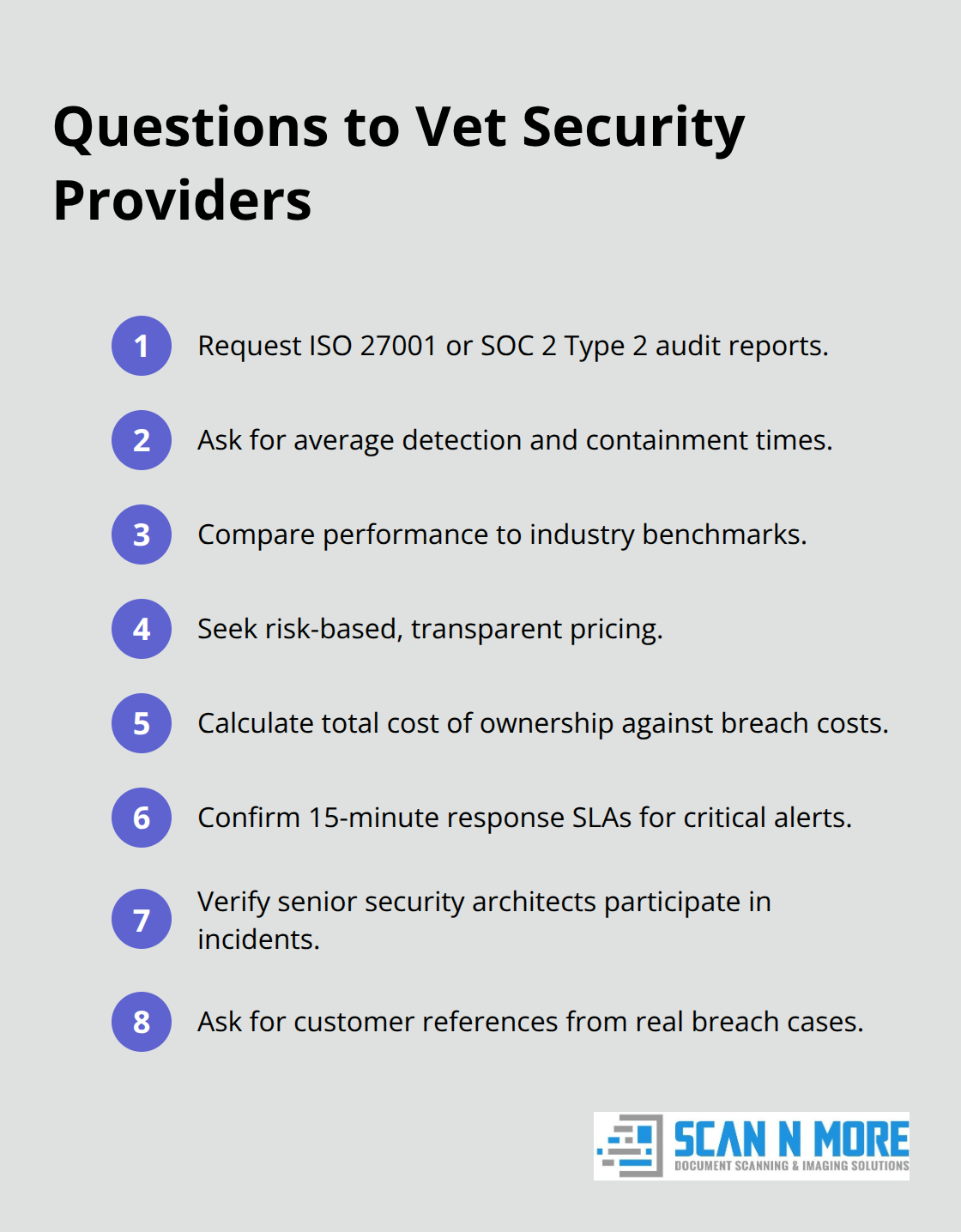
According to IBM’s 2024 Cost of a Data Breach Report, the global average cost of a data breach reached $4.88 million in 2024. A provider claiming they help customers detect threats in days rather than weeks has built something genuinely different. Request customer references who have experienced actual breaches and ask about detection timelines, not just happy-path security scenarios.
Pricing Models Reveal True Understanding of Your Risk
Pricing models reveal whether providers actually understand your risk profile or are simply selling commodity software. Avoid providers charging per user or per gigabyte of data monitored because these models incentivize them to upsell features you don’t need. Instead, seek providers offering transparent, risk-based pricing tied to your specific infrastructure size and threat level. Calculate total cost of ownership by weighing the solution cost against potential breach expenses. If a data center breach costs your organization $4.88 million on average, a security solution priced at $50,000 to $200,000 annually provides measurable ROI through prevention alone.
Service Level Agreements Specify Response Commitments
Request detailed service level agreements specifying response times for critical alerts, uptime guarantees, and remediation support. A provider committing to 15-minute response times for critical alerts demonstrates confidence in their monitoring capabilities. Support quality separates solutions that protect you from those that abandon you during crises. Evaluate whether support includes security experts who understand your infrastructure or merely tier-one technicians reading scripts. Ask about escalation procedures and confirm that senior security architects are available during incidents, not just during business hours.
Final Thoughts
Selecting the right data center security solution requires evaluating three core criteria: proven certifications from independent auditors, demonstrated detection speed from real customer incidents, and transparent pricing tied to your actual risk profile. Providers offering ISO 27001 or SOC 2 Type 2 attestation have undergone rigorous verification that their controls function as designed. Those with documented track records of detecting breaches within days rather than weeks have built infrastructure that actually protects you.
Implementation begins with a security assessment identifying your current gaps in access controls, physical security, and monitoring capabilities. Establish clear timelines for deploying multi-layer authentication, real-time monitoring, and compliance frameworks aligned to your industry requirements. Assign accountability for ongoing security reviews and threat response procedures so your team maintains continuous improvement as threats evolve.
Beyond digital security controls, physical security demands equal attention-protecting paper documents and decommissioned hardware containing sensitive data strengthens your overall protection. We at Scan N More help organizations eliminate physical security risks through professional document scanning and secure hard drive destruction services. Digitizing sensitive documents removes them from physical vulnerability while maintaining compliance with industry standards.
