Data breaches cost companies an average of $4.45 million per incident, according to IBM’s 2024 report. Yet most organizations still lack visibility into where their sensitive data lives and who can access it.
At Scan N More, we believe data security posture management tools are no longer optional-they’re essential. These solutions give you the real-time visibility and automated controls needed to protect your business before attackers strike.
Why Your Data Security Posture Actually Matters
Data breaches hit organizations 2,365 times in 2024 according to the Identity Theft Resource Center, and that number keeps climbing. The frequency alone should alarm you, but the real problem is that most organizations don’t know what data they protect. Without visibility into where sensitive information lives, who accesses it, and how it moves across your systems, you’re essentially guessing at your security posture. This isn’t acceptable in an era where regulatory bodies fine companies millions for data mishandling and customers abandon brands after breaches. Organizations with poor data visibility spend significantly more on incident response and remediation because they detect problems too late.
Regulatory penalties are staggering and real
GDPR violations cost companies up to 20 million euros or 4% of global revenue, whichever is higher. HIPAA penalties reach 1.5 million dollars per violation category annually. CCPA fines start at 2,500 dollars per violation and jump to 7,500 for intentional violations. These aren’t theoretical numbers-regulators assess them to real companies every month. Compliance teams spend countless hours gathering evidence that their organization knows where regulated data lives, who accesses it, and how it’s protected. DSPM tools solve this problem by automatically discovering classified data, tracking access patterns, and producing audit-ready reports that demonstrate ongoing compliance. Without this automation, compliance becomes a reactive nightmare that only triggers after a breach or audit notice arrives.
Financial damage extends far beyond fines
IBM’s 2024 report shows data breaches cost organizations an average of 4.88 million dollars per incident, but that figure masks significant variation. Breaches in the financial services sector average 5.9 million dollars, while healthcare breaches exceed 10.9 million dollars (when you factor in notification costs, legal fees, and customer trust erosion). The longer a breach remains undetected, the worse the damage-breaches identified within 200 days cost substantially less than those discovered after 200 days. DSPM tools reduce detection time dramatically by continuously monitoring data access and flagging unusual behavior before attackers exfiltrate sensitive information. Organizations using automated data discovery and classification catch problems weeks or months earlier than those relying on manual processes.
Visibility gaps create cascading risks
Most organizations struggle to answer basic questions about their data landscape. Where does sensitive customer information actually reside? Which employees or third parties can access regulated data? How does data move between cloud services, on-premises systems, and SaaS applications? These gaps (especially in multi-cloud environments where 89% of enterprises now operate) create opportunities for attackers and compliance violations. Manual audits can’t keep pace with data that constantly shifts across platforms.
Automated discovery and classification tools surface these risks in real time, allowing your team to act before problems escalate into costly incidents.
Detection speed determines financial impact
The difference between catching a breach in one week versus three months translates directly to millions of dollars in avoided costs. Attackers typically spend weeks inside a network before detection occurs, which means faster visibility saves money and protects reputation. DSPM solutions monitor data access patterns continuously, alert teams to suspicious behavior immediately, and enable rapid response before data leaves your environment. This proactive approach transforms security from a reactive expense into a strategic investment that protects your bottom line.
What to Actually Look for in a DSPM Tool
Real-Time Discovery Across All Your Data
A DSPM tool lives or dies based on whether it gives you real answers about your data landscape right now, not theoretical possibilities. The best tools discover data across your cloud providers, on-premises systems, and SaaS applications simultaneously, then classify what they find with enough accuracy that you can actually trust the results. Sentra achieves classification accuracy above 95 percent, which matters because false positives waste your team’s time investigating non-issues while false negatives leave real vulnerabilities undetected.
Your DSPM tool must identify structured data in databases, unstructured data scattered across file servers and cloud storage, and shadow data that exists outside official channels. Real-time discovery matters more than periodic scans because data changes constantly-files get shared, permissions shift, new sensitive information arrives daily. Tools like Cyera and Varonis track these changes continuously, alerting your team when a file containing customer payment information suddenly becomes accessible to a contractor or when an employee downloads a spreadsheet with regulated health records. Without this continuous monitoring, you’re essentially taking snapshots of a moving target.
Risk Scoring That Reflects Actual Exposure
The tool must calculate risk scores that reflect actual exposure, not just data sensitivity. A file containing social security numbers locked behind multi-factor authentication and encrypted storage presents far less risk than an identical file shared publicly with view-only permissions. Gartner’s research emphasizes that effective DSPM combines data location, encryption status, access controls, and configuration to generate actionable risk rankings. This approach means your security team focuses remediation effort on the exposures that matter most, rather than wasting resources on low-threat findings.
Integration That Eliminates Silos
Integration with your existing security infrastructure determines whether a DSPM tool becomes a central part of your operations or remains an isolated system that nobody uses. The tool should connect to your identity and access management systems so it understands which users hold which roles and can enforce least-privilege access automatically. Varonis excels at this by integrating with Active Directory and other IAM platforms to revoke excessive permissions and suggest policy-aligned access changes.
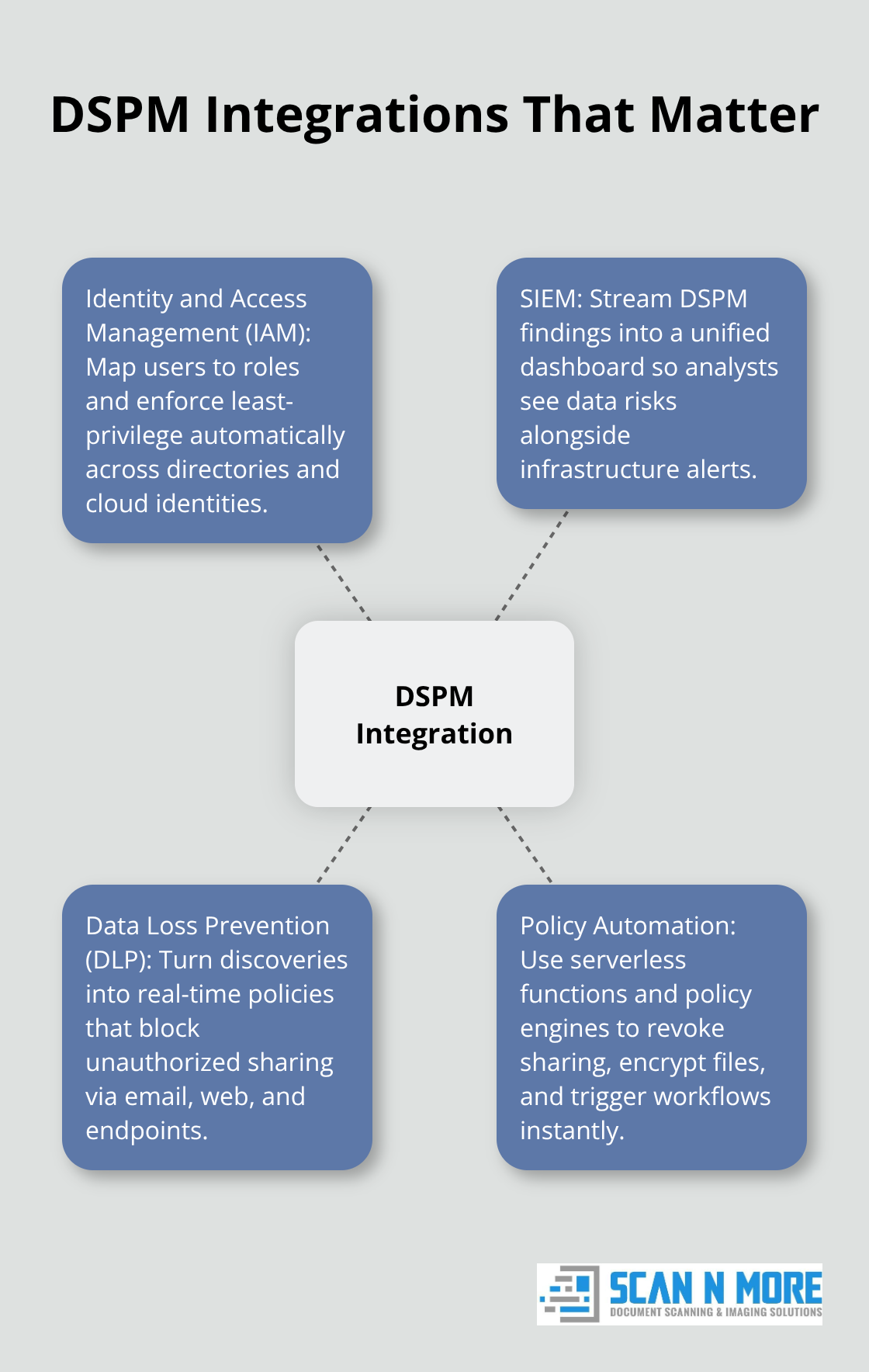
Your DSPM tool must feed findings into your security information and event management (SIEM) system so analysts see data-related risks alongside infrastructure alerts in one dashboard rather than switching between multiple tools. Integration with your data loss prevention (DLP) system ensures that DSPM discoveries trigger DLP policies that block unauthorized sharing across email, web, and endpoints. Tools like Sentra and Cyera provide these integrations out of the box, reducing implementation time and the likelihood that security teams ignore alerts because they come from yet another disconnected system.
Automated Remediation That Responds Immediately
Automated remediation capabilities determine whether your team spends hours executing manual fixes or whether the tool responds to discovered risks instantly. The tool should execute predefined workflows that revoke sharing permissions, encrypt sensitive files, or alert your legal team about regulatory data without requiring manual intervention. Open Raven and Laminar support this through serverless functions and policy engines that respond to discovered risks immediately rather than waiting for your team to review findings and decide what to do.
When your DSPM tool identifies that a contractor gained access to customer financial records, it should revoke that access in seconds, not days. When shadow data containing regulated information surfaces in an unsecured cloud bucket, the tool should encrypt it or move it to a compliant location automatically. This speed transforms your security posture from reactive to proactive, catching problems before they escalate into breaches that cost millions to remediate.
Getting Your Data Inventory Right Before DSPM Kicks In
Most organizations fail at DSPM implementation because they skip the foundational step of understanding what data actually exists in their environment. You cannot protect what you do not know about, and attempting to deploy a DSPM tool into an organization that has not mapped its data landscape creates chaos. Start with a thorough inventory across every system where data lives: cloud storage accounts, on-premises databases, SaaS applications, file servers, and backup systems. This inventory should identify not just what data exists, but where it sits, how old it is, and whether it remains actively used or abandoned.
Eliminate Redundant Data First
Many organizations discover that their stored data includes redundant, obsolete, or trivial information (what security teams call ROT data), which means you pay to store and protect information that serves no business purpose. Tools like BigID and Normalyze surface this shadow data and orphaned information that traditional audits miss entirely. Deleting ROT data before implementing DSPM reduces your attack surface immediately and makes the tool’s job easier by eliminating noise from your risk assessment.
Establish Policies Before Deployment
Once you know what data exists, establish clear policies about how different data types should be handled based on sensitivity level and regulatory requirements. Define which data requires encryption, who can access it, how long it should be retained, and what happens when employees leave or contractors finish projects. These policies become the rules that your DSPM tool enforces automatically, so vague guidelines guarantee implementation failure. Financial services companies operating under PCI DSS requirements must enforce strict separation between production and test environments, restrict administrative access to payment data, and log all access attempts. Your DSPM tool monitors compliance with these policies continuously, but the policies themselves must exist first.
Pilot Your Tool in One Department
Implementation speed matters less than getting the foundation correct. Many organizations rush to deploy DSPM tools across their entire infrastructure immediately, which creates alert fatigue when the tool surfaces thousands of misclassified files, overshared documents, and policy violations that teams lack capacity to remediate.
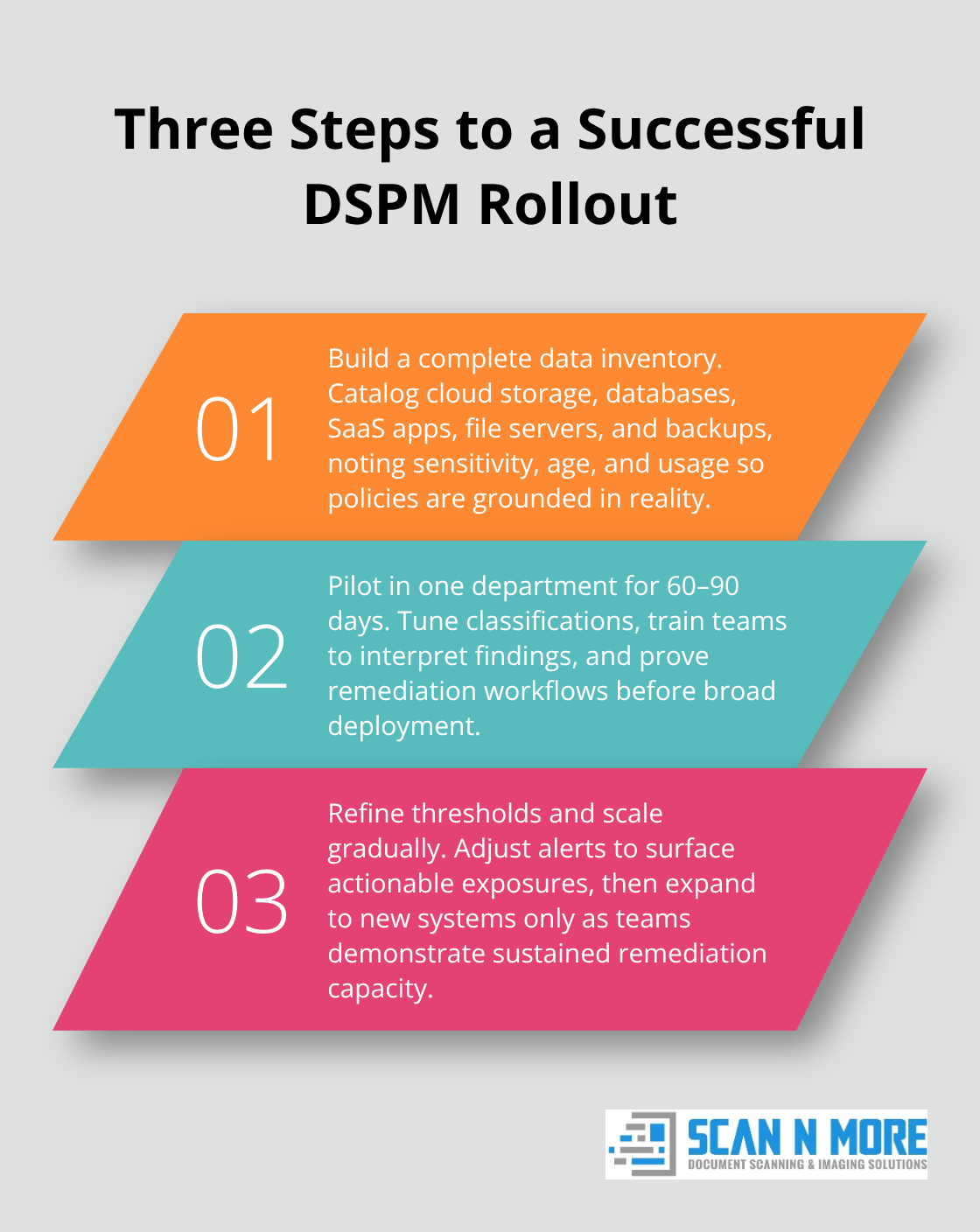
Instead, pilot your DSPM tool in a single department or business unit for 60 to 90 days. This approach lets your security and compliance teams refine your policies, train staff on how to interpret findings, and build remediation workflows that actually work before scaling to the entire organization.
Refine Thresholds and Scale Gradually
During this pilot phase, monitor how your team responds to alerts and adjust thresholds so you surface only exposures that require action rather than everything that technically violates policy. Sentra reports that customers achieve classification accuracy above 95 percent when they invest time in training the tool with examples from their own environment rather than relying on generic classifiers. After the pilot succeeds, expand gradually to additional systems and departments while continuously monitoring whether your security team can actually remediate findings at the pace the tool discovers them. This phased approach prevents the common failure mode where organizations deploy DSPM, get overwhelmed by findings, and abandon the tool because they lack resources to act on what it reveals. Your DSPM implementation succeeds when it becomes part of your normal security operations, not when you deploy the fanciest technology available.
Final Thoughts
DSPM tools solve a problem that manual processes cannot handle at scale, giving your organization real-time visibility into where sensitive data lives and who accesses it. Investing in data security posture management tools costs far less than responding to a breach that exposes customer information or violates regulatory requirements. Organizations that implement these solutions catch problems weeks or months earlier than competitors relying on periodic audits, which translates directly into millions of dollars saved in incident response costs and avoided regulatory fines.
As your organization grows and data spreads across more cloud providers, SaaS applications, and on-premises systems, manual oversight becomes impossible. Data security posture management tools scale with your infrastructure automatically, discovering and classifying new data without requiring your security team to expand proportionally. This efficiency compounds over time, allowing your team to focus on strategic security initiatives rather than spending endless hours gathering evidence for compliance audits or investigating data access requests.
Selecting the right tool requires honest assessment of your current environment and realistic evaluation of your team’s capacity to remediate findings. Start with a pilot deployment in a single department rather than attempting organization-wide rollout immediately, and consider how you’ll integrate document scanning and digitization into your overall data security strategy through services like Scan N More’s professional document scanning, which transforms paper-based processes into secure digital solutions while eliminating the security risks associated with physical document storage.
