Data breaches cost companies an average of $4.45 million per incident, according to IBM’s 2024 report. Most of these breaches happen because organizations lack a solid data security plan.
At Scan N More, we’ve seen firsthand how businesses struggle when they don’t have clear security strategies in place. This guide walks you through the three essential steps to build a data security plan that actually works.
Assess Your Current Data Security Posture
Map Every Location Where Your Data Lives
Start by mapping every location where your data resides. CrowdStrike’s 2024 Global Threat Report shows unauthorized access attacks increased 62% since 2022, and most attackers exploit gaps in visibility. You cannot protect what you don’t see. Walk through your systems and identify where customer information, financial records, and operational data sit. Check cloud storage accounts, local servers, backup systems, email archives, and even personal devices employees use for work. Many organizations store sensitive data in places nobody documented.
Once you have this inventory, categorize your data by sensitivity level. High-value customer information and financial records need stronger protections than general operational files. This classification directly shapes which security controls matter most.
Identify Gaps Between Current Defenses and Requirements
Conduct a formal security assessment to identify where your current security falls short. IBM’s 2024 Cost of a Data Breach Report found the average incident costs about $4.88 million. Companies with mature incident response plans reduce losses by roughly $1.2 million according to the Ponemon Institute’s research. The gap between your current defenses and regulatory requirements creates your priority list.
Check whether your access controls follow the principle of least privilege, meaning employees only access data required for their roles. Verizon’s 2024 Data Breach Investigations Report found 68% of breaches involve a human element like phishing or misuse of privileges, so weak access controls represent a major vulnerability. Examine your encryption practices for data at rest and in transit. Test your ability to detect suspicious activity in real time. Identify which systems lack multi-factor authentication. Document whether your incident response procedures exist and whether your team knows how to execute them. This honest assessment prevents you from wasting resources on controls that don’t address your actual weaknesses.
Build a Prioritized Roadmap from Assessment Findings
Turn your assessment into a prioritized roadmap. Address the highest-risk gaps first, focusing on the data that would cause the most damage if exposed. GDPR mandates breach notification within 72 hours, and similar timelines apply under other regulations, so your ability to detect and respond quickly matters enormously. Assign clear ownership for each security control and set realistic timelines for implementation.
Some fixes happen immediately, like enabling multi-factor authentication on critical systems. Others require longer planning, such as selecting and deploying new security tools. Document everything you find during this assessment phase, as this documentation becomes essential for compliance audits and demonstrates that you took security seriously. With your current posture mapped and priorities set, you’re ready to develop the security strategy and implementation plan that will actually close these gaps.
Build Your Security Strategy Around Real Data and Threats
Translate Assessment Findings Into Measurable Objectives
Your assessment revealed gaps. Now you need a strategy that closes them without wasting resources on tools that don’t match your actual risks. Translate your assessment findings into specific, measurable security objectives tied directly to the vulnerabilities you found. If your assessment showed weak access controls, your objective becomes implementing role-based access control within 90 days. If you lack real-time threat detection, your objective becomes deploying monitoring tools that alert on suspicious activity within 60 days. Avoid vague goals like “improve security” or “enhance protection.” These statements don’t tell you whether you succeeded.
Your objectives should answer three questions: what protection do you need, by when, and how will you measure success. Once objectives are clear, rank them by business impact. A breach affecting customer payment data causes more damage than a breach affecting internal memos, so prioritize accordingly. 60% of small companies go out of business within six months of falling victim to a data breach or cyber attack, which means your highest priorities must address the data that would cripple your business if exposed.
Select Tools That Match Your Actual Needs
Selecting the right tools matters, but tool selection should follow strategy, not drive it. Too many organizations buy expensive security platforms before understanding what problems they need solved. Instead, map each objective to specific capabilities you need. If you need to detect unauthorized data access, you need monitoring tools with behavioral analytics. If you need to enforce least-privilege access, you need identity and access management solutions with multi-factor authentication support. If you need to protect sensitive data across cloud and on-premises systems, you need encryption and data loss prevention tools.
Once you know what capabilities matter, evaluate tools against your actual environment and budget constraints. This approach prevents you from purchasing solutions that don’t address your real vulnerabilities or that your team cannot operate effectively.
Create Policies That Operationalize Your Strategy
Write policies that operationalize your objectives. Your access control policy should specify which employees access which data types, how access requests get approved, and how often access gets reviewed.
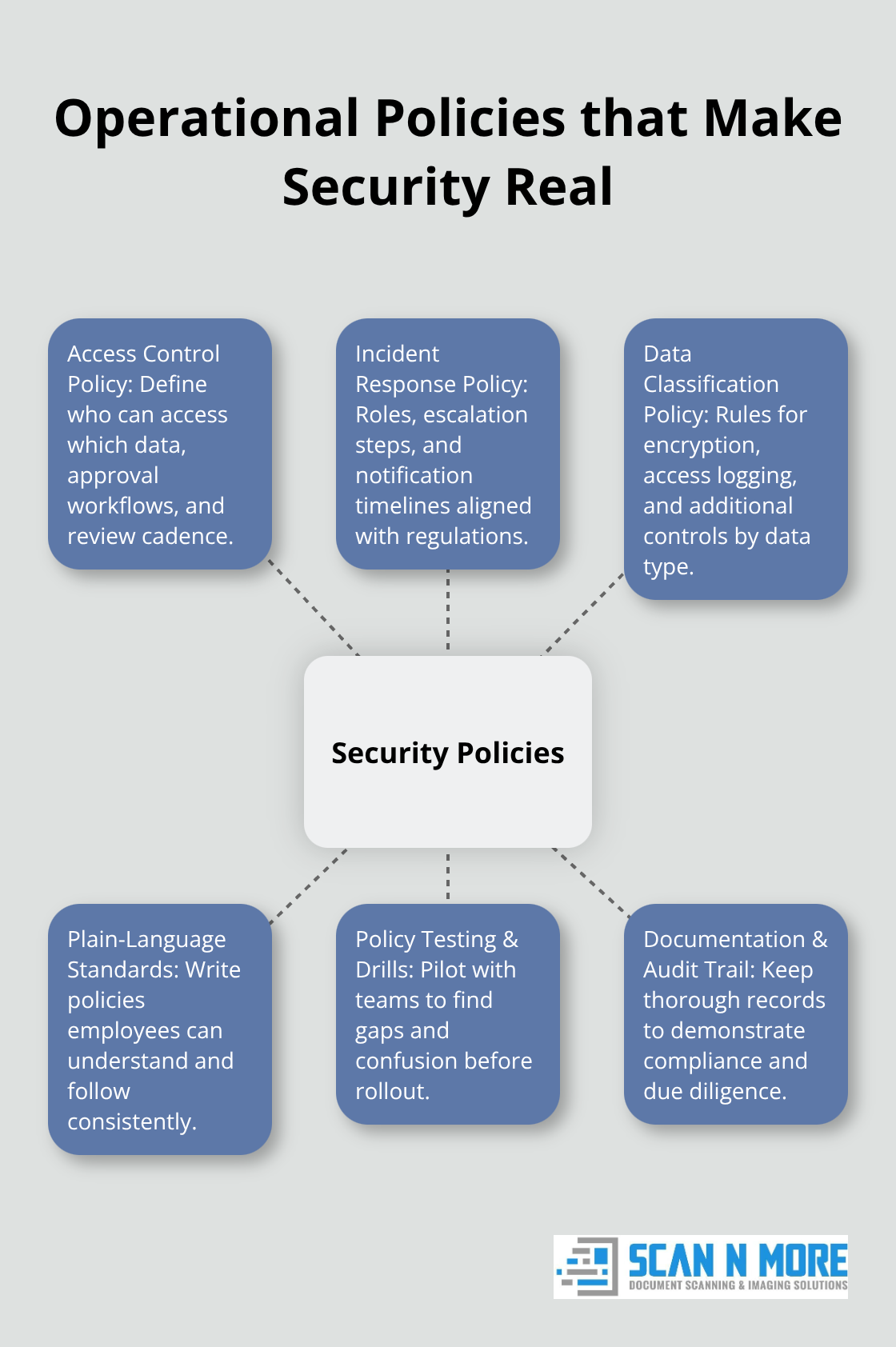
Your incident response policy should define who responds to breaches, escalation procedures, notification timelines aligned to GDPR’s 72-hour requirement and similar regulations, and how you document what happened. Your data classification policy should specify which data types require encryption, which require access logs, and which require additional controls.
Write these policies in language your team understands, not legal jargon. Test policies with your team before rolling them out to identify gaps and confusion. Document everything so compliance auditors see you took a structured, thoughtful approach to protecting data. With your strategy and policies in place, your next critical step involves preparing your team to execute these controls effectively.
Train Your Team and Monitor Compliance
Your team will either execute your security strategy or sabotage it. Verizon’s 2024 Data Breach Investigations Report found that 68 percent of breaches involve a human element, which means your policies mean nothing if employees don’t understand them or ignore them. Most organizations treat security training as a box to check, delivering annual compliance videos that people skip through. This approach fails. You need training that teaches employees why security matters to their specific roles and what happens when they get it wrong.
Build Role-Based Training That Sticks
Start with role-based training, not one-size-fits-all sessions. Your finance team needs to understand payment card security and phishing tactics targeting financial information. Your customer service team needs to recognize social engineering attempts. Your IT staff need to know how to patch systems and manage access controls. Training should take 20 to 30 minutes per quarter for most employees, not eight hours annually. Shorter, frequent sessions stick better than marathon training sessions.
Include real scenarios from your industry and your actual systems. Show your employees what a phishing email targeting your company looks like. Walk through your actual incident response procedures so people know who to call when something goes wrong. Run phishing simulations quarterly and track which employees click suspicious links. Those employees need additional coaching, not punishment. The goal is behavior change, not compliance theater.
Deploy Monitoring That Catches Real Threats
Deploy monitoring that catches real threats, not monitoring that generates false alarms your team ignores. Breakout time from initial access to lateral movement averages 48 minutes, which means you need detection systems that alert within minutes, not days. Configure your monitoring tools to flag unauthorized access attempts, unusual data downloads, and privilege escalation. Set baselines for normal activity in your environment, then alert when activity deviates significantly from those baselines.
Audit Access and Remove Unnecessary Permissions
Audit your access logs monthly to verify that employees only access data their roles require. If someone in accounting suddenly accesses customer payment card data, that’s an alert. If a departing employee still has active access 30 days after their last day, that’s a gap. Schedule quarterly reviews where managers confirm that their team members still need their current access levels. Remove access that’s no longer needed.
Document everything you find during these audits. This documentation proves to regulators and auditors that you actively manage access and catch problems before they become breaches. Update your policies when audits reveal that your current controls don’t match reality. If you discover that your backup systems aren’t being tested monthly, change your backup policy to require monthly testing and assign someone ownership of that task. If monitoring shows that certain data types are accessed far more frequently than expected, investigate why and tighten access controls if necessary.
Final Thoughts
Your data security plan only works if you treat it as a living document that evolves with your business and the threat landscape. Review your assessment findings quarterly to catch new vulnerabilities before attackers exploit them, and update your policies when monitoring reveals that employees struggle to follow current procedures or when new regulations impose stricter requirements. Document everything you do during this ongoing process, as this documentation demonstrates to auditors and regulators that you actively manage risk rather than hoping breaches won’t happen.
Start implementing your data security plan immediately, beginning with your highest-priority gaps. Don’t wait for perfect conditions or complete budget approval-address the vulnerabilities that would cause the most damage if exploited. As you digitize your operations and move sensitive data to new systems, partner with organizations that understand data security requirements and can help you transition processes safely while maintaining control over sensitive information.
We at Scan N More offer professional document scanning services with strong data security and compliance protections built into every step of the process. Your data security plan protects your business, your customers, and your reputation, so treat it as an investment that improves continuously.
