Enterprise data breaches cost companies an average of $4.45 million per incident, according to IBM’s 2024 report. That’s why selecting the right data security products matters more than ever for protecting your organization’s most sensitive information.
We at Scan N More understand that enterprises face mounting pressure to defend against evolving threats while maintaining compliance. This guide walks you through the essential features to look for, the top solutions available, and how to implement them effectively across your organization.
What Makes Enterprise Data Security Products Actually Work
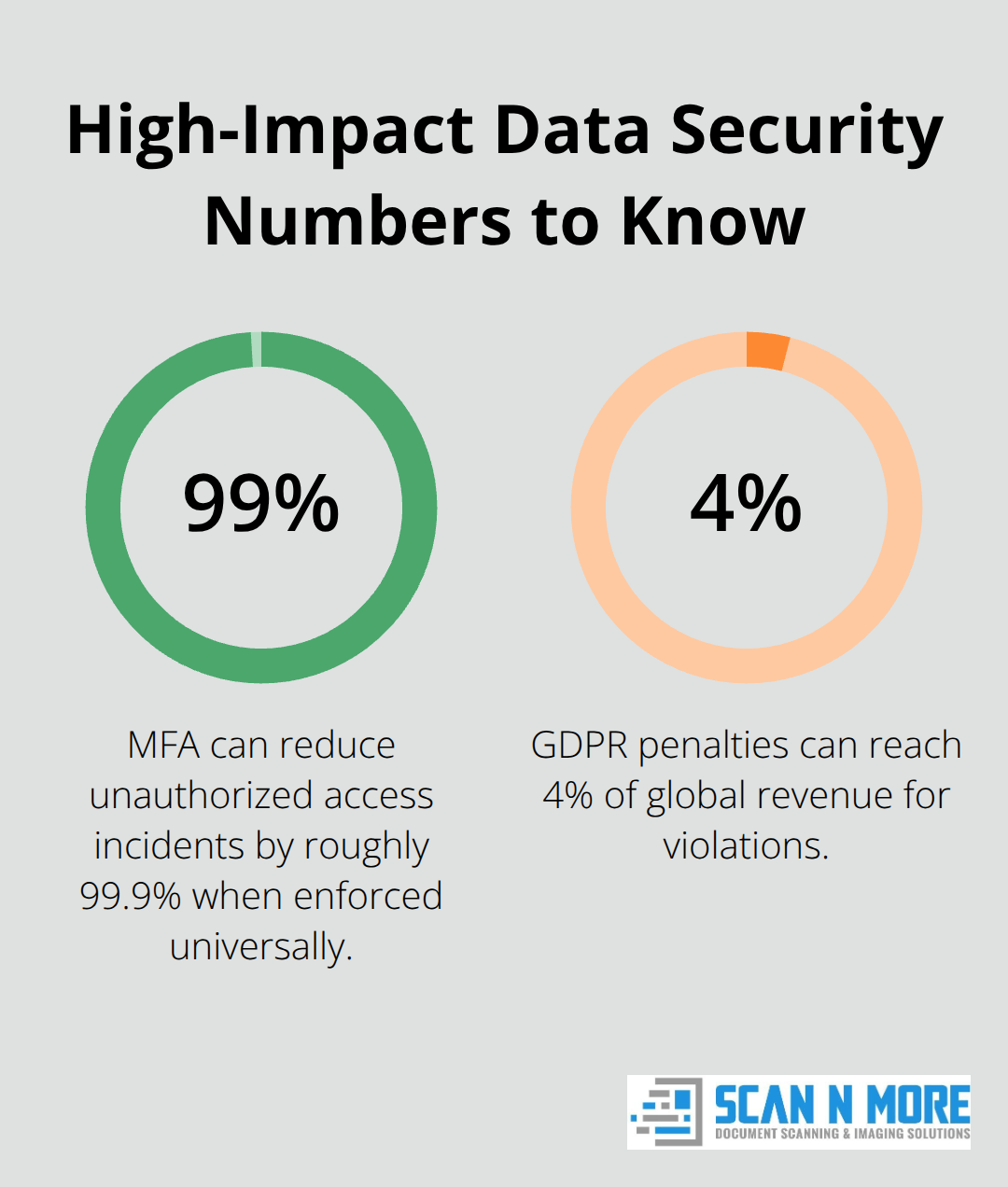
Encryption and access controls form the foundation of enterprise protection, but most organizations implement them incorrectly. You need encryption at three distinct points: data at rest, in transit, and in use when employees access it. The mistake enterprises make is treating encryption as a one-time deployment rather than an ongoing process tied to key management. Strong key management means rotating encryption keys regularly, restricting who can access them, and auditing every key use. Access controls should implement multi-factor authentication across all endpoints-not just email systems. According to research on data breach patterns, organizations using MFA reduce unauthorized access incidents by roughly 99.9%, yet fewer than half of enterprises enforce it universally. Role-based access control matters equally; when an employee changes departments, their access permissions should automatically adjust within hours, not weeks.
Detection Speed Separates Effective Products from Expensive Failures
Real-time threat detection systems must process massive volumes of activity to catch threats before they spread. Leading platforms like CrowdStrike Falcon process trillions of global events daily to identify patterns humans would miss. The critical capability here is behavioral analytics that flags anomalies-when a user downloads 500 files in 10 minutes or accesses systems at 3 AM from a new location, detection happens instantly. Automated response is non-negotiable; waiting for analysts to investigate means hours of exposure. Platforms that isolate infected endpoints immediately and quarantine suspicious files reduce breach impact substantially.
Threat detection latency matters enormously. A platform that detects malware in 30 seconds versus 30 minutes determines whether an attack affects one user or spreads across your entire network. Behavioral analytics identify threats that signature-based detection misses entirely. Fileless attacks and living-off-the-land techniques exploit legitimate system tools, so detection must recognize abnormal process chains and system behavior rather than just known malware signatures. Automated remediation-rolling back infected systems, isolating endpoints, and blocking malicious processes instantly-transforms detection from observation into actual defense.
Encryption Must Cover All Data States
Data at rest, in transit, and in use each require different encryption approaches. Organizations often encrypt databases but leave email attachments unprotected or fail to encrypt data on employee laptops. This fragmented approach leaves gaps attackers exploit constantly. Your encryption strategy should automatically classify data by sensitivity level, then apply appropriate encryption rules without manual intervention.
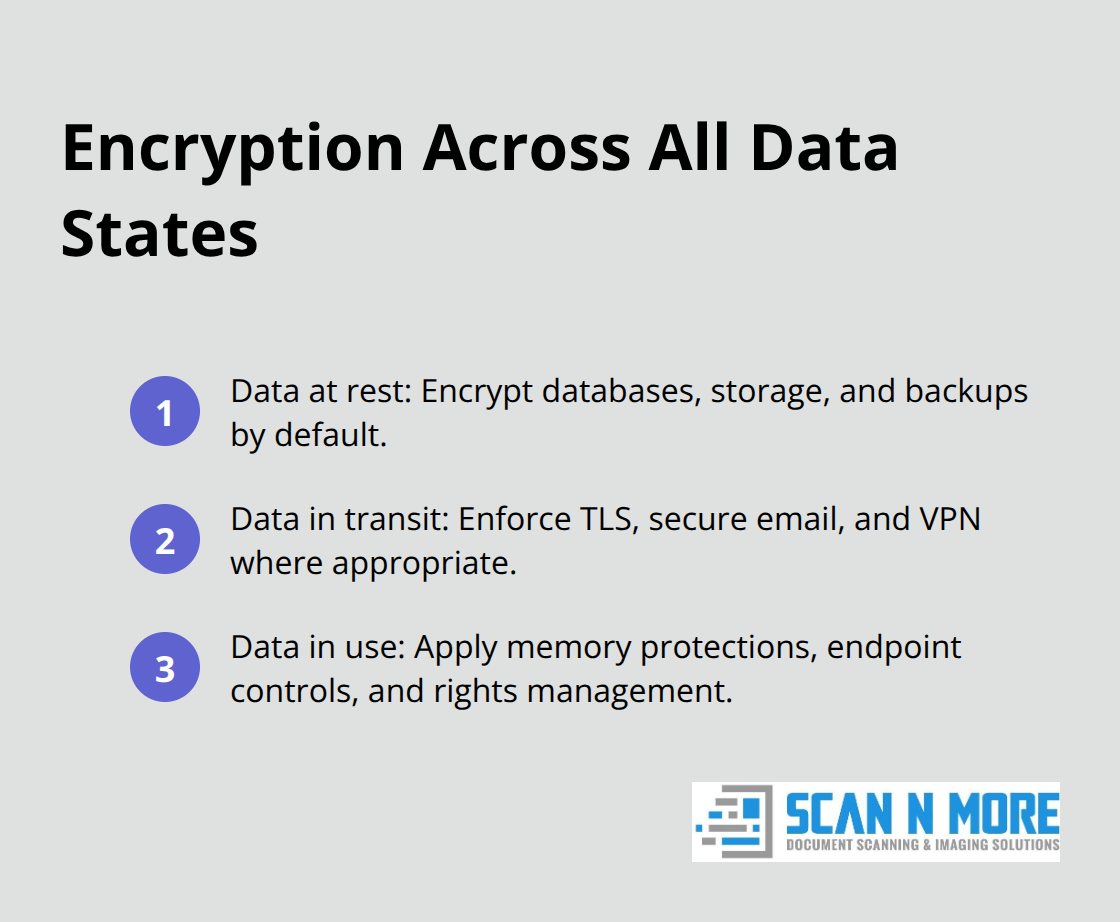
Tokenization for payment card data and format-preserving encryption for databases provide additional layers beyond standard AES-256 encryption. The reality is that encryption without strong access controls provides false security-an attacker with encryption keys gains full access.
Audit Trails Enable Real Compliance, Not Checkbox Compliance
Compliance and audit capabilities determine whether your security investments actually satisfy regulators. GDPR, HIPAA, and PCI DSS require documented proof that you control data throughout its lifecycle. Your data security product must generate audit logs automatically, track who accessed what data and when, and produce compliance reports without manual compilation. IBM’s 2024 data shows the average time to contain a breach is 277 days; platforms that enable rapid incident reconstruction cut this window significantly.
Regulators want evidence of control, not just policies. Your audit system must capture every data access, modification, and export event with timestamps and user identity. This data should remain immutable and retained according to regulatory requirements. Solutions that correlate audit logs with threat detection create incident timelines that satisfy auditors and support legal investigations. Compliance reporting should generate automatically rather than requiring weeks of manual data collection across disconnected systems. Look for solutions that integrate with your existing systems-SIEM platforms, endpoint detection tools, and identity systems-rather than creating isolated silos that generate alert fatigue and slow investigation. The right platform transforms your security infrastructure from fragmented point solutions into a cohesive defense that protects data at every stage while meeting regulatory obligations.
Enterprise Data Security Platforms That Actually Stop Breaches
Cloud-Based Security Platforms Lead Detection and Response
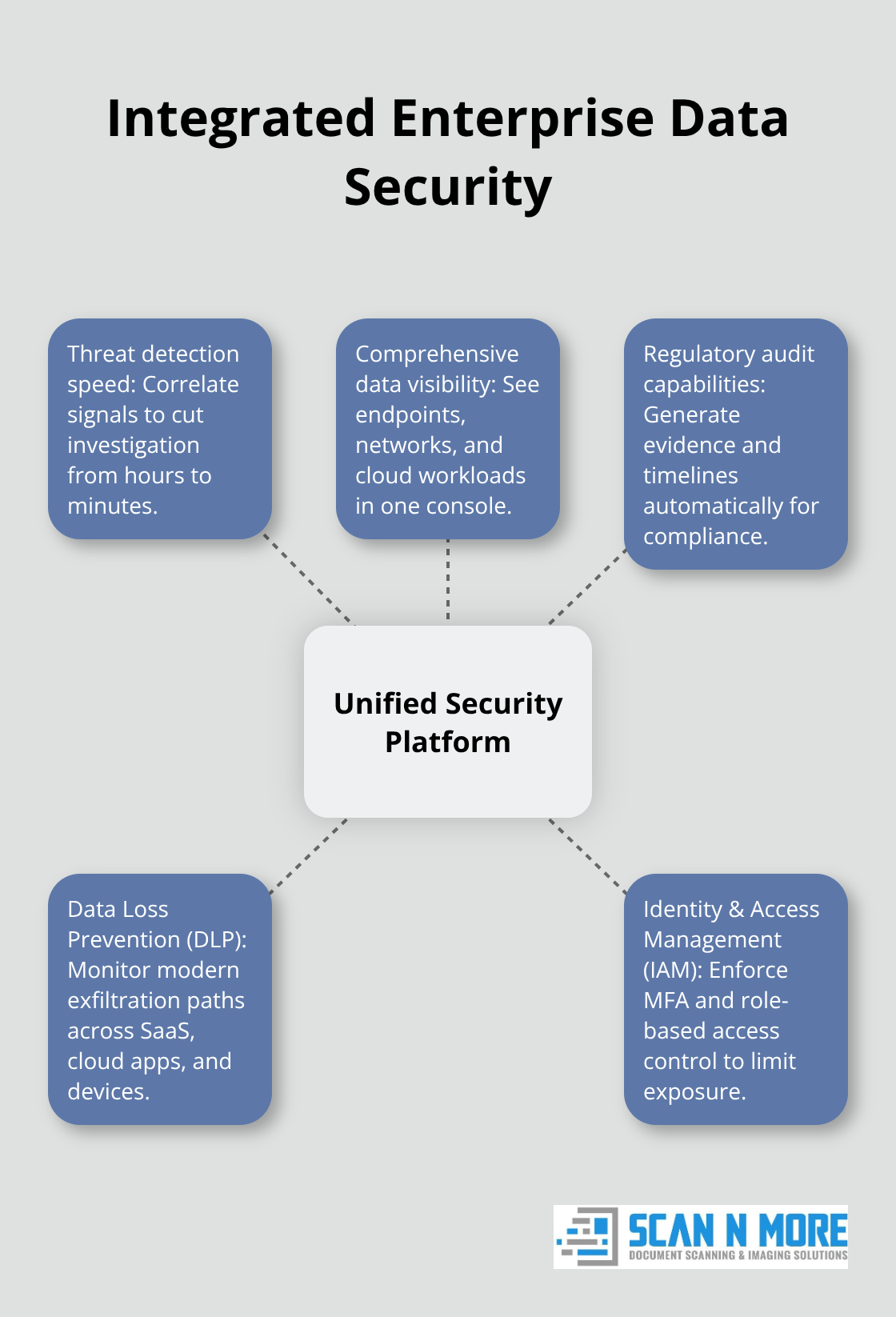
Enterprises need solutions that handle three overlapping problems simultaneously: stopping data exfiltration, maintaining visibility across cloud and on-premises systems, and generating audit evidence for regulators. The platforms that succeed accomplish all three without creating alert fatigue or requiring a security team the size of a small company. Cloud-based security platforms have become the default choice because they process threat data at scale without burdening internal infrastructure. CrowdStrike Falcon, Sophos Endpoint, and SentinelOne Singularity Endpoint lead Gartner Peer Insights rankings with ratings between 4.7 and 4.8 across thousands of customer reviews, reflecting real-world deployment success.
These platforms correlate signals from endpoints, networks, and cloud workloads in unified consoles, reducing investigation time from hours to minutes. When your security team can see all threats in one place rather than switching between five disconnected dashboards, response speed improves dramatically. Behavioral analytics catch what signature-based detection misses-a user accessing sensitive files at 2 AM from a new country, or downloading 50 GB of data in five minutes. Automated remediation isolates endpoints and blocks processes instantly, preventing widespread infection. Ransomware protection matters enormously for enterprises; some platforms offer seven-day system rollback capabilities that restore infected devices without paying attackers.
Data Loss Prevention Tools Must Monitor Modern Exfiltration Paths
Data loss prevention tools form the second critical layer, and they must monitor beyond email and USB drives. Modern DLP platforms track data moving through cloud applications, SaaS collaboration tools, and generative AI interfaces-areas where legacy DLP solutions provide zero visibility. Microsoft Purview DLP dominates Microsoft-heavy environments with strong coverage for Exchange, SharePoint, OneDrive, and Teams, though Teams chat DLP often requires expensive E5 licensing that inflates total cost of ownership.
Symantec DLP and Forcepoint DLP deliver broader channel coverage across networks, endpoints, and storage, but implementation demands substantial effort and ongoing policy tuning to reduce false positives. Proofpoint Enterprise DLP emphasizes people-centric protection by combining content inspection with insider-threat risk profiling, particularly valuable for regulated industries. The critical evaluation step involves auditing your actual data flows-where sensitive information lives, which applications employees use, and which exfiltration paths pose genuine risk.
Identity and Access Management Controls Who Reaches Data
Identity and access management systems complete the triad by controlling who reaches what data. Multi-factor authentication improves security by 45% with a reduction in unauthorized access risk when compared with single-factor authentication, yet fewer than half of enterprises enforce it universally. Role-based access control automatically adjusts permissions when employees change roles, preventing former department members from retaining access.
Integration across these three categories matters more than individual product excellence; a best-of-breed DLP platform isolated from your identity system creates blind spots that attackers exploit. The platforms winning enterprise deployments combine threat detection speed, comprehensive data visibility, and regulatory audit capabilities into cohesive solutions rather than forcing security teams to stitch together incompatible point products. Your next step involves assessing which vulnerabilities pose the greatest risk to your organization’s specific data and operations.
Getting Your Data Security Implementation Right
The hardest part of enterprise data security isn’t selecting products-it’s deploying them without breaking your operations or overwhelming your team. Most enterprises fail during implementation because they treat it as a technology problem when it’s fundamentally an organizational one.
Map Your Data Before You Buy Anything
Start with your actual data flows rather than assumptions about where sensitive information lives. Document which applications handle customer data, payment information, or intellectual property. Which systems connect to the internet? Which databases store regulated information? This inventory takes two to three weeks for most enterprises but prevents months of wasted spending on solutions that don’t address your real vulnerabilities.
The inventory process forces you to confront uncomfortable truths-legacy systems still processing sensitive data, shadow IT applications employees use without approval, databases with no encryption. These discoveries shape which products actually matter for your organization. A platform that excels at cloud data protection won’t help if your biggest vulnerability is unencrypted databases on aging servers.
Test Before Full Deployment
Proof-of-concept with your top three candidates prevents expensive mistakes. Test the platform with 50 to 100 employees across different departments for four to six weeks. This reveals integration friction with your existing systems, the actual false-positive rate when applied to your specific workflows, and whether your security team can operate it without drowning in alerts.
Many enterprises discover during POC that a platform generates thousands of daily alerts, creating investigation paralysis rather than protection. The vendor’s lab environment looks perfect; your environment with legacy systems, custom applications, and 15 years of accumulated data behaves differently. A platform that requires 40 hours weekly of policy tuning and alert investigation doesn’t protect you-it consumes your security team’s time without reducing breach risk.
Select Solutions Based on Operational Reality
Brutal honesty about what your team can actually manage determines success. Microsoft Purview DLP works well for Microsoft-centric organizations because it integrates natively, but Teams chat DLP requires E5 licensing that costs substantially more than the base product. Forcepoint DLP delivers superior risk-adaptive capabilities but demands significant implementation effort and ongoing tuning. Cheapest doesn’t mean best, and most feature-rich doesn’t mean most operationally sustainable.
Your team’s capacity matters more than feature lists. A solution that fits your actual workflows and staffing levels protects you far better than an overcomplicated platform that your team resents and circumvents.
Train Your Team and Define Processes
Comprehensive training combined with phased rollout reduces post-deployment friction compared to big-bang deployments, according to Gartner’s implementation research. Assign a dedicated security champion in each department who understands the tools and answers user questions rather than forcing all questions to your central security team.
Document your actual security protocols before deployment-how employees report suspicious activity, how long incident investigation takes, what compliance evidence you need to generate monthly. Most organizations skip this step and discover they lack defined processes once the platform goes live. Phased deployment prevents catastrophic failures; deploy to one department, let them stabilize for two weeks, then expand. This approach takes longer but identifies problems at scale before they affect your entire organization.
Integrate Across Your Security Stack
Your data security platform must connect with existing systems rather than creating isolated silos. Integration with SIEM platforms, endpoint detection tools, and identity systems transforms fragmented point solutions into cohesive defense. When your security team can see all threats in one place rather than switching between five disconnected dashboards, response speed improves dramatically.
The platforms winning enterprise deployments combine threat detection speed, comprehensive data visibility, and regulatory audit capabilities into solutions that work with your infrastructure rather than against it. Start implementing your data security plan immediately, beginning with your highest-priority gaps. Your next step involves assessing which vulnerabilities pose the greatest risk to your organization’s specific data and operations.
Final Thoughts
Enterprise data security requires sustained commitment, not one-time purchases. The data security products and strategies outlined above work only when you implement them with realistic expectations about your organization’s capacity and actual vulnerabilities. Your investments succeed when they integrate seamlessly with existing systems, reduce alert fatigue rather than amplifying it, and enable your team to respond faster than attackers can spread.
IBM’s research shows breaches cost $4.45 million on average, with containment taking 277 days. A platform that detects threats in minutes instead of weeks prevents exponential damage expansion. Compliance violations add regulatory fines on top of breach costs; GDPR penalties reach 4% of global revenue, HIPAA violations cost $100 to $50,000 per record, and PCI DSS non-compliance triggers merchant account termination. Prevention costs far less than remediation.
Your immediate next step involves assessing which vulnerabilities pose the greatest risk to your organization’s specific data and operations. Start with your highest-priority gaps rather than attempting comprehensive overhaul simultaneously. Scan N More provides professional document scanning services with guaranteed data security and compliance, transforming paper records into protected digital assets while maintaining the security standards your enterprise demands.
