In today’s digital landscape, businesses face an ever-growing array of threats to their sensitive data. At Scan N More, we understand the critical importance of robust data security solutions for protecting your company’s most valuable assets.
From sophisticated cyber attacks to insider threats, the risks are numerous and constantly evolving. This blog post explores essential measures and advanced technologies that modern businesses can implement to safeguard their data and maintain customer trust.
What Are the Biggest Data Security Threats?
The Rising Tide of Ransomware Attacks
Ransomware attacks surged dramatically in 2024, both in frequency and sophistication. Cybercriminals have increasingly targeted high-value organizations. These attacks not only result in financial losses but also cause significant operational disruptions. Organizations must implement robust backup systems and provide comprehensive employee training to combat this growing threat.
Insider Threats: The Enemy Within
While external attacks often dominate headlines, insider threats pose a significant risk to data security. These threats can be malicious or accidental, highlighting the need for strict access controls and continuous monitoring of user activities.
Supply Chain Vulnerabilities Exposed
As businesses become more interconnected, supply chain attacks have emerged as a major concern. The SolarWinds attack targeted several government agencies and corporations in the United States in 2020, demonstrating the far-reaching consequences of these attacks. Companies must thoroughly vet their vendors and implement stringent security measures across their entire supply chain.
The Ever-Evolving Threat Landscape
Cyber threats constantly shift, with attackers developing new techniques to bypass security measures. Organizations must remain vigilant and adapt their security strategies continuously. This adaptation includes the use of advanced technologies (such as AI-powered threat detection) and the adoption of a zero-trust security model.

Securing Document Management in the Digital Age
In the realm of document management, data security remains paramount. Secure scanning processes and robust data handling protocols protect sensitive information throughout the digitization process. Organizations that prioritize these security measures can focus on their core business while ensuring the safety of their documents and data.
As we explore the landscape of data security threats, it becomes clear that a comprehensive approach to protection is essential. In the next section, we will examine the critical data security measures that modern businesses must implement to safeguard their valuable information assets.
How to Build a Fortress Around Your Data
At Scan N More, we understand that protecting your data requires a comprehensive security strategy. This chapter outlines key measures to create a robust defense for your business information.
Fortify Your Access Points
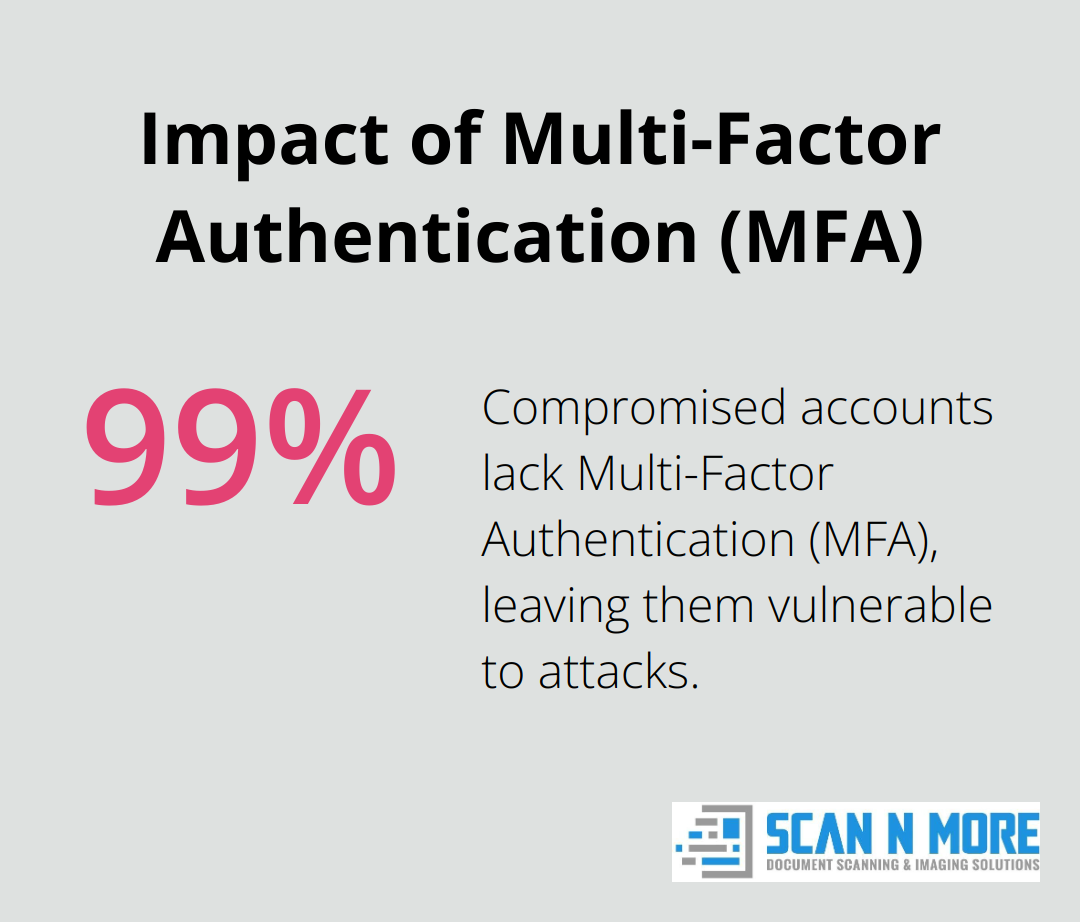
The first line of defense in data security is to control who can access your information. Implement multi-factor authentication (MFA) across all systems. A Microsoft study shows that more than 99.9% of compromised accounts don’t have MFA, which leaves them vulnerable to password spray, phishing, and password reuse. Use role-based access control (RBAC) to limit employees’ access to only the data they need for their specific job functions.
Encrypt Everything, Everywhere
Encryption acts as armor for your data. Apply end-to-end encryption for all data in transit and at rest. The National Institute of Standards and Technology (NIST) recommends AES-256 bit encryption as a strong standard. The AES algorithm is capable of using cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits. Don’t overlook mobile devices and removable storage – they need encryption too.
Conduct Regular Security Check-Ups
Your security measures must stay up-to-date. Schedule regular security audits and vulnerability assessments. The Payment Card Industry Data Security Standard (PCI DSS) requires quarterly vulnerability scans for businesses handling credit card data. Go beyond this requirement and conduct comprehensive annual audits to identify and address potential weaknesses in your security infrastructure.
Transform Your Employees into Security Assets
Your staff can become your most valuable defense. Implement a robust security awareness training program. Make training interactive and ongoing (not just a one-time event). Use simulated phishing attacks to keep employees alert and measure the effectiveness of your training.
Secure Your Document Management
In the digital age, document management security is paramount. Implement secure scanning processes and robust data handling protocols to protect sensitive information throughout the digitization process. This approach allows organizations to focus on their core business while ensuring the safety of their documents and data.
As we move forward, it’s essential to explore advanced data security solutions that can further enhance your protection against evolving cyber threats. The next chapter will introduce cutting-edge technologies and strategies to stay ahead in the ever-changing landscape of data security.
How Advanced Tech Protects Your Data
Cloud Security: Beyond the Buzzword
Cloud adoption continues to surge, necessitating a comprehensive cloud security strategy. Organizations should implement Cloud Access Security Brokers (CASBs) to monitor and control cloud usage. CASBs function as security intermediaries between cloud users and cloud-based applications, enforcing security policies and preventing data leaks.
Cloud-native security tools integrate seamlessly with chosen platforms. For example, Amazon Web Services (AWS) offers GuardDuty, a threat detection service that continuously monitors for malicious activity and unauthorized behavior.
AI and ML: Your Round-the-Clock Security Team
Artificial Intelligence (AI) and Machine Learning (ML) revolutionize threat detection and response. These technologies analyze vast amounts of data in real-time, identifying patterns and anomalies that human analysts might overlook.
AI-powered SIEM systems correlate data from multiple sources and detect sophisticated attacks. IBM’s QRadar SIEM uses multiple layers of AI and automation to enhance alert enrichment, threat prioritization, and incident correlation.
Blockchain: Data Integrity Assurance
Blockchain technology offers powerful data integrity solutions beyond its association with cryptocurrencies. Its immutable ledger system verifies the authenticity and integrity of sensitive documents, making it ideal for industries like healthcare and finance.
Blockchain-based systems for supply chain management ensure product authenticity and prevent counterfeiting. Walmart successfully used blockchain to trace the origin of food products, reducing tracking time from 7 days to 2.2 seconds.
Zero Trust: Verify Everything
The Zero Trust model assumes no user, device, or network should receive trust by default, even if they’re already inside the security perimeter. This approach proves essential in today’s distributed work environments.
Micro-segmentation divides networks into small, isolated zones. This limits an attacker’s ability to move laterally if they breach one segment. Tools like Cisco’s Software-Defined Access automate policy enforcement across networks.
Advanced Document Security
Modern document management requires robust security measures. Advanced scanning technologies incorporate state-of-the-art encryption and access controls to protect sensitive information throughout the digitization process. This approach ensures that even during the transition from physical to digital formats, data remains secure and compliant with industry regulations.

Final Thoughts
The landscape of cybersecurity evolves rapidly, making proactive data security measures essential for business survival. Organizations must implement robust data security solutions to protect against external attacks and insider threats. These solutions should enhance operational efficiency while maintaining stringent security measures.
We anticipate several trends will shape the future of data security, including increased adoption of zero-trust architectures and cloud-based security solutions. Quantum computing advancements will necessitate new encryption standards, while increased regulatory scrutiny will likely lead to more stringent compliance requirements. These factors make comprehensive data security strategies even more critical for businesses.
Scan N More offers professional scanning services that ensure a seamless transition from paper-based processes to digital solutions. Our services prioritize data security and compliance throughout the digitization process. Businesses that partner with experts in document digitization and data protection can focus on their core operations while maintaining high standards of information security.

