Data breaches cost companies an average of $4.45 million in 2023, making robust data governance and security non-negotiable for modern businesses.
We at Scan N More understand that protecting sensitive information requires more than basic password protection. Organizations need comprehensive frameworks that combine strict governance policies with advanced security measures.
The right approach transforms data from a liability into a strategic asset while maintaining regulatory compliance.
What Makes Data Governance Actually Work?
Strong data governance starts when you assign specific owners to every data asset in your organization. Data ownership must have decision-making authority over their assigned datasets, including who can access the information and how it gets used. This person should be a business stakeholder, not an IT professional, because they understand the data’s business context and impact. Organizations that skip this step face endless finger-pointing when data problems arise.
Data Quality Standards That Actually Matter
You need measurable data quality standards to prevent the chaos that destroys business decisions. Establish specific thresholds for completeness, accuracy, and consistency that align with your business needs. For example, customer data should maintain high completeness for critical fields like email addresses and phone numbers. Companies that use automated data quality monitoring tools see faster issue resolution times. Quality standards must include validation rules, standardized formats, and regular monitoring schedules. Without these concrete measures, your data governance program becomes meaningless paperwork.
Smart Data Classification Systems
Data classification forms the backbone of effective governance when you categorize information based on sensitivity and business value. Start with four basic categories: public, internal, confidential, and restricted. Each category needs specific handling procedures, access controls, and retention policies. Organizations that use automated classification tools reduce manual effort while they improve accuracy. Classification must happen at the point of data creation, not as an afterthought. This systematic approach allows you to apply appropriate security controls and compliance measures based on actual risk levels rather than guesswork.
Access Control Framework Implementation
You must establish role-based access controls that limit data exposure to authorized personnel only. Research from IBM’s reports shows that compromised user credentials remain a major factor in successful data breaches, making access management your first line of defense. Create user groups based on job functions and assign permissions accordingly (following the principle of least privilege). Regular access reviews help identify orphaned accounts and excessive permissions that create security vulnerabilities. This framework becomes the foundation for your security protocols and authentication systems.

How Do You Build Bulletproof Data Security?
Data security requires multiple defense layers that work together to protect your organization from sophisticated attacks. Multi-factor authentication reduces the risk of compromise by 99.22% across the entire population according to Microsoft research, which makes it your strongest first defense. You must implement encryption for data both at rest and in transit with AES-256 standards, which remains unbreakable by current computers. Network segmentation creates isolated zones that prevent attackers from lateral movement through your systems once they gain initial access. Deploy endpoint detection and response tools that monitor device behavior in real-time rather than rely on signature-based antivirus software that misses zero-day threats.
Authentication Systems That Actually Stop Intruders
Strong authentication goes beyond passwords to verify user identity through multiple factors. Biometric authentication with fingerprints or facial recognition provides the highest security level because attackers cannot steal or share these factors like passwords. Time-based one-time passwords through authenticator apps offer better protection than SMS codes (which attackers can intercept through SIM swaps). Implement conditional access policies that evaluate login attempts based on location, device, and behavior patterns to block suspicious activities automatically. Conduct quarterly access reviews to remove dormant accounts and excessive permissions that create unnecessary attack surfaces.
Security Testing That Finds Real Vulnerabilities
Vulnerability assessments must happen continuously rather than annually to catch new threats as they emerge. Penetration tests by external security firms provide unbiased evaluation of your defenses and identify weaknesses that automated tools miss. Database activity monitors generate real-time alerts when unusual queries or access patterns occur, which helps you detect insider threats and compromised accounts. Security information and event management systems correlate data from multiple sources to identify attack patterns that individual tools might overlook. Organizations that conduct regular vulnerability scans experience fewer successful attacks compared to those with infrequent schedules.

Real-Time Threat Detection
Modern threats require immediate response capabilities that traditional security tools cannot provide. User behavior analytics detect abnormal data access patterns through machine learning algorithms that adapt to new attack methods. Data loss prevention systems inspect data across various states (at rest, in motion, and in use) to prevent unauthorized access and usage. Automated threat response systems can isolate compromised systems within seconds of detection, which limits damage from successful breaches. These advanced detection methods become the foundation for comprehensive compliance and risk management strategies.
How Do You Stay Compliant Without Breaking Your Budget?
Regulatory compliance starts when you map your specific requirements against industry standards like GDPR, HIPAA, SOX, and CCPA rather than implement generic policies that miss critical obligations. GDPR fines have reached significant levels according to European data protection authorities, which proves that regulators actively enforce penalties against non-compliant organizations. You must conduct annual risk assessments that identify data types, process activities, and potential compliance gaps within your current systems. Organizations that maintain compliance matrices track regulatory changes and see fewer violations compared to those that use outdated frameworks. Create automated compliance monitors that flag policy violations in real-time rather than discover problems during audits when penalties become unavoidable.
Response Plans That Actually Work
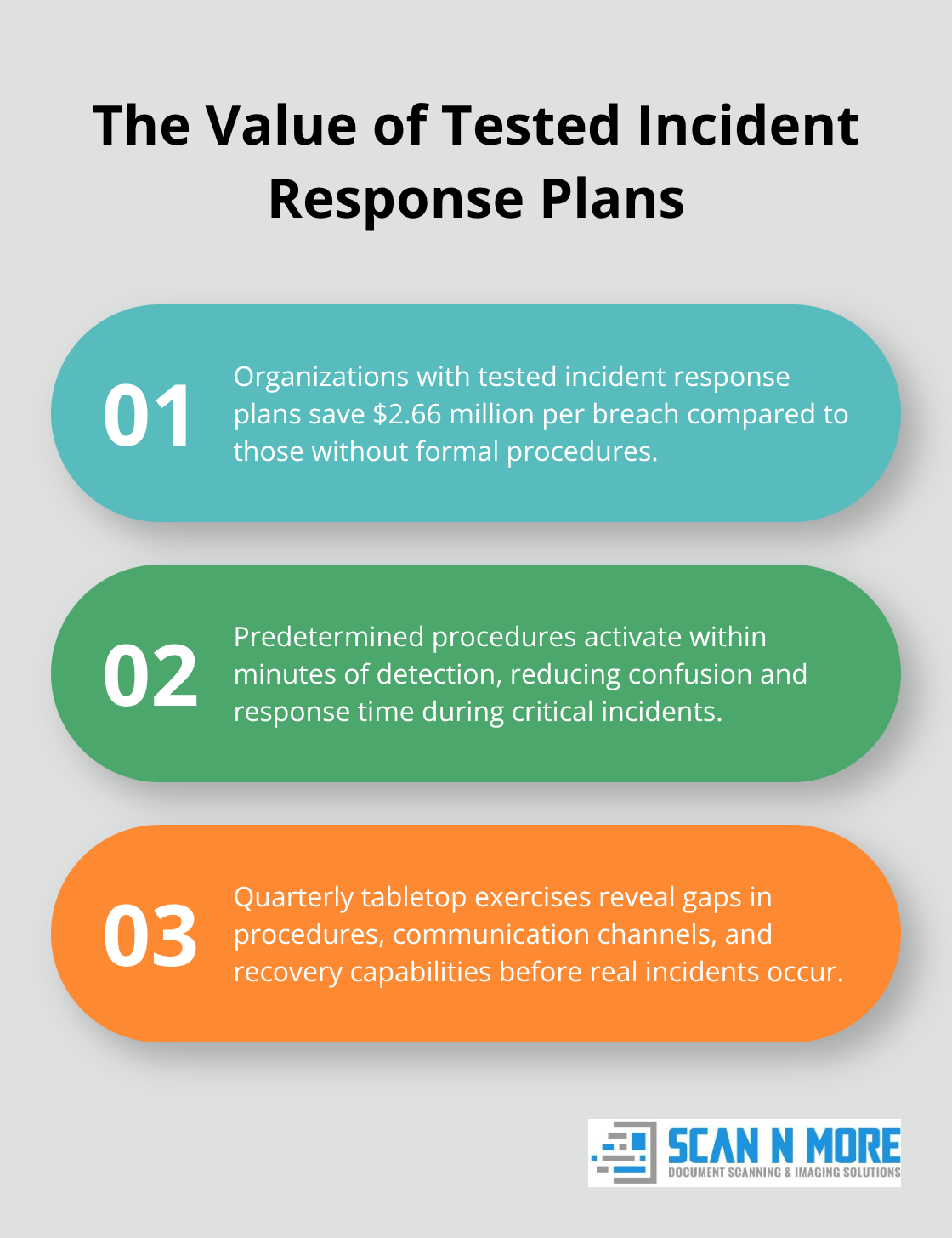
Data breach response requires predetermined procedures that activate within minutes of detection, not hours of confusion about next steps. Your incident response team needs specific roles for legal counsel, IT security, communications, and executive leadership with clear escalation paths and decision-making authority. Organizations with tested incident response plans save $2.66 million per breach compared to those without formal procedures. Document notification requirements for each jurisdiction where you operate because GDPR requires reports within 72 hours while state laws vary significantly. Test your response plans quarterly through tabletop exercises that reveal gaps in procedures, communication channels, and recovery capabilities before real incidents expose these weaknesses.
Documentation That Survives Audits
Audit documentation must demonstrate continuous compliance oversight rather than scrambled evidence collection when regulators arrive at your door. Maintain detailed logs of data processing activities, access controls, policy changes, and security incidents with timestamps and responsible parties clearly identified. Automated audit trails capture user activities, system changes, and data movements without manual intervention that creates gaps or inconsistencies in your records. Organizations that use centralized documentation platforms reduce audit preparation time while they improve accuracy of compliance reports. Your documentation system should generate compliance reports automatically and store evidence in tamper-proof formats that regulators accept as valid proof of your governance activities.
Risk Assessment Frameworks
Risk assessments must evaluate both technical vulnerabilities and business impact to prioritize your security investments effectively. Conduct quarterly assessments that examine new data sources, system changes, and emerging threats rather than rely on annual reviews that miss critical developments. Organizations that use standardized risk scoring methodologies (like NIST frameworks) achieve more consistent results across different departments and time periods. Document risk mitigation strategies with specific timelines and responsible parties to track progress and demonstrate due diligence to auditors. Your risk assessment process should integrate with incident response plans to activate appropriate countermeasures when threat levels exceed acceptable thresholds.
Final Thoughts
Effective data governance and security demands three fundamental elements: clear ownership structures, comprehensive security protocols, and continuous compliance oversight. Organizations that assign specific data owners experience 40% fewer governance failures compared to those with unclear accountability structures. Your security framework must combine multi-factor authentication, encryption, and real-time detection to create multiple defense layers against sophisticated attacks.
Security-first culture requires employee threat recognition training while automated systems prevent human error. Regular vulnerability assessments and incident response testing transform reactive security into proactive protection. Companies with tested response plans save millions during actual breaches.
Implementation begins with data classification and risk assessment, followed by access control deployment and compliance documentation. Organizations that transition from paper-based processes can partner with professional document scanning services to digitize records securely while they maintain governance standards. Success depends on executive sponsorship, employee education, and continuous improvement of your data governance and security frameworks.
