Data breaches cost companies an average of $4.45 million in 2023, according to IBM’s Cost of a Data Breach Report. Most organizations still lack proper protection against cyber threats.
We at Scan N More understand that implementing data security best practices requires a systematic approach. This guide covers the essential technologies, strategies, and compliance requirements your business needs to protect sensitive information effectively.
What Security Threats Target Your Business Data
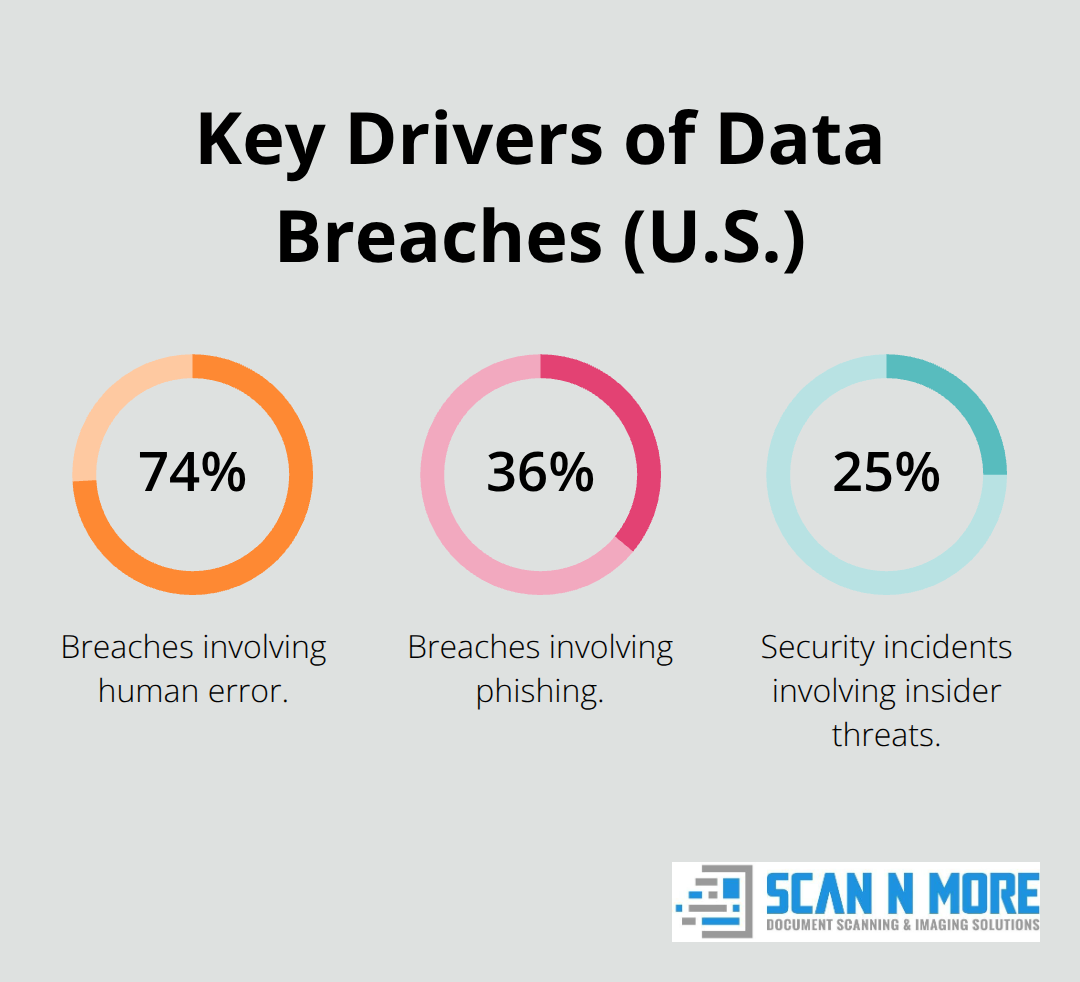
Ransomware attacks increased by 41% in 2022, with Verizon’s Data Breach Investigations Report showing that 74% of breaches involve human error. Phishing remains the top attack vector and affects 36% of all data breaches, while insider threats account for 25% of security incidents according to the Ponemon Institute. Advanced persistent threats now target small and medium businesses more aggressively, with attackers who spend an average of 287 days inside networks before detection.
SQL injection attacks still compromise 19% of web applications, despite basic coding practices that prevent them.
Vulnerable Systems That Attackers Exploit Most
Outdated software creates the biggest security gaps in business environments. Microsoft reports that threat actors increasingly use AI to exploit vulnerabilities in today’s landscape. Misconfigured cloud storage exposed 22 billion records in 2023 alone (with Amazon S3 buckets as the most common target). Remote access tools like VPNs suffer from weak authentication protocols, which allow attackers to bypass network security in 43% of remote work breaches. Legacy systems that run Windows Server 2008 or older operating systems face 5 times more security incidents than updated infrastructure.
Financial and Operational Damage From Data Breaches
Healthcare organizations pay the highest breach costs at $10.93 million per incident, while financial services average $5.90 million according to IBM’s latest research. Companies lose 3.7% of their annual revenue on average after a major data breach, with stock prices that drop 7.5% within six months. Regulatory fines compound the damage (GDPR penalties reached €1.2 billion in 2023 across European companies). Ransomware groups now specifically target application databases, encrypt critical business data, and demand payments that exceed $1 million. Recovery time averages 287 days to identify and contain a breach, during which businesses lose customers at a rate 36% higher than normal operations.
These threats make it clear why organizations need robust security technologies and methods to protect their data assets effectively.
Which Technologies Actually Stop Data Theft
AES-256 encryption stands as the gold standard for data protection at rest, capable of using cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits. Organizations must encrypt database files, backup storage, and all sensitive data repositories. Implementation quality matters more than the algorithm itself. 99% of cloud security failures will be the customer’s fault by 2025, primarily due to misconfigurations, not platform vulnerabilities.
Multi-factor authentication reduces account compromise by 99.9% according to Microsoft’s security team, yet only 22% of organizations enforce MFA across all systems. Role-based access controls work best when administrators limit user permissions to specific time windows and IP ranges, not just job functions.
Backup Systems That Survive Ransomware Attacks
The 3-2-1 backup rule saves businesses during ransomware attacks, but most companies skip the offline component that provides real protection. Veeam’s 2023 Ransomware Trends Report shows that 85% of organizations with air-gapped backups recover within 24 hours, compared to 287 days for those without proper isolation.
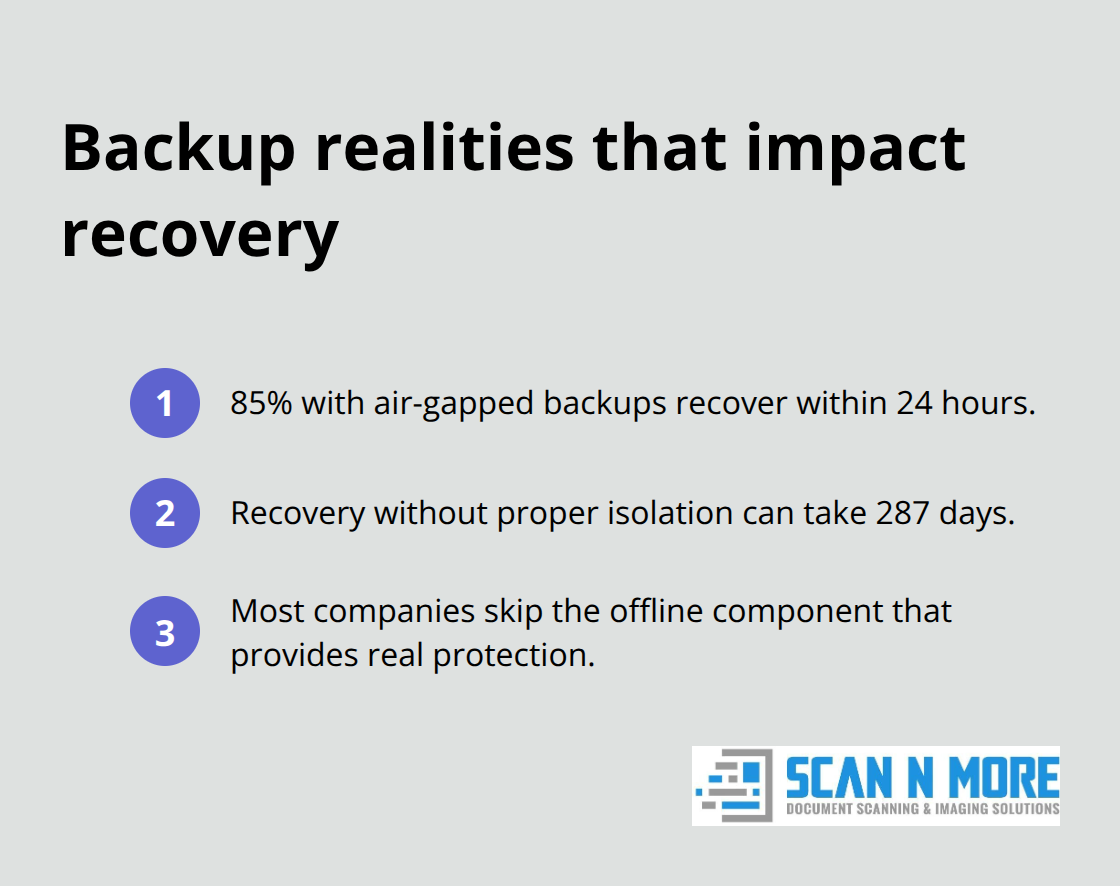
Immutable backups that use WORM technology prevent attackers from encryption of recovery data, though this requires storage systems that support write-once policies. Test your restore procedures monthly because 34% of backup systems fail during actual recovery attempts (according to Acronis research). Geographic replication protects against regional disasters, but latency increases to 150ms when backup sites exceed 1,000 miles from primary locations.
Network Defenses That Block Advanced Threats
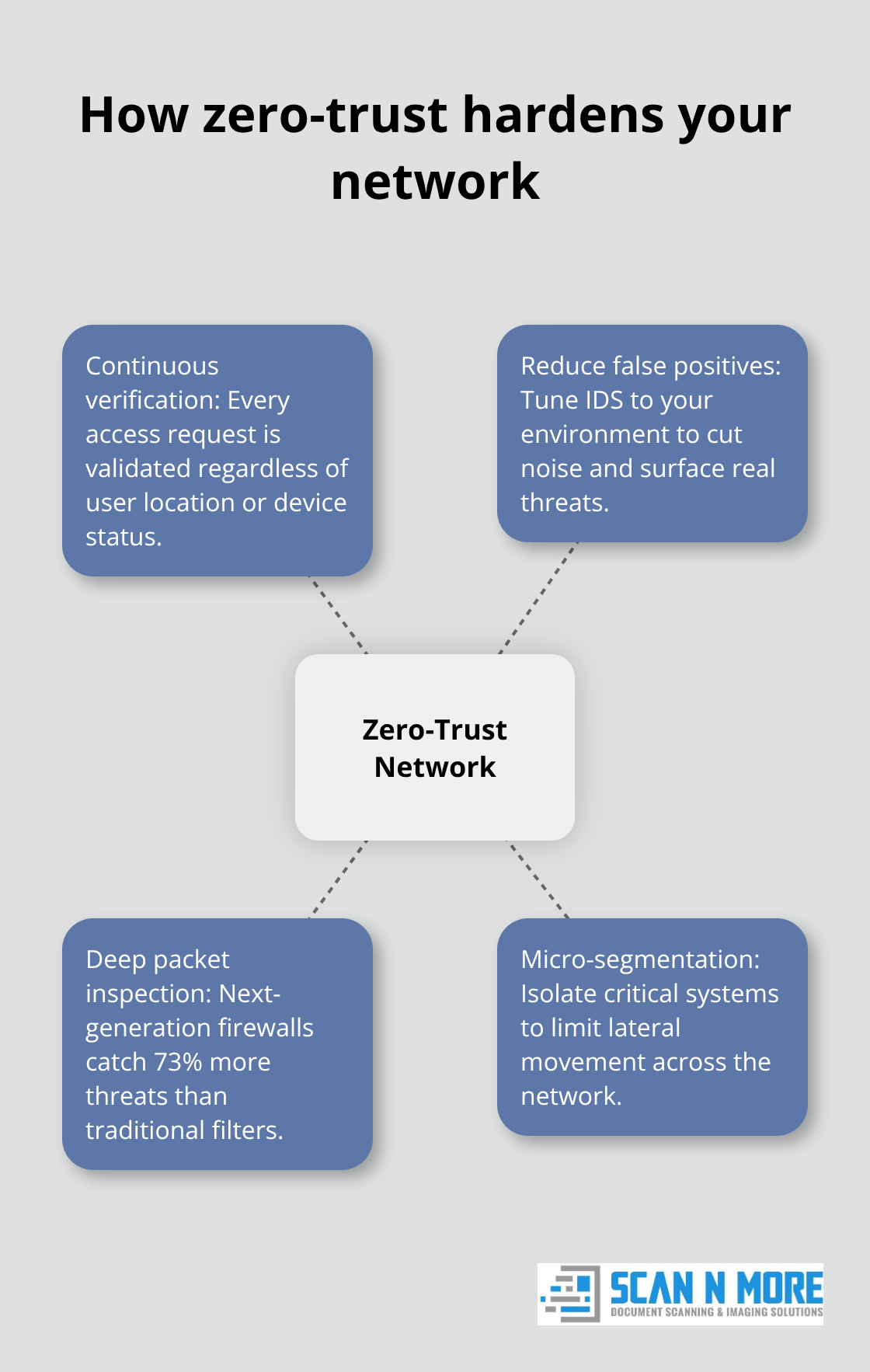
Next-generation firewalls with deep packet inspection catch 73% more threats than traditional port-based filters according to Fortinet’s Threat Landscape Report. Network segmentation limits breach damage through isolation of critical systems, though micro-segmentation works better than VLAN-based approaches for prevention of lateral movement.
Intrusion detection systems generate too many false positives unless security teams tune them for specific environments and traffic patterns. Zero-trust network architecture assumes every connection is hostile and requires verification for each access request regardless of user location or device status (this approach blocks 60% more unauthorized access attempts than perimeter-based security).
These technical foundations create the framework for comprehensive security strategies that address both technology and human factors in data protection.
How Do You Build Security That Actually Works
Security audits reveal gaps that automated tools miss, yet many organizations conduct assessments only after incidents occur. Effective risk assessment starts with data classification that identifies your most valuable information assets and maps their storage locations across all systems. We recommend quarterly vulnerability scans combined with annual penetration tests that simulate real attack scenarios. Focus audit efforts on systems that handle financial data, personal information, and intellectual property because these targets generate the highest breach costs. Document every security control and test its effectiveness through red team exercises that attempt to bypass your defenses.
Risk Assessment Methods That Find Real Vulnerabilities
Start with asset inventory that catalogs all data repositories, applications, and network connections across your infrastructure. Classify data by sensitivity levels and map information flows between systems to identify potential exposure points. Conduct threat modeling sessions that examine how attackers might target your specific business processes and data types. Vulnerability assessments detect technical flaws, but manual reviews catch configuration errors and business logic weaknesses that automated tools miss. Prioritize remediation based on actual business impact rather than generic severity scores to reduce security debt effectively.
Employee Training Programs That Stop Human Error
Most breaches involve human elements, which makes security awareness training more critical than expensive security tools. Monthly phishing simulations can significantly reduce click rates within six months, but training must include current attack methods and real examples from your industry. Train employees to recognize social engineering tactics, verify unusual requests through separate communication channels, and report suspicious activities immediately. Regular training programs work best when integrated into onboarding processes and reinforced through quarterly updates that address emerging threats. Gamification increases participation rates and improves retention of security concepts compared to traditional classroom sessions.
Compliance Frameworks That Guide Implementation
Regulatory fines continue to increase across industries, making compliance frameworks essential for data protection. Choose compliance frameworks that match your industry requirements and data types rather than implementing generic standards that waste resources. SOC 2 audits take significant time but demonstrate data protection capabilities to customers and partners. ISO 27001 certification requires substantial investment but provides comprehensive security management structure for organizations that need structured approaches. NIST Cybersecurity Framework offers practical guidance without mandatory certification costs, making it ideal for businesses that need security structure without regulatory overhead.
Final Thoughts
Data security best practices require a systematic approach that combines technology, processes, and human awareness. AES-256 encryption, multi-factor authentication, and network segmentation form the technical foundation, while regular risk assessments and employee training address human vulnerabilities. Organizations that invest in comprehensive security strategies see average returns of 1.6x on their privacy investments (according to Cisco research).
Start with data classification to identify your most sensitive information, then implement encryption for data at rest and in transit. Deploy backup systems with air-gapped storage and conduct monthly restore tests. Train employees through regular phishing simulations and establish clear incident response procedures.
Strong data security delivers measurable business benefits beyond compliance. Companies with robust security programs experience 36% fewer customer losses after incidents and maintain higher stock valuations. Scan N More helps organizations implement secure digital document management solutions that reduce physical vulnerabilities while maintaining compliance standards.

