Data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 report. A comprehensive data security assessment is your first line of defense against these threats.
At Scan N More, we’ve seen firsthand how organizations that skip assessments end up scrambling after a breach. This guide walks you through each step of conducting a thorough evaluation of your security posture.
What Actually Happens During a Data Security Assessment
A data security assessment isn’t a checkbox exercise or a single audit you complete once and forget. It’s a systematic examination of how your organization handles, protects, and manages sensitive information across all systems and processes. The assessment identifies where data lives, who can access it, what controls protect it, and what happens when those controls fail. IBM’s 2024 report found that organizations detected breaches in an average of 277 days, which means vulnerabilities often sit undetected for months. A proper assessment compresses that timeline by forcing you to look at the entire landscape intentionally rather than reactively.
You map every database, application, cloud storage service, and third-party integration that touches your data. You examine access controls to see if employees still have permissions they no longer need. You test whether encryption is actually enabled on sensitive information or just configured in theory. You verify that your incident response plan actually works when pressure is on, not assuming it does because it exists in a document somewhere.
Why assessments matter more than compliance checkboxes
Organizations often conflate assessments with compliance audits, but they’re fundamentally different. A compliance audit verifies you meet specific regulatory requirements like HIPAA or PCI-DSS. An assessment identifies actual security gaps regardless of what regulations require. The distinction matters because regulations lag behind real threats. A company can pass a compliance audit and still suffer a breach from an attack vector the regulations don’t address.
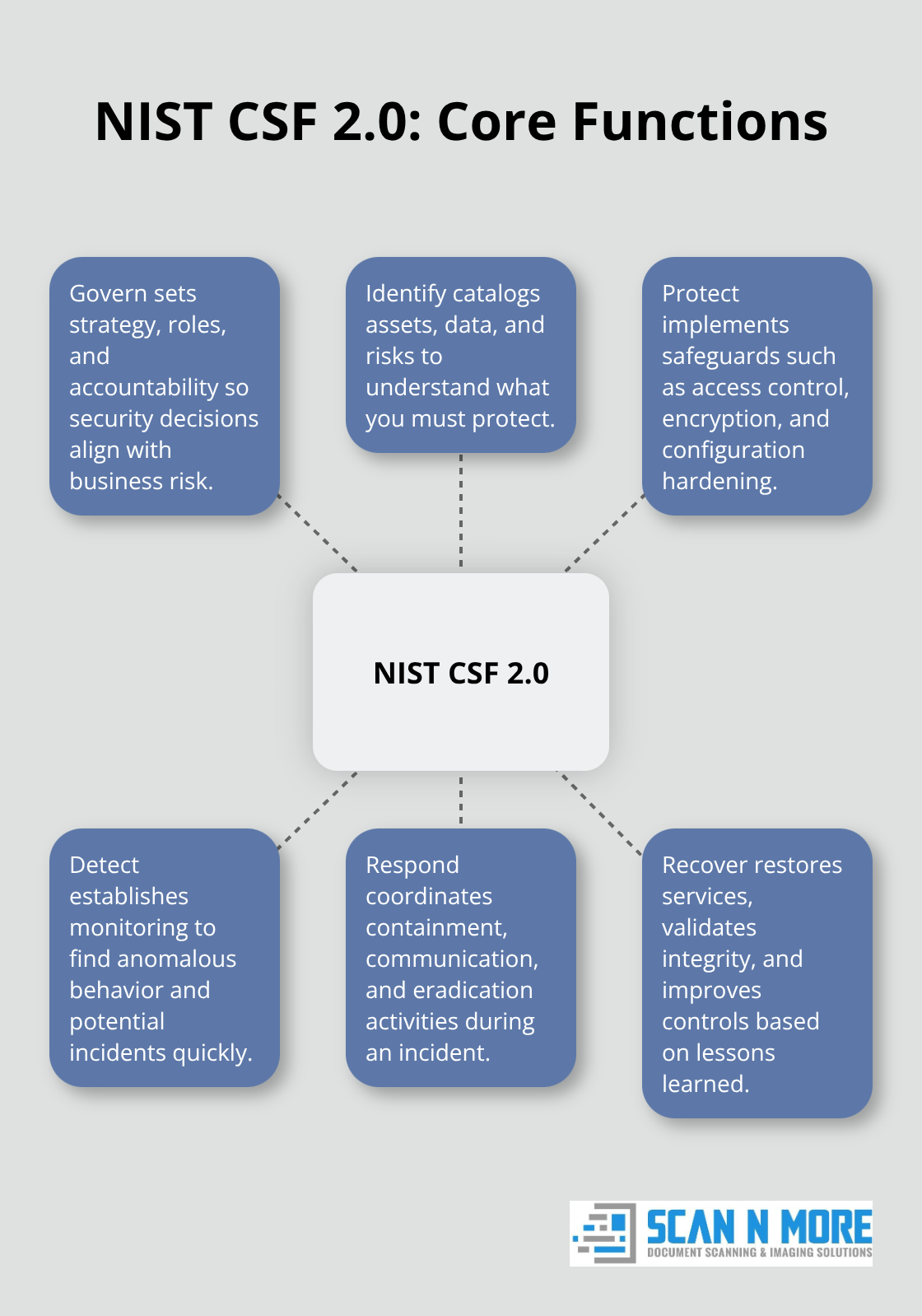
Assessments should be continuous and risk-focused rather than annual events. The NIST Cybersecurity Framework 2.0 provides structure for assessments across organizations of all sizes, emphasizing this ongoing approach through its six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. These functions aren’t meant to execute once but repeat cyclically as threats evolve. When you conduct an assessment using this framework, you establish a baseline for measuring improvement and catch new threats as they emerge.
Building your assessment scope with what actually matters
Most organizations fail at assessments because they either scope them too narrowly or too broadly. Scoping too narrow means you miss critical vulnerabilities in systems you didn’t think were important. Scoping too broadly overwhelms your team and produces a report so large nobody acts on it.
Start with data classification. Identify what data you have, categorize it by sensitivity, and determine which systems store or process that sensitive data. A healthcare provider doesn’t need to assess the same controls on a public-facing blog that they need on systems handling electronic health records. This targeted approach means you allocate resources where they actually reduce risk.
Identify third-party connections because external dependencies introduce risk you don’t directly control. If your CRM vendor suffers a breach, your customer data is compromised regardless of your internal controls. The assessment must account for these external touchpoints. Finally, align your scope with regulatory requirements specific to your industry. HIPAA for healthcare, PCI-DSS for payment processing, and GDPR for EU customer data each impose different control requirements. A comprehensive assessment incorporates all applicable frameworks so you avoid regulatory gaps.
Moving from scope to execution
With your scope defined, you’re ready to move into the actual assessment work. The next chapter walks you through the step-by-step process of conducting your evaluation, from inventorying assets to documenting findings in a format that drives action.
Conducting Your Data Security Assessment Step-by-Step
Map Every System That Touches Your Data
Create an exhaustive inventory of where your data actually lives, not where you think it lives. Most organizations discover during assessment that data exists in places nobody documented: old shared drives, personal cloud accounts, archived systems still connected to the network, and API integrations with third-party tools. You must map every database, application server, cloud storage bucket, backup system, and external service that touches sensitive information. Data breach detection delays reveal that organizations often lack visibility into all systems storing their data. Automated discovery tools scan your network and identify data repositories, then manual validation through interviews with department heads confirms what systems actually store sensitive information. Document the data owner for each system, the type of data stored, how long it remains, and who holds access. This inventory becomes your foundation for everything that follows.

Evaluate Controls and Identify Vulnerabilities
Next, evaluate the actual security controls protecting each system and identify vulnerabilities through multiple methods. Access your systems and verify that encryption actually functions on sensitive data, not just sits configured but inactive. Check whether multi-factor authentication protects administrative accounts or if a single compromised password grants access to everything. Review access logs to spot unused accounts still holding permissions or contractors retaining access months after their work ended. Vulnerability scans using automated tools identify known weaknesses, but scanners miss misconfigurations and logical flaws that only manual review catches. Test your incident response plan through attack simulation to see whether your team detects it, responds appropriately, and recovers without chaos. NIST Cybersecurity Framework 2.0 recommends testing controls through realistic exercises rather than assuming they work in theory. Document each control, note what it protects, and record whether it functions properly or requires remediation.
Prioritize Vulnerabilities With a Risk Matrix
Finally, create a risk matrix that plots each vulnerability against two axes: likelihood of exploitation and potential business impact. A vulnerability in an internet-facing system handling payment data ranks higher than a similar vulnerability in an internal administrative tool. This matrix forces prioritization decisions rather than treating all vulnerabilities equally and overwhelming your team with a thousand low-impact items. With your assessment findings documented and prioritized, you now move into the critical phase of turning these insights into concrete action-determining which vulnerabilities demand immediate attention and which can wait, then building the roadmap to fix them.
From Risk Matrix to Action Plan
Turn Findings Into Concrete Fixes
Your risk matrix sits complete, vulnerabilities ranked from critical to low. Now most organizations make a fatal mistake: they treat the assessment report as a finished product rather than a starting point. The matrix is worthless if it doesn’t drive concrete action within weeks. You need an action plan that assigns ownership, sets realistic timelines, and allocates resources to actually fix things.
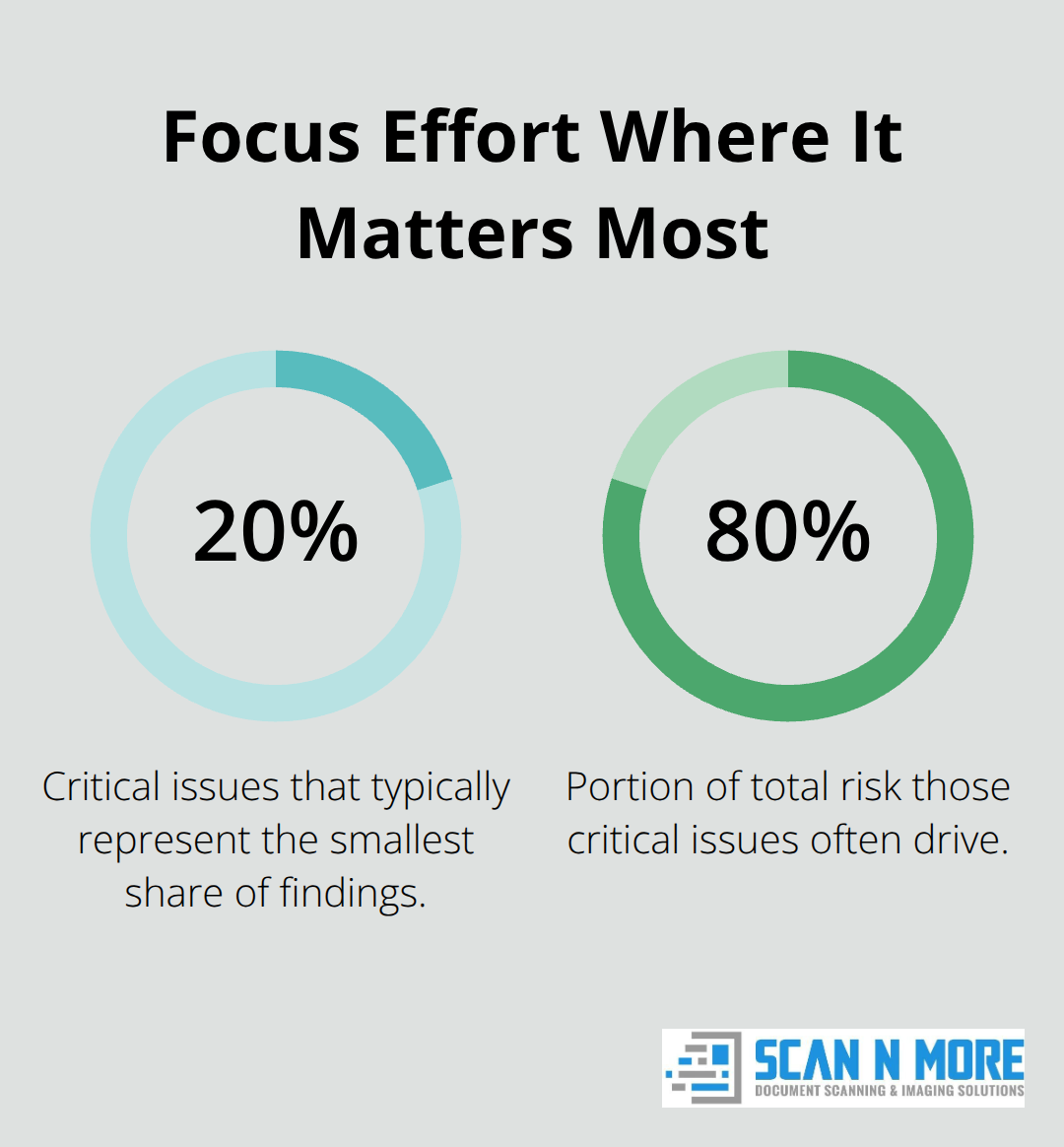
Start with critical vulnerabilities first, which typically represent 20% of the issues that account for 80% of your actual risk. A vulnerability in an internet-facing authentication system handling customer data demands a fix within 30 days. A misconfigured internal development server can wait 90 days. This ruthless prioritization prevents analysis paralysis and focuses your team’s energy where it matters most.
Assign Owners and Set Realistic Timelines
Assign a specific owner to each vulnerability, not a department. When you assign vulnerability remediation to “IT,” nobody fixes it. When you assign it to Sarah in infrastructure with a deadline and budget approval, it gets done. Set realistic timelines based on your team’s actual capacity, not wishful thinking. If your security team has two people and you’re asking them to remediate 200 vulnerabilities in three months while maintaining daily operations, you’ve created an impossible situation that guarantees failure. Build in buffer time for unexpected complications. A firewall rule change sounds simple until you discover a critical business application depends on the old configuration.
Monitor Continuously Rather Than Wait for Annual Reviews
Establish ongoing monitoring immediately rather than waiting for the next annual assessment. Organizations that wait 12 months between assessments miss new threats that emerge in weeks. Deploy continuous vulnerability scanning tools that run weekly or daily, not quarterly. Set up configuration monitoring that alerts you when security settings change unexpectedly, because insider threats and misconfigurations often happen between formal assessments. IBM’s 2023 data breach report showed organizations took 277 days to detect breaches, but that timeline compresses dramatically when you monitor continuously. Schedule quarterly reassessments of your highest-risk systems to catch new vulnerabilities quickly. This doesn’t mean running the full assessment again, but rather spot-checking critical systems and reviewing recent changes.
Track Progress With Metrics and Accountability
Create a metrics dashboard that tracks remediation progress and shows executives how many critical vulnerabilities remain open, how long they’ve been waiting for fixes, and what resources you need to accelerate closure. This visibility forces accountability and prevents the assessment report from disappearing into a filing cabinet. The NIST Cybersecurity Framework 2.0 emphasizes this continuous approach through its Govern function, which embeds security into ongoing enterprise risk management rather than treating it as an annual event. Your assessment becomes a living program that adapts as threats evolve and business changes, not a static report that sits unused.
Final Thoughts
A comprehensive data security assessment transforms your organization from reactive to proactive. You’ve mapped every system that touches your data, evaluated controls honestly, and built a risk matrix that forces prioritization. The assessment process itself reveals vulnerabilities that would otherwise sit undetected for months or years, and the real value emerges when you act on those findings with assigned owners, realistic timelines, and continuous monitoring that catches new threats before they become breaches.
Organizations that conduct regular assessments spend less money fixing problems after breaches occur and more strategically preventing them. Your team gains visibility into systems that previously operated in darkness, and executives understand actual risk rather than assuming everything is secure because compliance audits passed. Customers and partners trust you more when you demonstrate commitment to protecting their data through documented, ongoing security work.
As you digitize records and consolidate data during your assessment, handle sensitive documents securely throughout the transition. Scan N More provides professional document scanning services with data security and compliance built in, helping you move paper-based processes to digital while maintaining the protection standards your data security assessment identifies as necessary.

