Data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 report. At Scan N More, we know that implementing effective data security methods isn’t optional anymore-it’s a business requirement.
This guide walks you through the threats you face, the best practices that actually work, and the compliance standards you need to meet. You’ll find actionable steps to strengthen your security posture right away.
What Threats Target Your Data Right Now
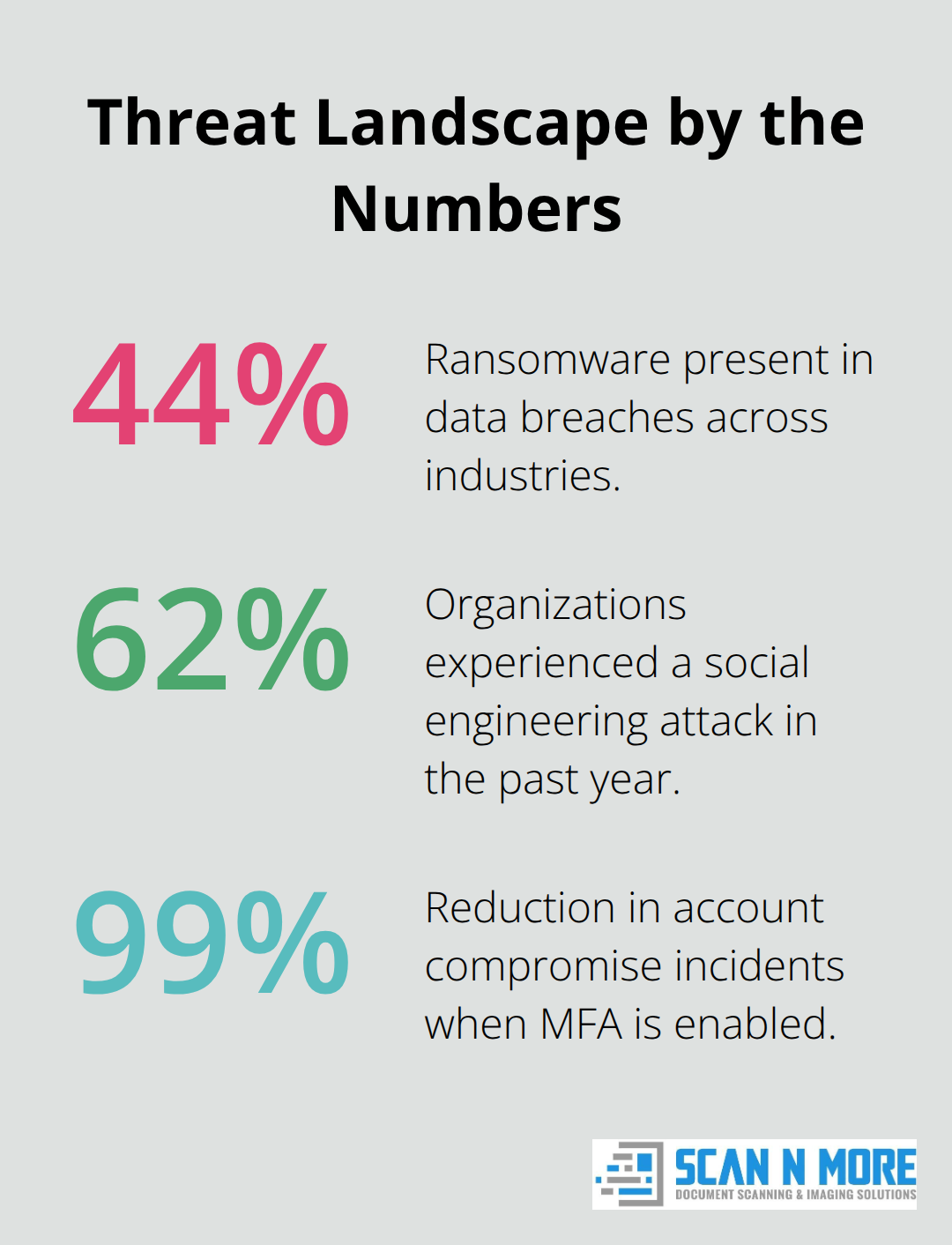
Ransomware attacks have become industry-wide problems, not edge cases. According to Verizon’s 2025 Data Breach Investigations Report, ransomware was present in 44% of breaches, a 37% increase compared to its 2024 report. The real damage extends beyond money: organizations lose operational continuity, customer trust, and sometimes entire business lines.
Malware operates differently-it installs itself on systems to steal data, monitor activity, or create backdoors for future attacks. These threats spread through unpatched software, weak credentials, and outdated systems.
Detection Gaps Give Attackers Months to Work
The median time organizations take to detect a breach is 207 days, according to IBM’s 2024 Cost of a Data Breach Report. This means attackers have months to extract sensitive information before anyone notices. Threat actors count on this detection gap-they move slowly, stay quiet, and extract data in small batches to avoid triggering alerts. Most organizations detect breaches through external notification rather than their own security tools, which reveals that current monitoring fails to catch what matters.
Companies using advanced behavioral analytics and automated alerting reduce Mean Time to Detect (MTTD) to under 30 days. You need real-time data-access monitoring with anomaly detection that flags unusual patterns like after-hours access, mass downloads from restricted directories, or access from unfamiliar locations. Endpoint detection and response (EDR) tools monitor process execution, file activity, and network connections to catch anomalies before encryption starts or data exfiltration begins.
Phishing and Social Engineering Exploit Human Behavior
Phishing remains the most cost-effective attack vector for criminals because it exploits human behavior rather than technical vulnerabilities. Threat actors send emails impersonating trusted contacts, vendors, or executives to trick employees into sharing passwords, clicking malicious links, or downloading infected attachments. Social engineering extends beyond email-attackers call employees pretending to be IT support, pose as new team members in Slack channels, or create fake login pages that capture credentials.
Deloitte research shows that 62 percent of organizations experienced a social engineering attack in the past year, yet many companies still rely on basic awareness training that fails to stick. Phishing simulations reveal that 15 to 25 percent of employees still click malicious links even after training. Layered email filtering combined with user behavior analytics catches both the emails and the risky clicks before damage occurs.
Unauthorized Access and Insider Threats
Unauthorized access happens when attackers exploit weak authentication protocols, default credentials, or compromised accounts to move laterally through networks and reach sensitive data repositories. Insider threats-whether malicious or accidental-account for a significant portion of breaches because employees have legitimate access that’s difficult to monitor without proper controls.
Privileged account monitoring is non-negotiable because compromised admin credentials give attackers full system access. Track every action taken by users with elevated permissions, enforce multi-factor authentication on all critical systems, and audit access quarterly to remove unnecessary permissions. The common denominator across all these threats is that organizations often lack visibility into where their data lives, who accesses it, and whether that access follows the principle of least privilege.
Understanding these threats sets the foundation for the security methods that actually stop them.
How to Stop Data Breaches With Encryption, Access Controls, and Regular Testing
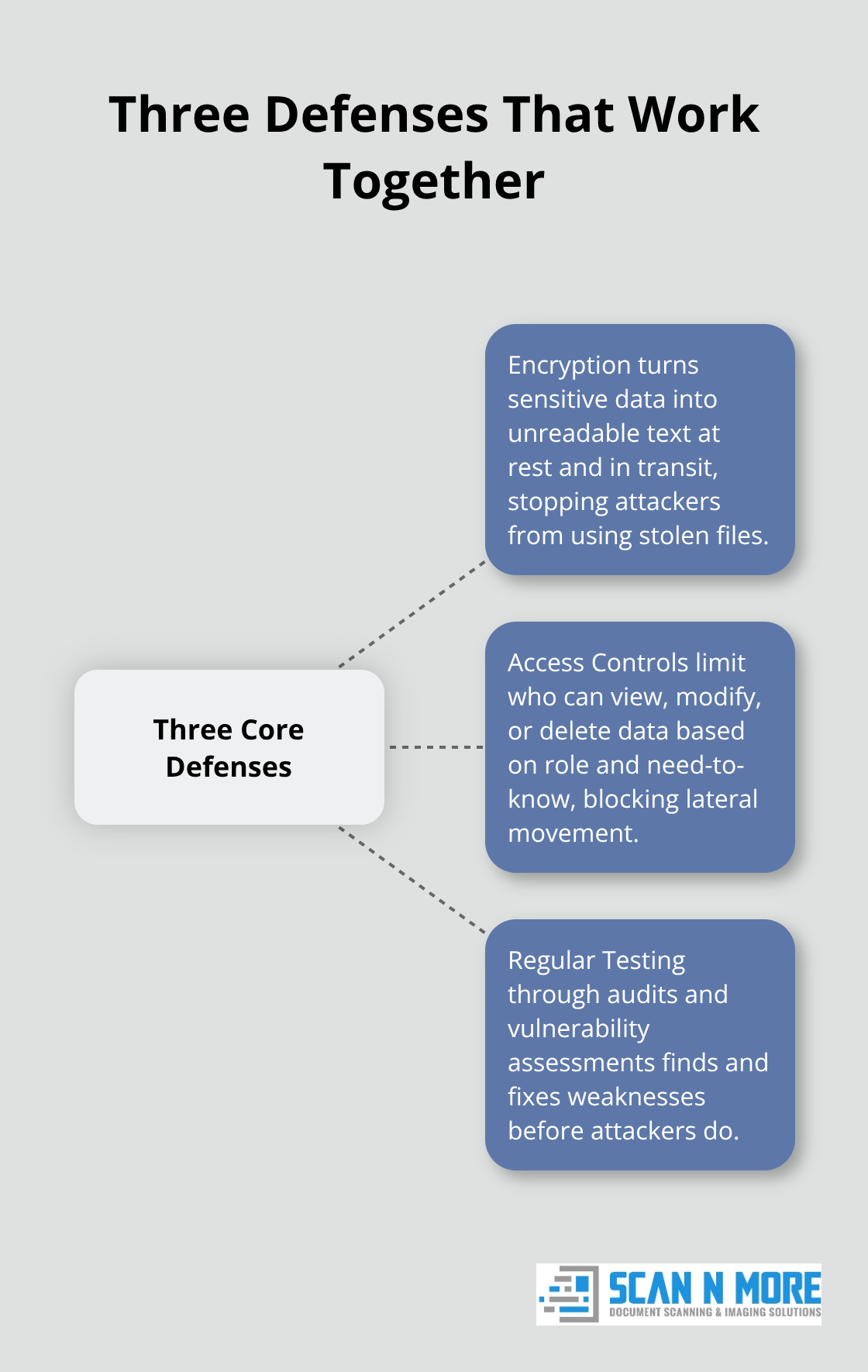
The threats you face demand three interconnected defenses that work together to prevent unauthorized access and data theft. Encryption transforms sensitive data into unreadable format so that stolen files become worthless to attackers. Access controls restrict who can view, modify, or delete data based on job function and necessity. Regular security audits and vulnerability assessments expose weaknesses before attackers find them. These aren’t theoretical concepts-they’re operational requirements that directly reduce breach risk and detection time.
Encryption Protects Data at Every Stage
Encryption at rest protects stored data using AES-256, the military-grade standard that makes brute-force attacks computationally impractical. Organizations that encrypt sensitive databases, file shares, and backup systems eliminate the risk of stolen hardware becoming a data breach. Encryption in transit uses TLS protocols to secure data moving between systems, applications, and cloud services-unencrypted connections expose credentials and customer information to network interception. IBM’s 2024 report found that organizations with encryption deployed company-wide experienced 28 percent lower breach costs than those without it. You should implement encryption for all systems storing personally identifiable information, payment card data, or health records. Maintain a documented cryptographic key management lifecycle that includes key rotation every 90 days, restricted access to key storage, and audited key usage. Non-production environments like development and testing databases must also use encryption or data masking techniques that replace real customer information with fictional values. This prevents developers from accidentally exposing production data during testing or code reviews.
Access Controls Stop Unauthorized Movement Through Your Systems
Role-based access control (RBAC) assigns permissions based on job function-a customer service representative needs access to contact information but not to salary data or source code. Enforce the principle of least privilege ruthlessly: employees should access only the data required for their specific role, nothing more. Multi-factor authentication (MFA) on all systems handling sensitive data makes stolen passwords worthless because attackers lack the second authentication factor. Microsoft security research shows that organizations using MFA reduce account compromise incidents by 99 percent. Privileged Access Management (PAM) systems monitor and control administrative accounts that have elevated permissions across critical infrastructure. Every action taken by an admin should be logged, reviewed, and justified-this visibility catches insider threats and prevents lateral movement after initial compromise. Audit access rights quarterly and remove permissions when employees change roles or leave the organization. Many breaches succeed because encryption without strong access controls provides false security when attackers obtain encryption keys.
Vulnerability Assessments Expose Hidden Weaknesses
Vulnerability assessments scan systems for known security flaws like unpatched software, misconfigurations, and weak encryption settings. Conduct these assessments quarterly at minimum, or monthly in environments handling health or payment data. Penetration testing goes further by simulating actual attacker behavior-ethical hackers attempt to break into your systems to identify exploitable weaknesses that automated scans miss. Organizations that run annual penetration tests catch an average of 25 to 30 critical vulnerabilities per assessment, many of which would have remained undetected by standard scanning. Security audits review policies, procedures, and compliance controls to verify that documented practices match actual operations.

Patch management must follow a defined timeline: apply critical security patches within 15 days, high-priority patches within 30 days, and routine updates within 60 days. Tracking your patching rate as a percentage tells you how exposed you remain to known exploits. Organizations that maintain 95 percent patching rates reduce breach likelihood significantly compared to those below 80 percent.
Compliance Frameworks Guide Your Implementation
Industry standards like HIPAA, GDPR, and SOC 2 establish specific requirements for encryption, access controls, and audit trails that your organization must meet. These frameworks provide a structured path to translate best practices into operational controls, ensuring lifecycle coverage and regulatory alignment across your data protection efforts. Mapping your security controls to NIST CSF categories helps you structure policies and demonstrate compliance to auditors and regulators. Automated compliance reporting tools generate evidence of your encryption deployment, access control audits, and vulnerability remediation timelines-this documentation proves your commitment to data protection during regulatory reviews. The next section covers the specific compliance standards that apply to your industry and how to meet them without disrupting operations.
Which Compliance Standards Apply to Your Organization
Compliance requirements form the legal foundation that forces organizations to implement controls that actually prevent breaches. HIPAA applies to healthcare providers, health plans, and healthcare clearinghouses handling patient records. The regulation mandates encryption for electronic protected health information, access controls that limit who can view patient data, and audit logs documenting every access to medical records. Covered entities must conduct risk assessments annually to identify vulnerabilities in their systems and demonstrate remediation efforts to regulators. Violations carry penalties up to $1.5 million per violation category per year, making HIPAA compliance expensive when ignored but straightforward when implemented correctly.
GDPR Protects European Data and Demands Rapid Response
GDPR governs data protection for any organization processing personal data of European Union residents, regardless of where your company operates. The regulation requires data minimization-collect only what you need-and explicit consent before processing personal information. Organizations must notify regulators and affected individuals within 72 hours of discovering a breach, which forces rapid incident response rather than the slow 207-day detection timelines many organizations accept. GDPR fines reach 20 million euros or 4 percent of global annual revenue, whichever is higher, making compliance non-negotiable for any company with European customers.
SOC 2 Compliance Proves Your Security Practices to Customers
SOC 2 compliance applies to service providers handling customer data and requires auditors to evaluate your security controls, availability, processing integrity, confidentiality, and privacy practices. Unlike HIPAA and GDPR, SOC 2 is voluntary but increasingly required by enterprise customers as a contract prerequisite. Type II audits, which evaluate controls over six to twelve months, provide stronger evidence of consistent security practices than Type I audits covering a single point in time.
Framework Overlap Simplifies Implementation
These frameworks overlap significantly. All three require encryption, access controls, audit trails, and incident response procedures-implementing one framework’s requirements typically moves you toward compliance with the others. Organizations should map their existing controls to NIST CSF categories to structure policies and demonstrate alignment across multiple regulatory standards. Automated compliance reporting tools generate evidence of encryption deployment, access audits, and vulnerability remediation timelines without manual documentation that consumes security team resources.
Operational Requirements for Sustained Compliance
Assign a compliance owner within your organization with authority to enforce security policies and coordinate with legal, IT, and business units on implementation. Schedule compliance audits annually at minimum, more frequently if you operate in highly regulated industries like healthcare or finance. Many organizations fail compliance not because controls are missing but because documentation proves implementation inconsistently. Audit trails must capture who accessed what data, when, and from which system-this evidence demonstrates controls function as designed. Patch management timelines must be documented with evidence showing critical patches deployed within 15 days and routine updates within 60 days. Data inventory and classification processes should be formalized and reviewed quarterly to ensure sensitive information remains protected as your systems evolve. Regulatory requirements force accountability that loose internal security policies never achieve.
Final Thoughts
Data breaches cost $4.45 million on average, but that figure only captures direct expenses-the real cost includes lost customer trust, regulatory fines, and operational disruption that extends for months. We at Scan N More understand that effective data security methods require continuous attention and refinement as threats evolve. The three pillars you’ve learned-encryption, access controls, and regular vulnerability testing-form the foundation of any serious data protection program.
Organizations detecting breaches within 30 days spend 40 percent less on incident response than those taking 207 days to notice compromise. Start by conducting a data inventory to identify where sensitive information lives across your systems, then classify data by sensitivity level and apply encryption to everything handling personally identifiable information, payment card data, or health records. Implement multi-factor authentication on all critical systems, audit privileged access quarterly, and deploy endpoint detection and response tools that monitor for suspicious activity.
Organizations managing physical documents containing sensitive data should also secure the digitization process-Scan N More offers professional document scanning services that transform paper-based processes into secure digital solutions while maintaining compliance with HIPAA and GDPR requirements. Data security operates as an operational discipline requiring sustained investment and attention, not a project with an end date. Start implementing these methods today and adjust your approach as threats change.

