Data breaches cost organizations an average of $4.45 million per incident in 2024, and that number keeps climbing. Companies face tougher regulations, customer demands for protection, and attackers using new tactics every day.
At Scan N More, we’ve seen firsthand how organizations struggle with data security management in 2025. This guide covers what actually works.
Why Data Breaches Now Cost More and Hit Harder
The Financial and Operational Impact
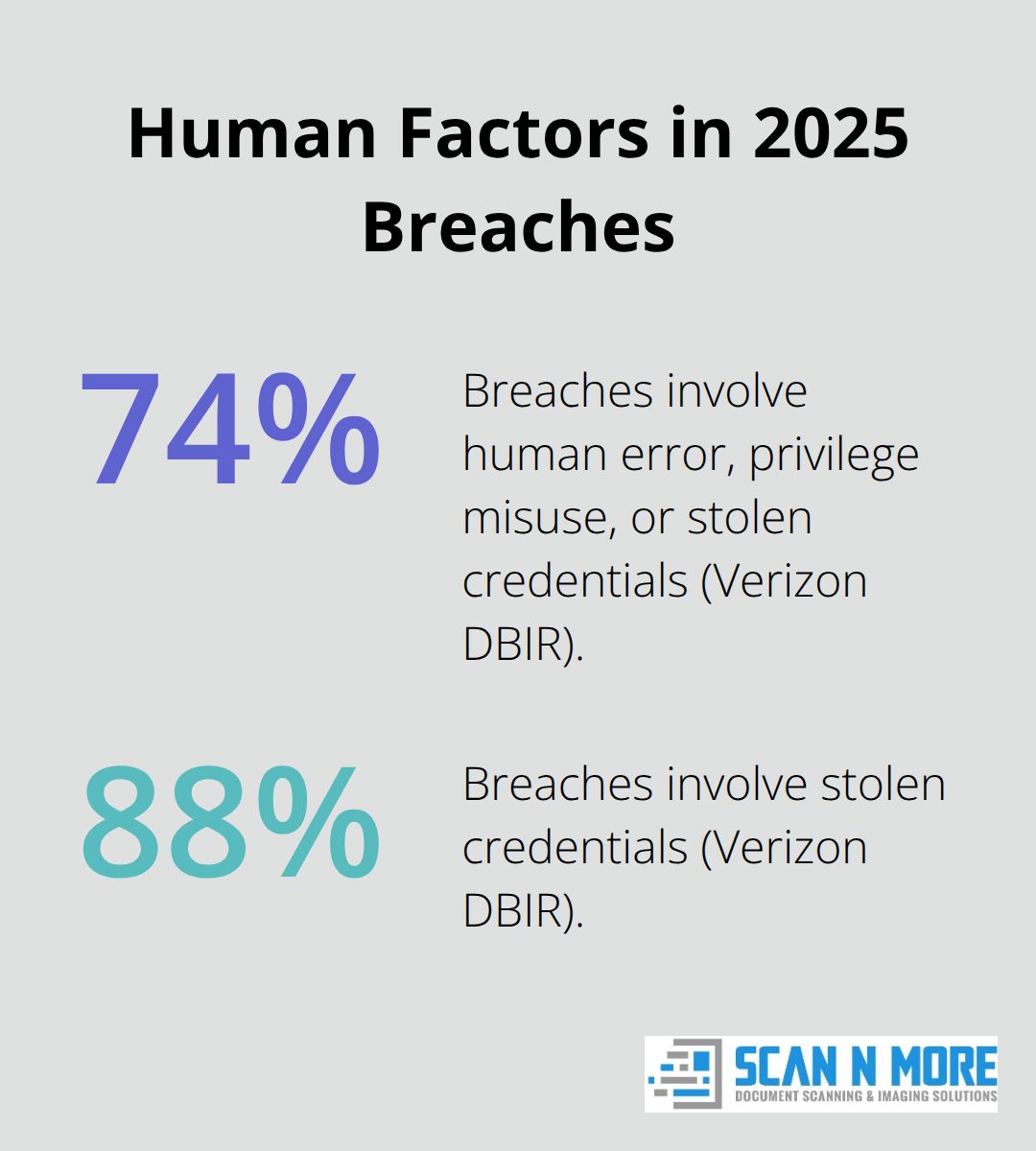
The average cost of a data breach reached $4.88 million in 2024 according to the IBM Cost of a Data Breach Report, and organizations pay far more than just recovery expenses. When a ransomware attack strikes, the average downtime stretches to about 24 days, during which operations grind to a halt, revenue evaporates, and customers lose trust. GDPR fines reach 4% of annual global revenue or €20 million, while HIPAA penalties climb to $1.5 million per violation. These aren’t theoretical numbers-they’re real penalties that have crippled organizations. The Verizon Data Breach Investigations Report shows that 74% of breaches involve human error, privilege misuse, or stolen credentials, meaning most incidents are preventable with proper security practices and controls.
How Attackers Exploit Human Weakness
Human error creates the largest vulnerability in any organization. Employees click malicious links, reuse passwords across systems, and grant excessive access to vendors without proper vetting. Attackers exploit these gaps relentlessly. They steal credentials through phishing, escalate privileges once inside networks, and move laterally through systems that lack proper segmentation. Organizations that fail to train employees or enforce access controls hand attackers the keys to sensitive data.
The New Threat Landscape
The threat landscape in 2025 has fundamentally shifted. Ransomware-as-a-Service democratizes attacks by offering toolkits to affiliates, enabling double extortion where attackers threaten both data destruction and public leaks. AI-powered phishing now mimics writing styles and voices with near-perfect accuracy, making traditional email filters obsolete. Cloud and API exploits remain common breach points due to poorly configured environments and excessive permissions. Supply chain attacks compromise trusted vendors, forcing organizations to secure not just their own systems but every third party with access to sensitive data. According to Cisco’s Cybersecurity Readiness Index 2025, 86% of business leaders experienced at least one AI-related security incident in the past year, with 43% involving model theft or unauthorized access.
Why Traditional Defenses Fall Short
Static security measures no longer work. Organizations that treat data security as an afterthought or a compliance checkbox will fall behind. Those that embed security into operations, enforce zero-trust principles, and invest in rapid detection and response capabilities gain competitive advantage and protect their bottom line. The organizations winning in 2025 implement multi-layered defenses that address human factors, technological vulnerabilities, and emerging attack vectors simultaneously.
Core Data Security Practices Every Organization Should Implement
Multi-Factor Authentication Stops Credential Theft
Organizations that survive 2025 don’t rely on single security layers. They stack defenses so that when one fails, others catch the breach before damage spreads. The reality is stark: about 88% of breaches involve stolen credentials, but these failures are entirely preventable. Multi-factor authentication stops credential theft cold because stolen passwords alone no longer grant access. Organizations implementing MFA across all user accounts reduce breach risk dramatically. Attackers steal credentials through phishing and social engineering constantly, yet MFA renders those stolen passwords useless without the second factor. Enforce MFA on every user account, not just administrators. The principle of least privilege means employees access only the data and systems their job requires, nothing more. A developer shouldn’t access payroll databases. A finance team member shouldn’t view source code. Quarterly permission reviews catch the bloat that creeps into systems when people change roles but retain old access. Set specific review dates on your calendar and audit access every 90 days, not annually. This catches excessive permissions before attackers exploit them.
Backups and Recovery Planning Defeat Ransomware
Data backups following the 3-2-1 rule protect against ransomware: maintain three copies of critical data, store them on two different storage types, and keep one copy offline or immutable. When ransomware hits, offline backups become your lifeline. Test restoration procedures monthly because backups that can’t restore quickly are worthless. Document your recovery time objectives clearly so leadership understands how long data will remain unavailable if the worst happens.
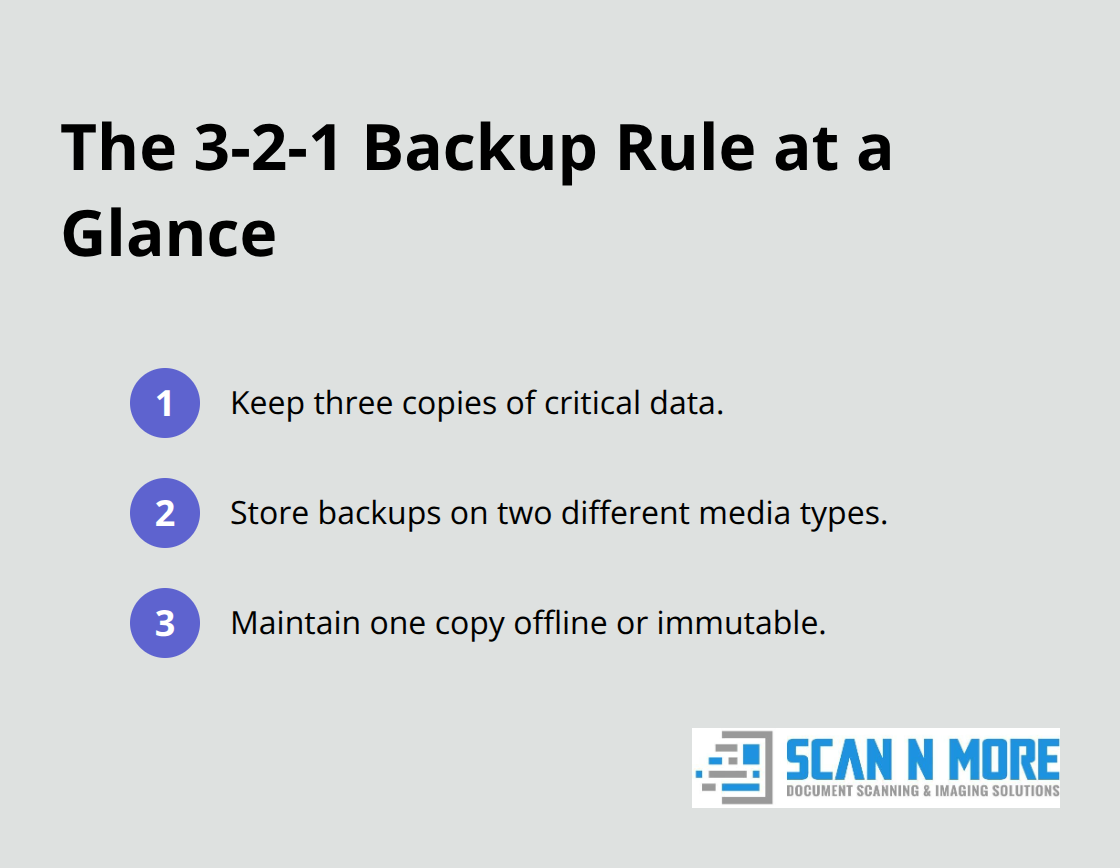
Organizations that skip restoration testing discover too late that their backups fail when needed most. Ransomware attackers know that many organizations lack tested recovery procedures, which is why they target companies with weak backup strategies. Immutable backups (those that attackers cannot delete or encrypt) provide the strongest defense against double extortion attacks where criminals threaten both data destruction and public leaks.
Employee Training Separates Breached from Protected Organizations
Employee training separates organizations that get breached from those that don’t. Phishing simulations show which employees click malicious links, and targeted follow-up training for those individuals cuts susceptibility rates significantly. Annual security awareness programs aren’t enough; organizations need quarterly training with role-specific content. Finance teams need to recognize invoice fraud. IT staff need to understand privilege escalation. Healthcare workers need HIPAA-specific scenarios. Generic training wastes time and money. Measure training effectiveness through phishing simulation click rates and track improvements over quarters. Establish clear security policies that employees can actually follow, not hundred-page documents buried on a server. One-page policies on password management, remote work, vendor access, and incident reporting get read and remembered. Make security policies visible, accessible, and tied to real consequences. Organizations that treat security as IT’s problem alone will fail. Security wins when leadership visibly supports it, when budgets fund it adequately, and when employees understand why it matters to their paycheck and career. The human element determines whether defenses hold or crumble under pressure.
Building a Security-First Culture
Leadership commitment transforms security from a compliance burden into organizational strength. When executives allocate adequate budgets, enforce policies consistently, and communicate security priorities regularly, employees take these responsibilities seriously. Visible leadership support signals that security matters as much as revenue and customer service. Tie security performance to performance reviews and compensation where appropriate, creating incentives for compliant behavior. Organizations that reward employees for reporting suspicious activity and completing training see higher engagement and faster threat detection. Security awareness becomes embedded in daily operations rather than treated as an annual checkbox. This cultural shift reduces human error and creates multiple layers of human detection alongside technical controls. As organizations strengthen these foundational practices, they build resilience against both current threats and emerging attack vectors that exploit gaps in access control, backup procedures, and employee vigilance.
What’s Actually Threatening Your Data in 2025
AI-Powered Attacks Exploit Detection Gaps
AI-powered attacks have shifted from theoretical threats to operational reality. According to Cisco’s Cybersecurity Readiness Index 2025, 86% of business leaders experienced at least one AI-related security incident in the past year, with 43% involving model theft or unauthorized access and 38% involving data poisoning attempts. These aren’t edge cases anymore.

Attackers now use machine learning to personalize phishing emails that mimic your organization’s internal communication patterns, making them nearly impossible to distinguish from legitimate messages. Traditional email filters catch obvious threats, but AI-generated attacks adapt in real time based on what works and what gets blocked.
Layer multiple defenses instead of hoping your users spot the difference. Deploy advanced email authentication protocols like DMARC and DKIM to verify sender identity, implement phishing-resistant MFA such as FIDO2 hardware keys instead of time-based codes that attackers can intercept, and run phishing simulations monthly with immediate follow-up training for anyone who falls for the bait. Organizations that wait for perfect detection rates before acting get compromised. Those that assume breach and implement rapid response capabilities survive.
Ransomware-as-a-Service Enables Sophisticated Attacks
Ransomware attacks now operate as sophisticated business models. RaaS platforms offer attack toolkits to affiliates on dark web marketplaces, meaning even unsophisticated threat actors can launch enterprise-grade campaigns. Double extortion tactics-where attackers threaten both data encryption and public disclosure-force organizations to pay even when they have clean backups. According to the 2025 Data Breach Investigations Report, ransomware attacks increased 58% year-over-year in 2025, and 74% of breaches involve human elements that attackers exploit relentlessly through compromised credentials and unpatched systems.
Your defense strategy must include offline immutable backups tested monthly for actual recovery speed, network segmentation that prevents lateral movement even after initial compromise, and a detailed incident response playbook with specific roles and communication procedures. Document recovery time objectives so leadership understands the cost of delay. Organizations that implement these controls stop attackers from extracting maximum value from their campaigns.
Third-Party Vendors Create Supply Chain Vulnerabilities
Third-party vendor risk management has become non-negotiable because attackers target the weakest link in your supply chain. SolarWinds and MOVEit demonstrated that compromising a single trusted vendor can breach thousands of downstream customers. Conduct security assessments before signing vendor contracts, not after deployment. Request software bills of materials and evidence of secure development practices.
Implement continuous monitoring of vendor access using privileged access management tools that log every connection and alert on unusual activity. Organizations with 60% visibility into vendor usage according to Cisco data lack basic oversight. Set specific approval requirements for which vendors can access what data, review those permissions quarterly, and terminate access immediately when relationships end. The organizations protecting themselves in 2025 treat emerging threats not as distant possibilities but as active problems requiring immediate, measurable responses.
Final Thoughts
Data security management in 2025 requires action, not planning. Organizations that wait for the perfect strategy get breached while competitors move forward. Start with a security audit that identifies where your organization stands today-map your current data flows, document who accesses what information, and test your backup restoration procedures. This audit reveals gaps that attackers exploit and shows you exactly where to focus your efforts first.
Implement multi-factor authentication across all accounts immediately, enforce the principle of least privilege through quarterly permission reviews, test your backups monthly, and run phishing simulations with follow-up training for anyone who clicks malicious links. These foundational practices cost far less than recovering from a breach and stop the majority of attacks that plague organizations. Build a comprehensive data protection strategy that extends beyond technology by engaging leadership to allocate adequate budgets, creating role-specific security training that employees actually understand, and documenting your incident response procedures so your team knows exactly what to do when threats materialize.
Organizations managing sensitive documents face additional complexity when paper-based records need digitization. Scan N More provides professional document scanning services that transform paper into secure digital solutions while maintaining compliance with data security standards. The organizations winning in 2025 treat data security as a business priority, not an IT checkbox, and they measure progress through metrics like mean time to detect and mean time to respond.

