Data breaches cost companies an average of $4.45 million per incident, according to IBM’s 2023 report. Most of these losses stem from failing to meet basic data security requirements that regulations now mandate.
At Scan N More, we’ve seen firsthand how businesses struggle to navigate compliance standards, implement proper safeguards, and respond when incidents occur. This guide covers the essential requirements your business must follow to protect customer data and avoid costly penalties.
Regulatory Compliance Standards Your Business Cannot Ignore
Over 80% of the global population now lives under data privacy laws, according to the International Association of Privacy Professionals. Your business likely operates across multiple jurisdictions with conflicting requirements, and non-compliance carries severe financial consequences. The highest GDPR fine to date reached $1.2 billion, imposed on Meta in 2023. These aren’t theoretical risks-they’re real penalties enforced against real companies that failed to meet regulatory standards. The European Union AI Act began enforcement in 2025 and reaches full enforceability in 2026, introducing additional obligations around how AI systems handle personal data. Eight US states enacted comprehensive privacy laws by the end of 2025, expanding the regulatory landscape beyond California’s CCPA and CPRA.
Which Regulations Apply to Your Business
GDPR applies if you process data of European residents, regardless of where your business operates. HIPAA governs healthcare organizations and their business associates handling protected health information, with requirements for encryption, access controls, and breach notification within 60 days. SOC 2 compliance matters for service providers handling customer data, requiring audits that validate your security, availability, processing integrity, confidentiality, and privacy controls. Your first step is to identify which frameworks apply to your operations. A single business often falls under multiple standards simultaneously, so treating them as separate initiatives wastes resources and creates compliance gaps.
Map Your Data Flows and Document Access
Start by mapping your data flows-identify where sensitive information enters your systems, how it moves between departments and vendors, and who has access at each stage. Document this in writing, as regulators expect evidence of your data inventory and access controls. This exercise reveals which data requires the strongest protections and where your organization faces the highest risk. The FTC Safeguards Rule requires information security programs with administrative, technical, and physical safeguards. This foundation covers most regulatory expectations across GDPR, HIPAA, and SOC 2.
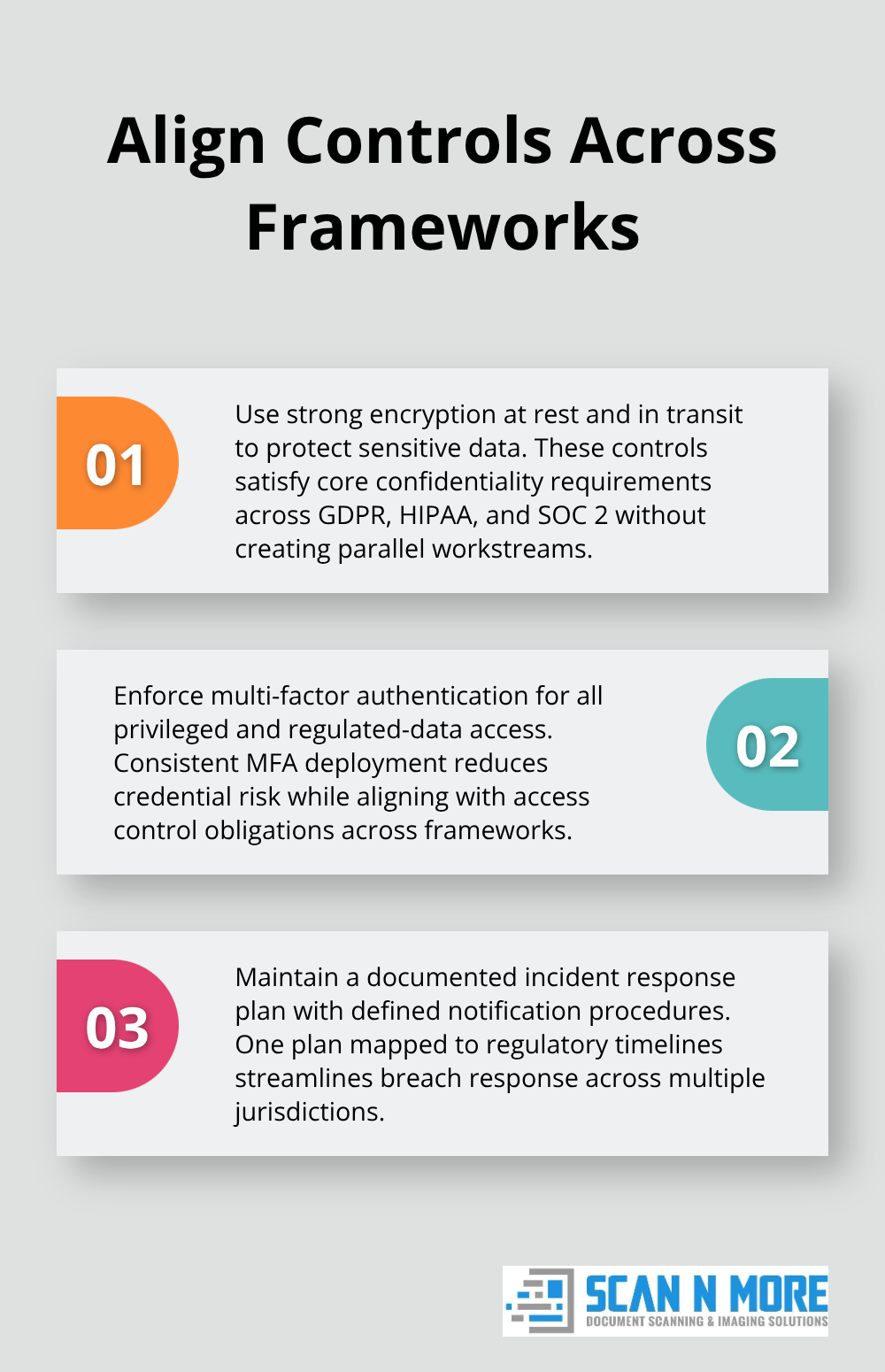
Align Security Practices Across All Frameworks
Strong encryption at rest and in transit satisfies GDPR, HIPAA, and SOC 2 requirements. Multi-factor authentication for employee access addresses access control obligations across all three standards. A documented incident response plan with defined notification procedures meets breach response requirements under GDPR and HIPAA. Rather than building separate security programs for each regulation, implement controls that satisfy multiple frameworks simultaneously. This approach reduces complexity and strengthens your overall security posture.
Manage Third-Party Risk and Vendor Compliance
Your vendor contracts must include written security expectations and require incident notifications, since you remain liable for third-party breaches under most regulations. Deploy a privacy management platform to track consent, manage data subject requests, and maintain audit trails proving compliance. These tools automate much of the documentation work that regulators scrutinize during audits or investigations. Your vendors represent a significant compliance risk-many data breaches originate from weak third-party security practices. Verify that your service providers meet the same standards you’ve implemented internally, and conduct periodic assessments to confirm ongoing compliance.
Build Security Controls That Actually Prevent Breaches
Stop Credential Attacks Before They Start
Compliance frameworks demand strong access controls and authentication, but most businesses treat these requirements as checkbox exercises rather than functional defenses. The 2021 Ponemon Data Breach research report, sponsored by IBM, shows that compromised credentials represented a top breach vector. This single vulnerability class exceeds the cost of many other breach types combined, yet fixing it requires discipline rather than expensive technology. Multi-factor authentication stops roughly 99.9% of credential-based attacks, yet 77% of IT professionals still report lacking an enterprise-wide incident response plan, suggesting MFA adoption remains inconsistent across most organizations.
Start with a strict need-to-know basis for sensitive data access-employees should access only information required for their specific roles. Implement strong password requirements of at least 16 characters with complexity, rotate credentials after any suspected breach, and disable default vendor passwords immediately upon system deployment. Set session timeouts aggressively, especially for remote access, and enforce MFA for any connection to systems handling regulated data.
The number 100% seems to be not appropriate for this chart. Please use a different chart type.
Document Access Control Policies and Audit Regularly
Write your access control policy to specify who approves access requests, how long access persists, and what triggers immediate revocation. Regular audits of active user accounts catch former employees and contractors who retain access months after departure-a surprisingly common finding during security assessments. Screen sharing, shoulder surfing, and unencrypted email transmissions remain common attack vectors that basic controls eliminate.
Protect Data Through Structured Backup Strategies
Data backups must follow a structured strategy rather than ad-hoc snapshots that provide false confidence. Test your recovery procedures quarterly under realistic conditions, not just annually during compliance audits. Backups stored on the same network as production systems offer zero protection against ransomware, so maintain offline copies in geographically separate locations with restricted access. The FTC requires backup frequency, integrity checks, and documented restoration procedures as core elements of your disaster recovery plan.
Train Employees to Recognize and Report Threats
Employee training represents your most cost-effective security investment, yet 73% of U.S. adults have experienced some kind of online scam or attack. Phishing emails remain the initial infection vector in the majority of ransomware campaigns, making user awareness your first line of defense. Conduct mandatory training at least annually, covering password security, phishing recognition, incident reporting procedures, and data handling requirements. Track completion rates and follow up with non-compliance.
Establish clear reporting channels where employees feel safe flagging suspicious activity without fear of blame, since early detection prevents most breaches from causing significant damage. This foundation of access controls, backups, and trained staff creates the conditions for effective incident response-the subject we address next.
When Breaches Happen, Speed Determines Your Survival
Establish a Documented Incident Response Plan
Most organizations lack the muscle memory to respond effectively when a breach occurs. The FTC requires a documented incident response plan with defined roles, notification timelines, and recovery procedures, but 77% of IT professionals report their companies lack an enterprise-wide plan entirely. This gap transforms a containable incident into a catastrophe.
Your response plan needs specific assignments: a designated senior coordinator who owns the process, a forensics team responsible for investigation and evidence preservation, legal counsel to navigate notification requirements, and communications staff to manage stakeholder notifications. When a breach happens, your first 24 hours determine whether you contain the damage or watch it spiral. Assign someone today to lead this effort, not during the chaos of an active incident.
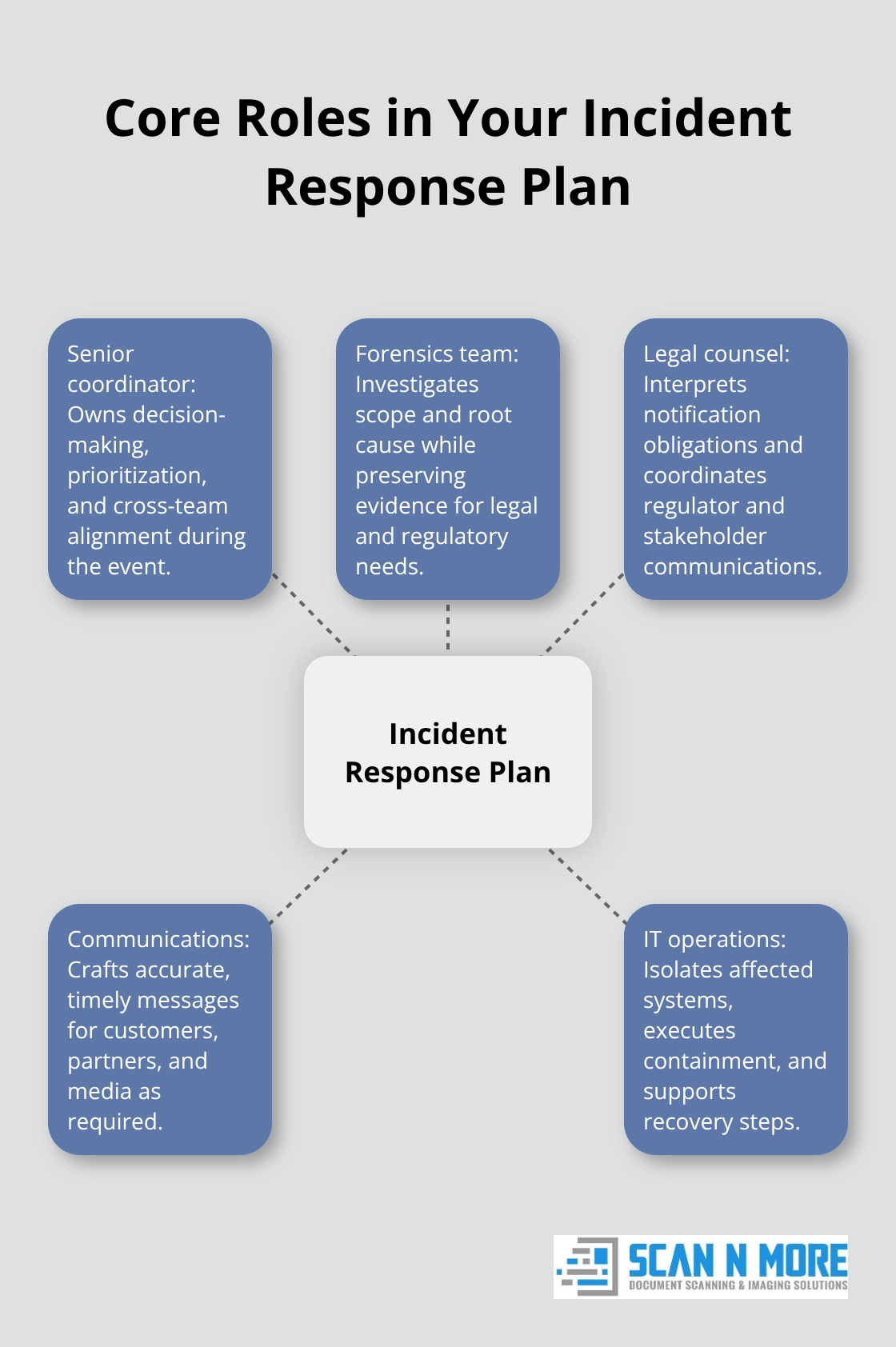
Your plan must specify exactly who contacts law enforcement, which systems get isolated first, and how you preserve evidence without destroying logs investigators need. Test this plan quarterly under realistic conditions, rotating which team members play which roles so knowledge doesn’t concentrate in one person.
Deploy Monitoring Systems That Detect Threats Early
Breaches tied to remote work can significantly increase costs, partly because remote systems lack the monitoring infrastructure that office networks provide. Your detection capabilities directly impact response speed, making monitoring investments non-negotiable.
Deploy intrusion detection systems that flag suspicious network activity, maintain centralized security logs from all systems, and configure alerts for unusual data access patterns or failed login attempts. On average, a hacking attack occurs every 39 seconds on internet-connected systems according to research from the University of Maryland, underscoring that breaches aren’t hypothetical. Most organizations discover breaches weeks or months after they occur because they lack monitoring visibility.
Implement automated alerts that trigger when user accounts access data outside normal patterns, when sensitive files get copied in bulk, or when someone logs in from unfamiliar locations. These controls cost far less than breach notification and recovery expenses.
Navigate Notification Requirements Across Jurisdictions
Your notification obligations vary by state and federal jurisdiction, with HIPAA requiring notification within 60 days and GDPR creating potential fines up to 4% of global revenue. Notification laws require informing affected individuals, regulatory agencies, and sometimes media outlets, so your communications must be accurate and timely.
Draft notification templates now while you’re not under pressure, specifying what information you’ll disclose about the breach, what steps affected individuals should take, and how they can contact you for questions. These templates serve as your foundation when time pressure and stress threaten to derail clear communication.
Communicate Transparently to Rebuild Trust
Post-breach communication extends beyond initial notification into reputation recovery, where transparency becomes your primary asset. Organizations that immediately acknowledge breaches and clearly explain remediation steps retain customer trust better than those that minimize incidents or delay disclosure.
Publish a clear timeline of events, explain what data was compromised, describe what you’ve done to prevent recurrence, and offer affected individuals concrete protections like credit monitoring or identity theft insurance. This honesty costs less than the customer churn that follows secretive responses. Customers expect organizations to own their failures and demonstrate concrete action to prevent future incidents.
Final Thoughts
Data security requirements form the foundation of your business operations, not optional add-ons that you can defer. The frameworks we’ve covered-GDPR, HIPAA, SOC 2, and the FTC Safeguards Rule-all demand the same core practices: strong access controls, encrypted data, documented incident response plans, and trained employees who recognize threats. Implementing these controls simultaneously across multiple regulations eliminates redundancy and strengthens your overall security posture far more effectively than treating each standard separately.
Your immediate action items address the most common breach vectors and satisfy core requirements across every major compliance framework. Assign a senior leader to own your incident response plan and test it quarterly, deploy multi-factor authentication across all systems handling regulated data, map your data flows to understand where sensitive information lives, establish clear backup procedures with offline copies in separate locations, and conduct mandatory security training for all staff with emphasis on phishing recognition. These steps transform data security from a compliance checkbox into a functional defense that protects your customers and your bottom line.
We at Scan N More understand that data security extends beyond digital systems to physical documents as well. Our professional document scanning services help businesses transition paper-based records into secure digital environments while meeting data protection standards. Taking action today prevents the far costlier consequences of inaction tomorrow.

