Healthcare organizations handle millions of sensitive patient records daily, making data security a top priority. HIPAA violations can result in fines up to $1.5 million per incident.
We at Scan N More understand that HIPAA compliant scanning requires more than basic security measures. The right technology and procedures protect patient privacy while streamlining your document management workflow.
What Are HIPAA’s Core Scanning Requirements?
HIPAA establishes three fundamental safeguard categories that directly impact your scanning operations. Protected Health Information includes any individually identifiable health data transmitted or maintained electronically, and this definition extends to scanned documents the moment they enter your digital systems. The healthcare industry experienced breached records in 2024, making strict adherence to these standards non-negotiable for your organization.
Physical Security Controls During Scanning
Your scanning environment needs locked storage areas with restricted access for both original documents and scanning equipment. Staff must complete background checks before they handle PHI, and you need documented procedures that specify who can access scanning areas during different shifts. Multi-factor authentication becomes mandatory for any system that processes scanned PHI (this applies to all workstations and mobile devices). Your facility requires 24/7 network monitoring with firewalls that protect all scanning workstations from unauthorized access.
Technical Safeguards for Digital Workflows
Encryption must protect scanned documents both during transmission and storage, with detailed audit trails that document every access and modification. Your organization needs vulnerability scans every six months and penetration testing annually under updated HIPAA regulations. Systems must recover within 72 hours after any data loss incident occurs, and you need comprehensive network mapping updated every 12 months to track all devices that handle scanned PHI.
Administrative Compliance Framework
Annual security risk assessments help identify compliance gaps in your scanning processes. Staff training programs must address cybersecurity awareness and proper data handling, as phishing attacks remain the most common infection vector in healthcare systems. Your policies must clearly define access permissions during and after scanning operations (including temporary staff and contractors), with regular vendor contract reviews for any third-party services that handle your scanned documents.
These foundational requirements create the framework for secure scanning operations, but implementation requires specific best practices that address real-world challenges.
How Do You Implement Bulletproof Scanning Procedures?
Effective scanning procedures start with a documented chain of custody that tracks every document from receipt to digital storage. Your staff must log each document with timestamps, handler names, and processing locations before scanning begins. SecurityMetrics research shows systems become compromised within 166 days on average after vulnerabilities appear, making immediate documentation essential for audit purposes. Create numbered batches for all incoming documents and assign unique identifiers that connect physical records to their digital counterparts throughout the entire process.
Document Control Systems That Work
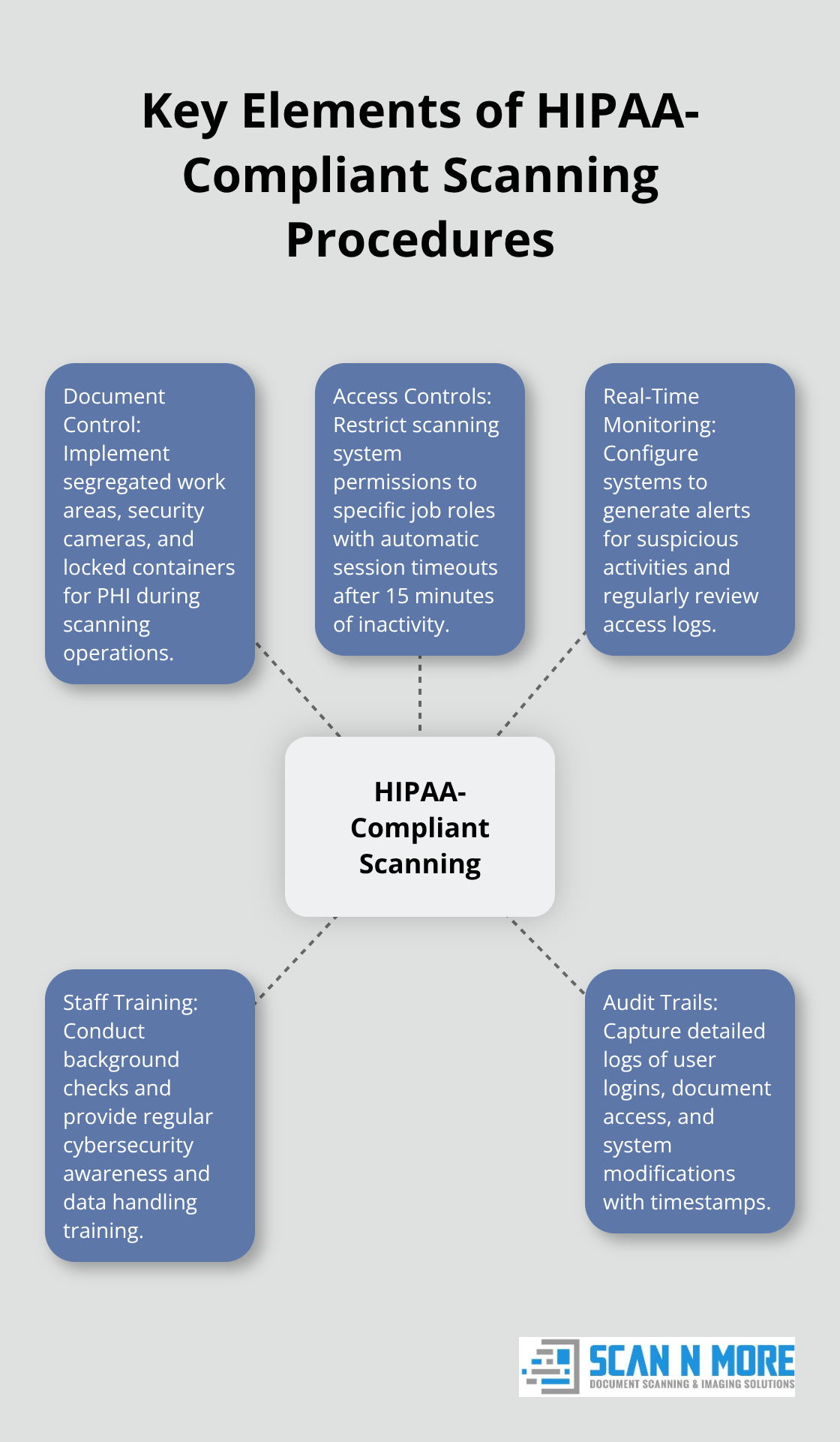
Document handling protocols require segregated work areas where only authorized personnel can access PHI during scanning operations. Install security cameras in all scanning areas and maintain visitor logs that record access times and purposes. Your organization needs locked containers for documents that await processing and separate secured storage for completed batches before destruction or return.
Staff must wear identification badges at all times, and you should implement clean desk policies that prevent unauthorized viewing of sensitive documents. Mobile device scanning has increased significantly, but many smartphone apps lack HIPAA compliance and could result in substantial fines.
Access Controls and Real-Time Monitoring
Access controls must restrict scanning system permissions to specific job roles with automatic session timeouts after 15 minutes of inactivity. Your audit trails need to capture user login attempts, document access times, system modifications, and failed authentication events with detailed timestamps. The average healthcare breach now costs $10.22 million per incident according to recent studies, making thorough monitoring financially essential.
Configure your systems to generate real-time alerts for suspicious activities like multiple failed login attempts or unusual access patterns outside normal business hours. Regular reviews of access logs help identify potential security incidents before they escalate into major breaches.
Staff Training and Accountability Measures
Background checks become mandatory for all employees who handle PHI during scanning operations. Your training programs must address cybersecurity awareness and proper data handling procedures, as phishing attacks remain the most common infection vector in healthcare systems. Staff need clear guidelines about mobile device usage and approved scanning applications that maintain HIPAA compliance.
Document who receives training and when refresher sessions occur (aim for quarterly updates on security protocols). Create accountability measures that track individual performance and compliance with established procedures. These human-centered safeguards work alongside your technical infrastructure to create comprehensive protection for patient data throughout the document scanning workflow.
Which Technology Tools Guarantee HIPAA Compliance
Your scanning technology stack requires specific components that address HIPAA’s technical safeguards while maintaining operational efficiency. Encrypted scanning systems must use AES-256 encryption for data at rest and TLS 1.2 or higher for transmission, with automated key rotation every 90 days to prevent unauthorized access. Digital workflow management platforms need role-based access controls that automatically log every document interaction, user session, and system modification with timestamps that support forensic analysis during audits. Web Application Firewalls protect your scanning applications from vulnerabilities, while Security Information and Event Management solutions provide real-time monitoring that alerts administrators to suspicious activities within minutes rather than hours.
Advanced Encryption and Storage Architecture
Modern HIPAA-compliant scanning solutions implement zero-knowledge architecture where encryption keys remain separate from stored data. This prevents unauthorized access even during system breaches. Your storage systems need automated data classification that identifies PHI and applies appropriate encryption levels based on sensitivity, with network segmentation that isolates scanning workstations from general office networks. Cloud storage requires encryption both in transit and at rest, with secure API management that validates every data request through multi-factor authentication. Database encryption must extend beyond file-level protection to include metadata, search indexes, and temporary processing files that could contain patient information fragments.

Disaster Recovery and Business Continuity Systems
Backup solutions must create encrypted copies within four hours of document scanning completion, with geographically distributed storage that maintains at least three copies across different physical locations. Your recovery testing needs quarterly validation that systems can restore operations within the mandated 72-hour timeframe (including full workflow functionality and audit trail integrity). Automated failover systems should activate when primary scanning infrastructure experiences downtime, switching to secondary systems without data loss or compliance gaps. Regular backup integrity checks prevent corruption issues that could compromise patient data during critical recovery situations.
Final Thoughts
HIPAA compliant scanning demands a comprehensive approach that combines technical safeguards, administrative controls, and physical security measures. Your organization must implement encrypted systems, maintain detailed audit trails, and conduct regular vulnerability assessments to protect patient data effectively. Staff training programs and access controls form the foundation of successful compliance, while backup systems and disaster recovery plans protect against data loss incidents.
Professional services eliminate the complexity of compliance maintenance while they improve operational efficiency. We at Scan N More offer secure document solutions that transform paper-based processes into digital workflows while we maintain strict data security standards. Our services handle legal and medical documents with guaranteed compliance and exceptional quality.
The investment in proper HIPAA compliant scanning procedures protects your organization from costly violations while it streamlines document management workflows (healthcare data breaches average $10.22 million per incident). The financial benefits of compliance far outweigh implementation costs. Your patients trust you with their most sensitive information, and robust procedures demonstrate your commitment to protect their privacy throughout the digital transformation process.
