Cyber attacks hit businesses every 39 seconds, with data breaches costing companies an average of $4.45 million in 2023. The threat landscape grows more sophisticated daily.
We at Scan N More understand that protecting your organization requires a comprehensive approach to cyber security and data privacy. This guide covers the essential strategies and tools you need to safeguard your digital assets.
What Cyber Threats Target Your Business Daily
Ransomware attacks now cost organizations an average of $1 million per incident according to Sophos, representing a 23% increase from 2022. These attacks encrypt your files and demand payment for restoration, with 65% of organizations experiencing at least one ransomware incident in the past year. Email delivers malware in 94% of cases per Verizon data, making your inbox the primary attack vector. Financially motivated threat actors drive 97% of cybercrimes, targeting businesses of all sizes with sophisticated tools.

Phishing Dominates Attack Methods
Phishing initiates 16% of all data breaches according to IBM research, making it the most common attack method. Spear phishing targets specific individuals using social media information and achieves higher success rates than generic campaigns. Business Email Compromise scams impersonate executives and cost organizations billions annually. Stanford research shows 88% of breaches stem from human error, with employees who click malicious links or download infected attachments. Man-in-the-middle attacks exploit unsecured Wi-Fi networks and intercept communications between parties. These attacks succeed because they exploit trust rather than technical vulnerabilities.
Identity Theft Through Data Breaches
Data breach identification takes an average of 181 days according to IBM, with containment that requires an additional 60 days. The Ticketmaster breach in 2024 exposed over 560 million customer records and demonstrated how large-scale incidents affect millions. US organizations face the highest breach costs at $10.22 million per incident. Zero-day exploits target unpatched vulnerabilities that exist for years before detection (Log4Shell affected 10% of global digital assets). Insider threats from employees create additional risks through both malicious intent and accidental exposure.
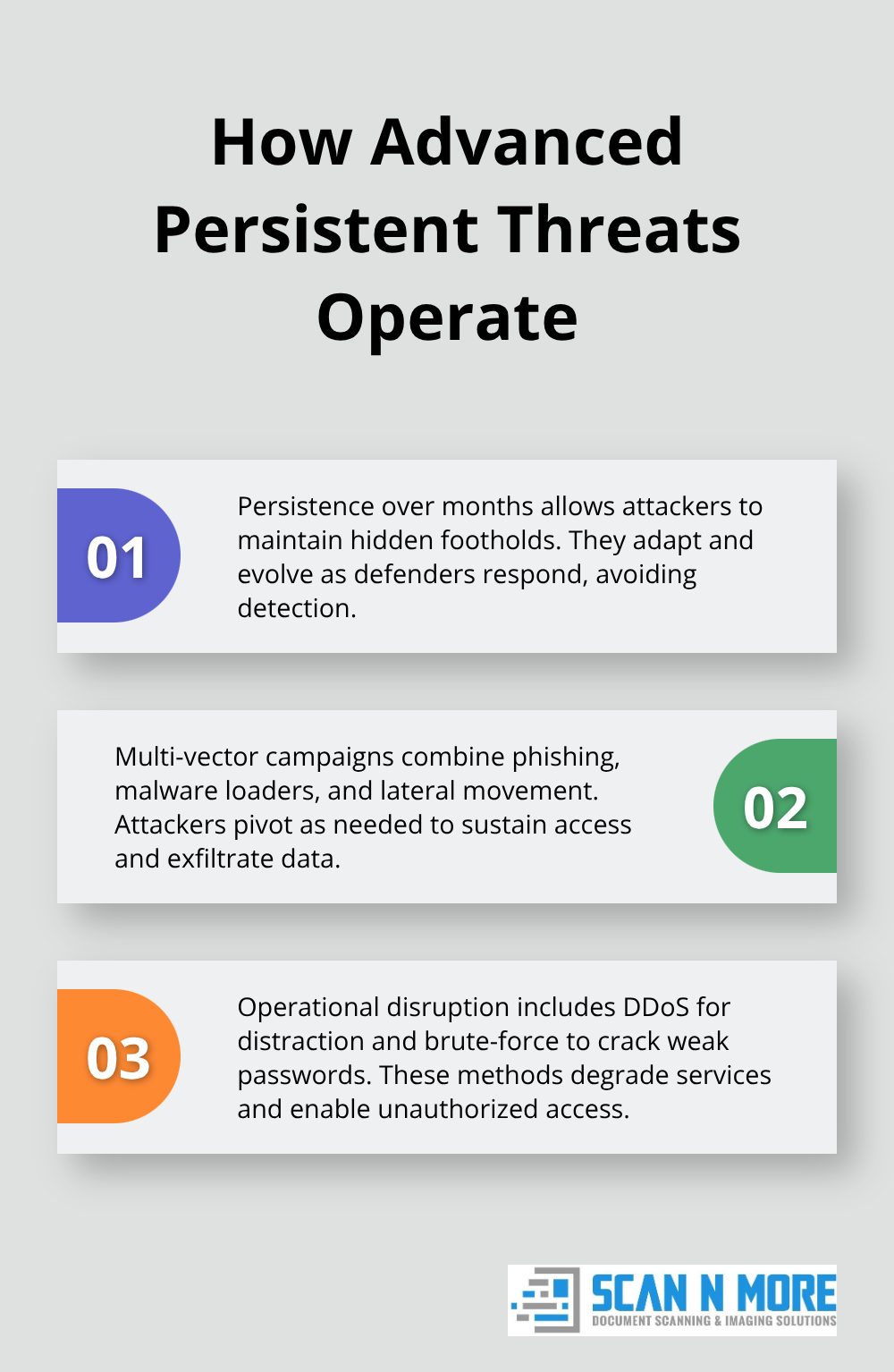
Advanced Persistent Threats
Sophisticated attackers establish long-term access to networks and remain undetected for months. These threats use multiple attack vectors and adapt their methods based on target responses. Distributed Denial-of-Service attacks overwhelm systems with traffic from botnets, causing service disruption that affects business operations. Brute force attacks systematically try different password combinations to gain unauthorized access to accounts.
Organizations need robust security measures to counter these evolving threats and protect their digital assets from compromise.
What Security Measures Actually Work
Multi-factor authentication reduces breach risk by 99.9% according to Microsoft data, making it the single most effective security control organizations can implement. Password-only access fails catastrophically when credentials get stolen in data breaches or phishing attacks. Organizations should implement MFA across all systems, starting with email, cloud services, and administrative accounts. Role-based access controls limit damage when accounts get compromised – employees should only access systems required for their specific job functions. The principle of least privilege means you grant minimum necessary permissions, not maximum convenience.
Security Audits Expose Hidden Vulnerabilities
Organizations without incident response plans represent 77% of companies according to Cybint research, which leaves them unprepared when attacks occur. Quarterly vulnerability assessments identify security gaps before attackers exploit them, while annual penetration tests simulate real-world attack scenarios. Third-party security assessments provide objective evaluation of your defenses and often reveal blind spots internal teams miss. Network segmentation prevents lateral movement during breaches – isolate critical systems from general user networks. Regular patch management addresses zero-day vulnerabilities that affect global digital assets.

Employee Training Stops Human Error
Human elements cause breaches, which makes employee education your most important investment. Monthly phishing simulations train staff to recognize social engineering attempts, while security awareness programs reduce successful attack rates. Teach employees to verify unusual requests through separate communication channels before they transfer money or share credentials. Insider threat programs monitor for suspicious behavior patterns and unauthorized access attempts. Security policies must include clear consequences for violations and regular updates that reflect new threat types.
Access Management Controls Risk
Zero Trust Architecture requires continuous verification of all users and devices, which enhances security against internal and external threats. Identity Access Management systems track user permissions and automatically revoke access when employees change roles or leave the organization. Privileged access management solutions monitor administrative accounts that pose the highest risk (these accounts can access sensitive systems and data). Regular access reviews identify orphaned accounts and excessive permissions that create security gaps.
Data privacy protection strategies build on these security foundations to create comprehensive protection for sensitive information.
How Do You Actually Protect Customer Data
GDPR violations result in significant financial penalties for companies, with non-compliance penalties that reach up to 4% of global revenue. Organizations must implement data minimization practices that collect only necessary information and delete data when retention periods expire. Privacy impact assessments identify risks before you process personal data, while data subject rights require automated systems to handle access, deletion, and portability requests. CCPA compliance affects any business that serves California residents and demands transparent privacy policies with opt-out mechanisms.
Regulatory Compliance Requirements
Data protection regulations impose strict requirements on how organizations collect, process, and store personal information. HIPAA compliance protects healthcare data with specific technical safeguards and access controls. Financial institutions must follow PCI DSS standards when they handle credit card information (these standards require encryption and secure networks). Organizations face severe penalties when they fail to meet regulatory requirements – Facebook paid $5 billion for privacy violations in 2019. Regular compliance audits help identify gaps before regulators discover them.
Encryption Standards That Actually Work
End-to-end encryption protects data during transmission and storage, which makes intercepted information unreadable to unauthorized parties. AES-256 encryption remains the gold standard for data protection, with quantum-resistant algorithms that become necessary as computers advance. Organizations should encrypt databases, backup systems, and cloud storage with separate encryption keys stored in hardware security modules. Data masking techniques allow testing and analysis without exposure of sensitive information, while tokenization replaces sensitive data with non-sensitive equivalents. Zero-knowledge architectures prevent even service providers from access to customer data.
Privacy by Design Implementation
Privacy by Default settings protect users automatically without configuration changes, while Privacy by Design embeds protection into systems from initial development. Organizations must conduct regular privacy audits to identify gaps and implement corrective measures before violations occur. Data anonymization techniques remove personally identifiable information while they preserve analytical value, and differential privacy adds mathematical noise to datasets to prevent individual identification. Staff training programs teach employees to recognize privacy risks and handle personal data according to established protocols. Privacy-preserving technologies like homomorphic encryption enable computation on encrypted data without decryption (this maintains confidentiality during processing operations).
Final Thoughts
Cybersecurity and data privacy protection demands immediate action rather than reactive responses. Multi-factor authentication reduces breach risk by 99.9%, while regular security audits expose vulnerabilities before attackers exploit them. Employee training programs address the human element that causes 88% of breaches, and encryption standards protect sensitive data during transmission and storage.
Organizations must implement comprehensive strategies that combine technical controls with regulatory compliance. GDPR and CCPA violations result in severe financial penalties, which makes privacy by design implementation essential for sustainable business operations (Zero Trust Architecture and role-based access controls limit damage when security incidents occur). The threat landscape evolves constantly, with ransomware costs that reach $1 million per incident and data breaches that take 181 days to identify.
Proactive measures cost significantly less than reactive damage control after successful attacks. We at Scan N More help organizations strengthen their digital protection through professional document scanning services that transform paper-based processes into secure digital solutions. Our services maintain data security and compliance while they reduce physical document vulnerabilities that create additional attack vectors for cybercriminals.
