Your old hard drives contain sensitive data that standard deletion can’t remove. Professional data recovery tools can retrieve supposedly erased files from improperly disposed drives.
We at Scan N More understand the serious risks businesses face when disposing of storage devices. A secure hard drive disposal service protects your organization from data breaches and compliance violations.
What Risks Do Improperly Disposed Hard Drives Create?
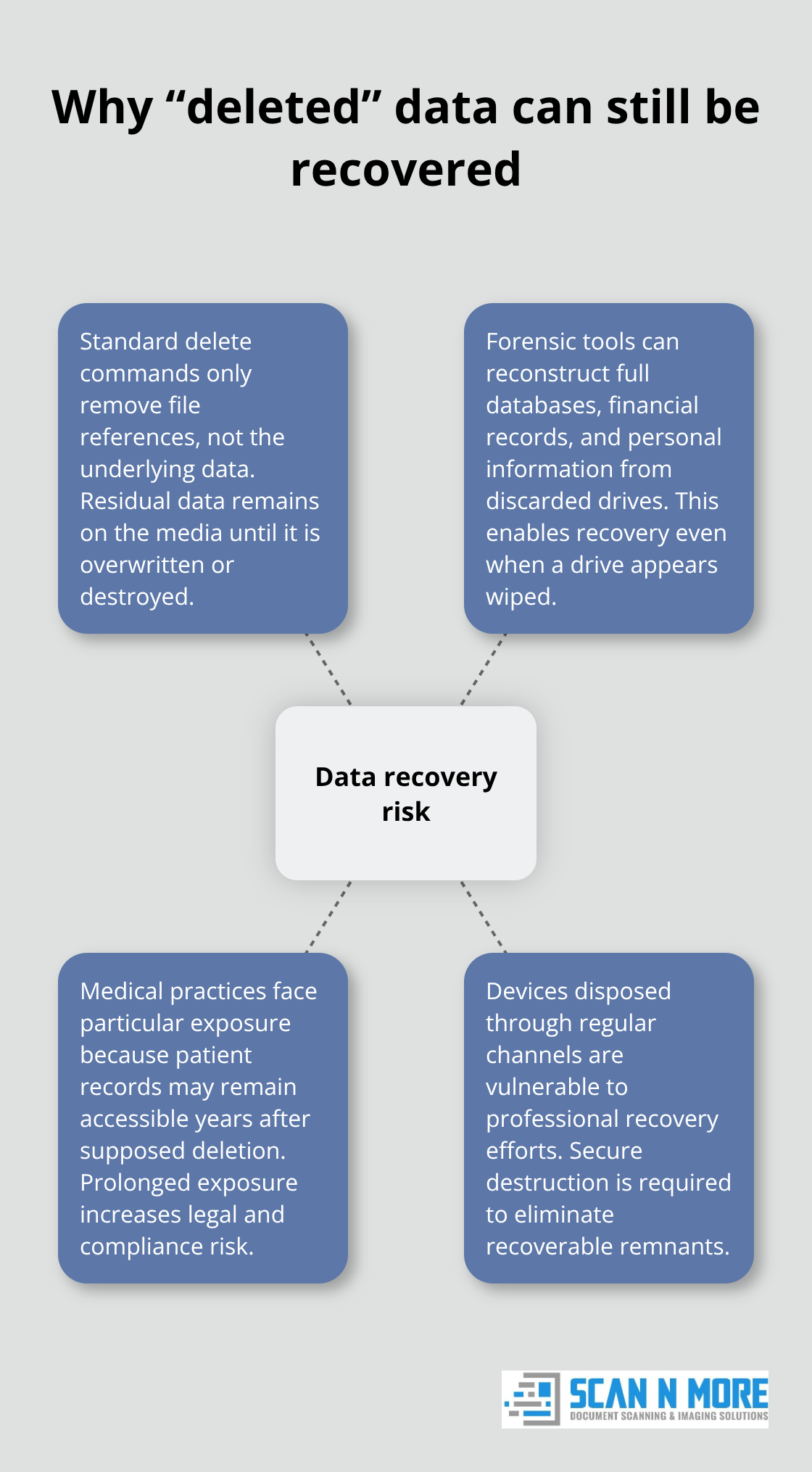
Data Recovery Technology Retrieves Supposedly Deleted Files
Professional data recovery firms retrieve files from hard drives even after standard deletion or formatting. Consumer victims reported total cybercrime-related losses of $4.2 billion in 2020, which was up to 69 percent from 2019, according to the FBI. Companies like Kroll Ontrack successfully recover data from drives that appear completely wiped.
Standard delete commands only remove file references, not the actual data. Forensic tools reconstruct entire databases, financial records, and personal information from drives disposed through regular channels. Medical practices face particular exposure since patient records remain accessible years after supposed deletion.
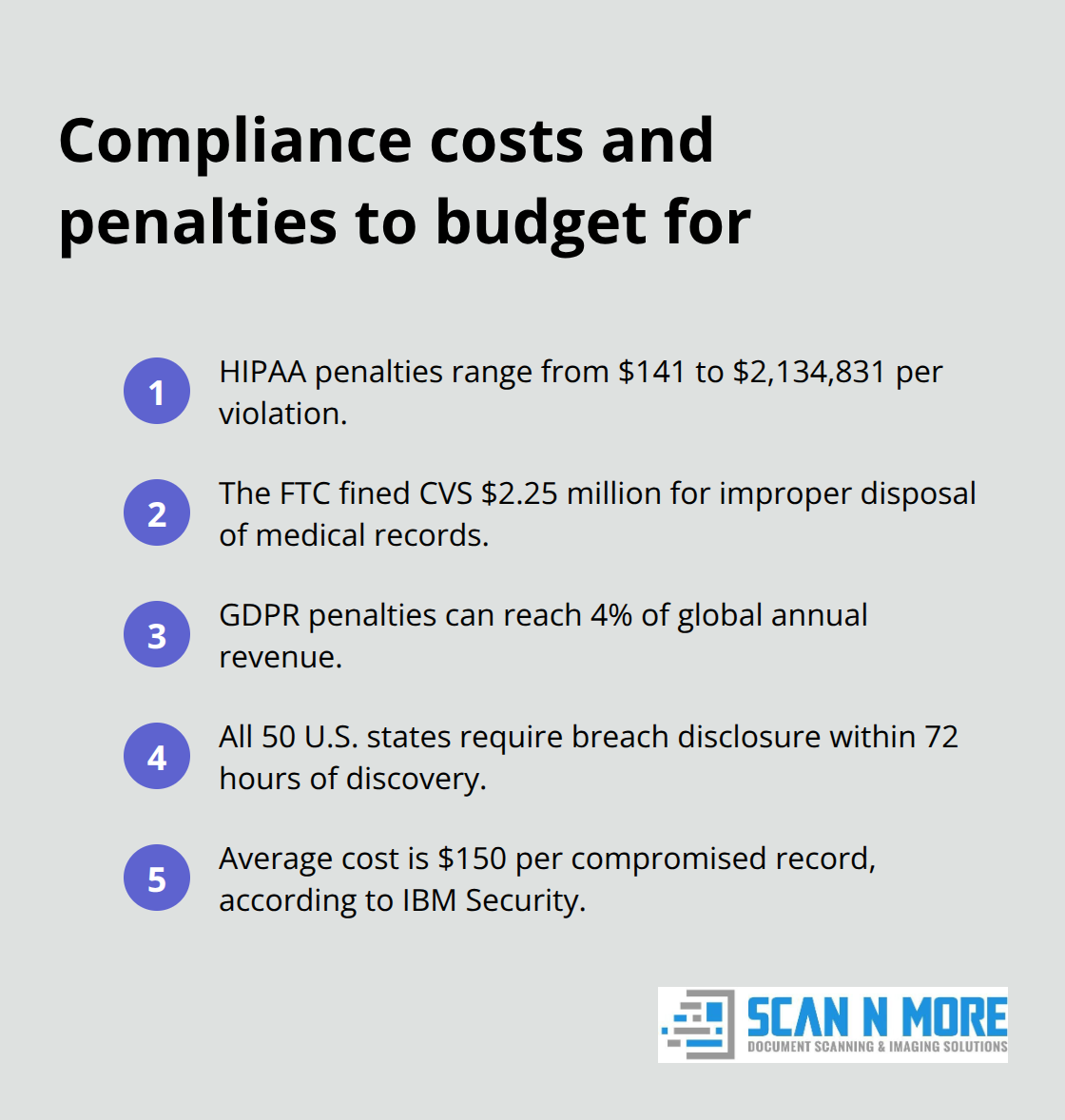
Compliance Violations Result in Massive Financial Penalties
The penalties for HIPAA violations include civil monetary penalties ranging from $141 to $2,134,831 per violation, depending on the level of culpability. The Federal Trade Commission fined CVS $2.25 million for disposal of prescription bottles and medical records in dumpsters (without proper data destruction protocols).
GDPR penalties reach 4% of global annual revenue for data protection failures. Financial institutions face Gramm-Leach-Bliley Act violations when customer data from disposed drives surfaces. State breach notification laws in all 50 states require public disclosure within 72 hours of discovery. Companies spend an average of $150 per compromised record according to IBM Security research.
Reputation Damage Exceeds Financial Penalties
Target lost 70 million customers permanently after their 2013 data breach became public knowledge. Stock prices typically drop 7.5% immediately after breach announcements and take two years to recover fully. Healthcare organizations lose 6% of their patient base permanently after data incidents.
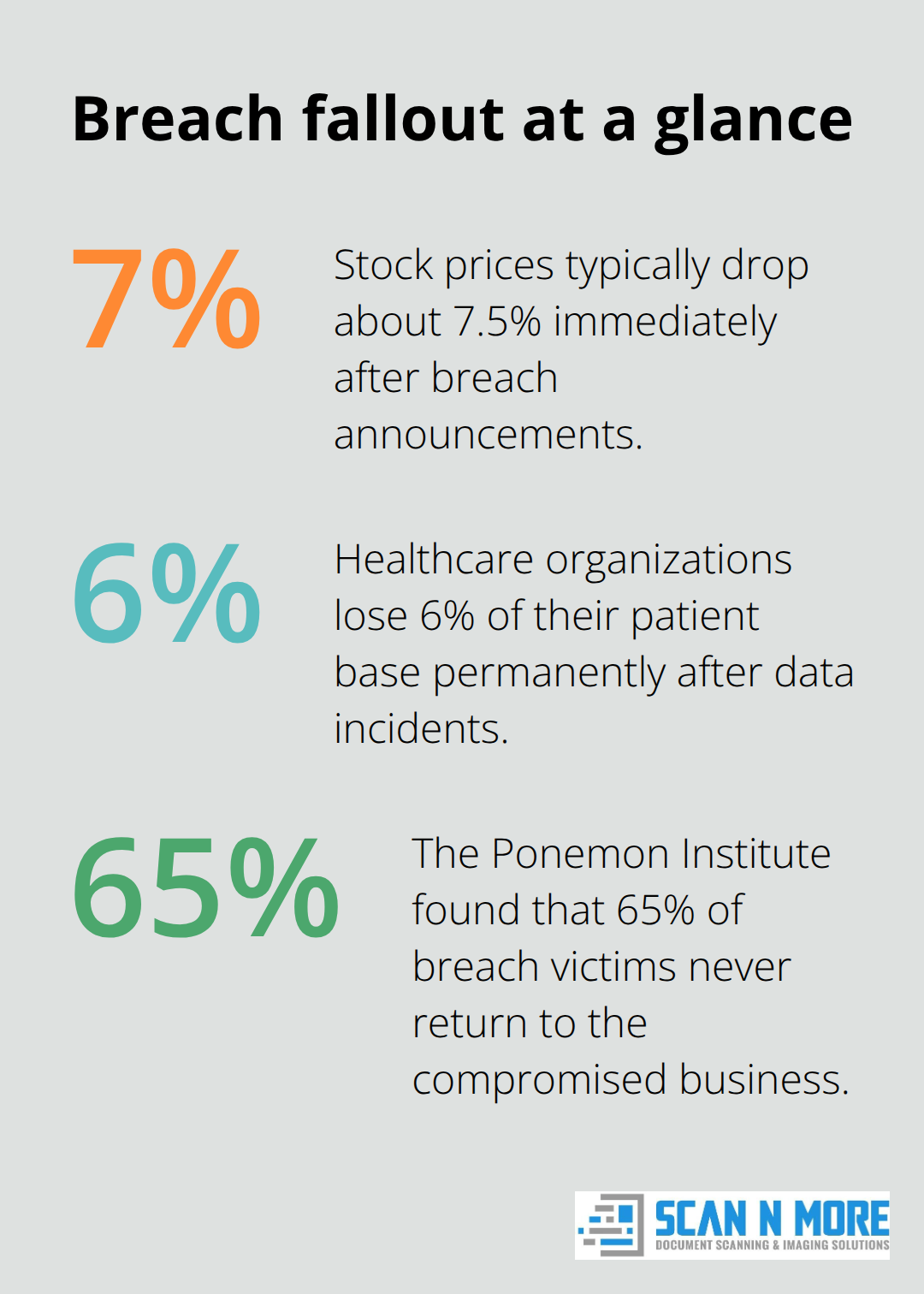
Law firms face malpractice claims when client information from disposed drives reaches competitors or opposing counsel. The Ponemon Institute found that 65% of breach victims never return to the compromised business. Professional service firms lose major contracts when disposal incidents damage their security reputation (particularly in competitive industries).
These risks make professional hard drive destruction services essential for any organization that handles sensitive data.
What Professional Features Should You Expect
NAID AAA certification verifies secure data destruction companies’ services’ compliance with all known data protection laws through scheduled and surprise audits. The National Association for Information Destruction requires providers to pass rigorous audits that cover operational security, employee background checks, and destruction processes. NIST Special Publication 800-88 compliance assists organizations and system owners in making practical sanitization decisions based on the categorization of confidentiality. Providers must demonstrate three destruction levels: clear for internal reuse, purge for external transfer, and destroy for end-of-life disposal.
Documentation Requirements Protect Against Legal Exposure
Professional services provide Certificate of Destruction within 48 hours of completion. This document includes serial numbers, destruction method, date, location, and witness signatures. The certificate serves as legal proof for compliance audits and regulatory investigations. Chain of custody documentation tracks every step from pickup to final destruction. GPS systems monitor transport vehicles while tamper-evident seals protect drives during transit (eliminating unauthorized access risks). Video surveillance records the actual destruction process at certified facilities. Companies like Iron Mountain maintain these records for seven years minimum to support legal defense strategies.
Location Choice Impacts Security and Cost
On-site destruction costs 40% more than off-site services but eliminates transport risks entirely. Mobile units arrive at your facility and destroy drives while you observe the process. This option works best for organizations with 50+ drives that require destruction quarterly. Off-site destruction at certified facilities costs less and handles larger volumes efficiently. However, drives must travel in secured vehicles with GPS monitoring and armed escort services for high-security clients (particularly government contractors). Degaussing followed by physical destruction provides the strongest protection regardless of location choice.
Staff Verification Standards Matter
Certified providers conduct comprehensive background checks on all employees who handle client data. These checks include criminal history, employment verification, and credit reports for financial responsibility assessment. Staff members sign confidentiality agreements and receive annual security training updates. The best providers require employees to pass drug screenings and maintain security clearances when handling government or healthcare data.
When you evaluate potential providers, these professional features separate legitimate services from basic disposal companies that lack proper security protocols.
How Do You Verify Provider Credentials
Check Multiple Industry Certifications
NAID AAA certification represents the gold standard for data destruction companies. This certification verifies that data destruction service providers meet stringent requirements for operational security, employee screening, and destruction processes through annual audits. Providers must also hold R2 or e-Stewards certification for environmental compliance, which covers responsible recycling of electronic components after destruction.
ISO 27001 certification demonstrates information security management system compliance. SOC 2 Type II reports verify internal controls for security and availability. Companies like ERI maintain all four certifications simultaneously, which proves comprehensive operational standards. Request current certificates directly from providers since expired certifications indicate poor operational standards.
Evaluate Security Infrastructure Standards
Professional providers conduct FBI background checks on all employees who handle client data. These checks include criminal history searches and employment verification. Staff must sign confidentiality agreements with financial penalties for violations and undergo annual security training updates with documented completion records.
Facilities require 24/7 surveillance systems with motion detectors and access control systems that log every entry and exit. The best providers maintain security clearances for government contracts and require drug tests for employees who handle sensitive healthcare or financial data.
Assess Personnel Verification Protocols
Iron Mountain employs armed guards at destruction facilities and uses GPS tracking on all transport vehicles with real-time monitoring capabilities. Professional services verify employee backgrounds through comprehensive screening processes that include credit reports for financial responsibility assessment.
Staff members receive annual security training updates and must pass drug screenings when they handle government or healthcare data. The strongest providers require employees to maintain active security clearances (particularly for defense contractors and healthcare organizations).
Compare Transparent Pricing Models
Reputable providers offer fixed pricing based on drive quantity and destruction method. This approach eliminates surprise fees during service delivery. On-site destruction typically costs $15-25 per drive while off-site services range from $8-15 per drive depending on volume and security requirements.
Providers should itemize transportation costs, certificate preparation fees, and any expedited service charges upfront. The strongest providers guarantee destruction within 48 hours of pickup and deliver certificates within 24 hours of completion. Avoid companies that quote prices significantly below market rates since proper security measures require substantial operational investments.
Final Thoughts
Professional hard drive disposal service selection protects your organization from devastating data breaches and compliance violations. Financial penalties for improper disposal reach millions of dollars while reputation damage often proves irreversible. Companies that choose certified providers with NAID AAA credentials and comprehensive security protocols avoid these catastrophic risks.
Certified service providers deliver measurable benefits beyond compliance protection. Professional destruction methods guarantee complete data elimination while proper documentation shields your organization during regulatory audits. Chain of custody tracking and video surveillance provide legal proof that sensitive information received proper handling throughout the disposal process.
Your next step involves evaluating potential providers against the certification and security standards outlined in this guide. Request current certificates, verify employee background check protocols, and compare transparent pricing models before you make your selection (particularly for high-volume disposal needs). We at Scan N More understand the importance of comprehensive data security solutions that protect your organization’s sensitive information.
