Data breaches cost companies an average of $4.45 million in 2023, making compliance with data security compliance standards more important than ever. Organizations face mounting pressure from regulators worldwide to protect sensitive information.
We at Scan N More understand that meeting these requirements can feel overwhelming. This guide breaks down the essential standards and provides actionable steps to achieve compliance.
Which Compliance Standards Matter Most
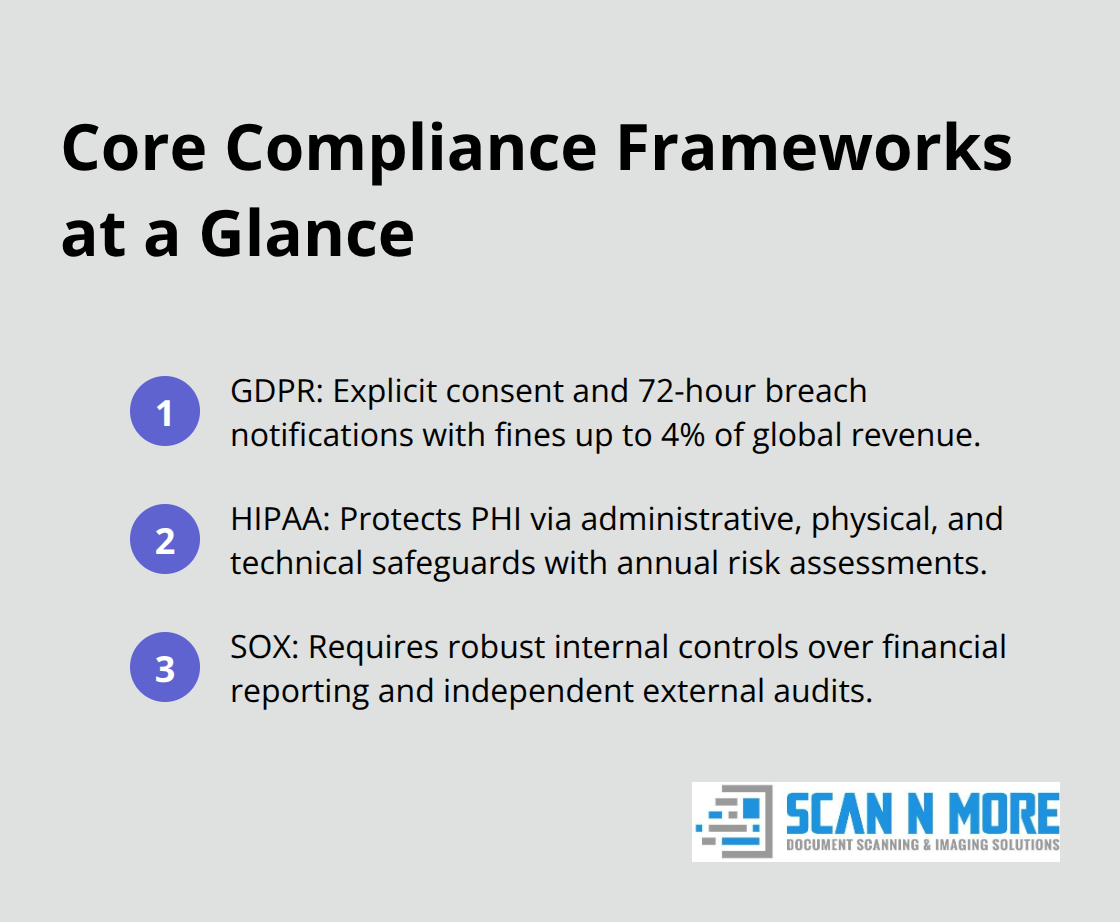
Organizations handle three main types of sensitive data, each governed by specific regulations that carry severe penalties for violations. The General Data Protection Regulation affects any business that processes EU citizens’ personal information, requires explicit consent and mandates breach notifications within 72 hours. GDPR fines reached €1.6 billion in 2023 according to European Data Protection Board statistics, with penalties up to 4% of annual global revenue.
Healthcare organizations must comply with HIPAA, which protects patient health information through administrative, physical, and technical safeguards. HIPAA violations are tracked by the HHS Office for Civil Rights, which maintains records of all breaches reported within the last 24 months that are currently under investigation. Financial institutions face Sarbanes-Oxley requirements that mandate internal controls over financial reporting and data integrity. SOX non-compliance can result in criminal charges, with executives who face up to 20 years imprisonment for willful violations. These three frameworks form the foundation of most compliance programs, and organizations often need multiple certifications based on their industry and customer base.
GDPR Personal Data Protection Requirements
GDPR applies to any organization that processes personal data of EU residents, regardless of company location. The regulation defines personal data broadly (including IP addresses, device identifiers, and location data). Organizations must implement privacy by design, conduct data protection impact assessments for high-risk activities, and appoint a Data Protection Officer when required. The right to be forgotten requires companies to delete personal data upon request within one month, while data portability mandates that companies provide user data in machine-readable formats.
HIPAA Healthcare Information Standards
HIPAA covers healthcare providers, health plans, and business associates who handle protected health information. The Security Rule requires encryption for data in transit and at rest, unique user identification for system access, and automatic logoff procedures. Healthcare organizations must conduct annual risk assessments and maintain audit logs for all PHI access. Business associate agreements are mandatory for third-party vendors (making them equally liable for HIPAA violations).
SOX Financial Data Security Rules
SOX Section 404 requires public companies to assess internal controls over financial reporting annually. IT general controls must cover data center operations, system access, program changes, and program development. Companies need documented procedures for financial data access, change management processes, and separation of duties. External auditors must evaluate these controls independently, and management must certify their effectiveness quarterly.
Understanding these core standards provides the foundation for compliance, but organizations face significant challenges when they attempt to implement these requirements across complex business environments.
What Makes Compliance So Difficult
Most organizations struggle with compliance because they underestimate the complexity of managing regulations across different jurisdictions and integrating new requirements into existing systems. A Ponemon Institute study found that companies face significant challenges with their compliance efforts, primarily due to inadequate preparation and system integration issues. The challenge becomes exponentially harder when organizations operate globally, as they must navigate conflicting requirements between regions while maintaining consistent security standards.
Multiple Legal Frameworks Create Conflicts
Organizations that operate across borders face the nightmare of reconciling conflicting regulations that often contradict each other. GDPR requires data to remain within EU borders, while Chinese data localization laws mandate that certain data stays in China (creating impossible situations for multinational companies). Research indicates that a focused national data privacy law would cost about $6 billion per year to maintain compliance across multiple jurisdictions. Smart organizations pick one strict standard like GDPR and apply it globally rather than try to customize compliance for each region. This approach reduces complexity and training costs while it maintains the highest protection standards everywhere.
Legacy Systems Block Modern Compliance
Retrofitting compliance controls into existing systems costs 300% more than building compliance into new systems from the ground up, according to Gartner research. Most organizations discover that their current databases, access controls, and monitoring tools cannot support modern compliance requirements without major overhauls. The biggest mistake companies make is that they try to patch compliance onto legacy systems instead of replacing them entirely. Organizations that invest in modern, compliance-ready infrastructure see 40% lower ongoing compliance costs and pass audits at twice the rate of companies that use retrofitted systems.
Traditional Training Methods Fail Employees
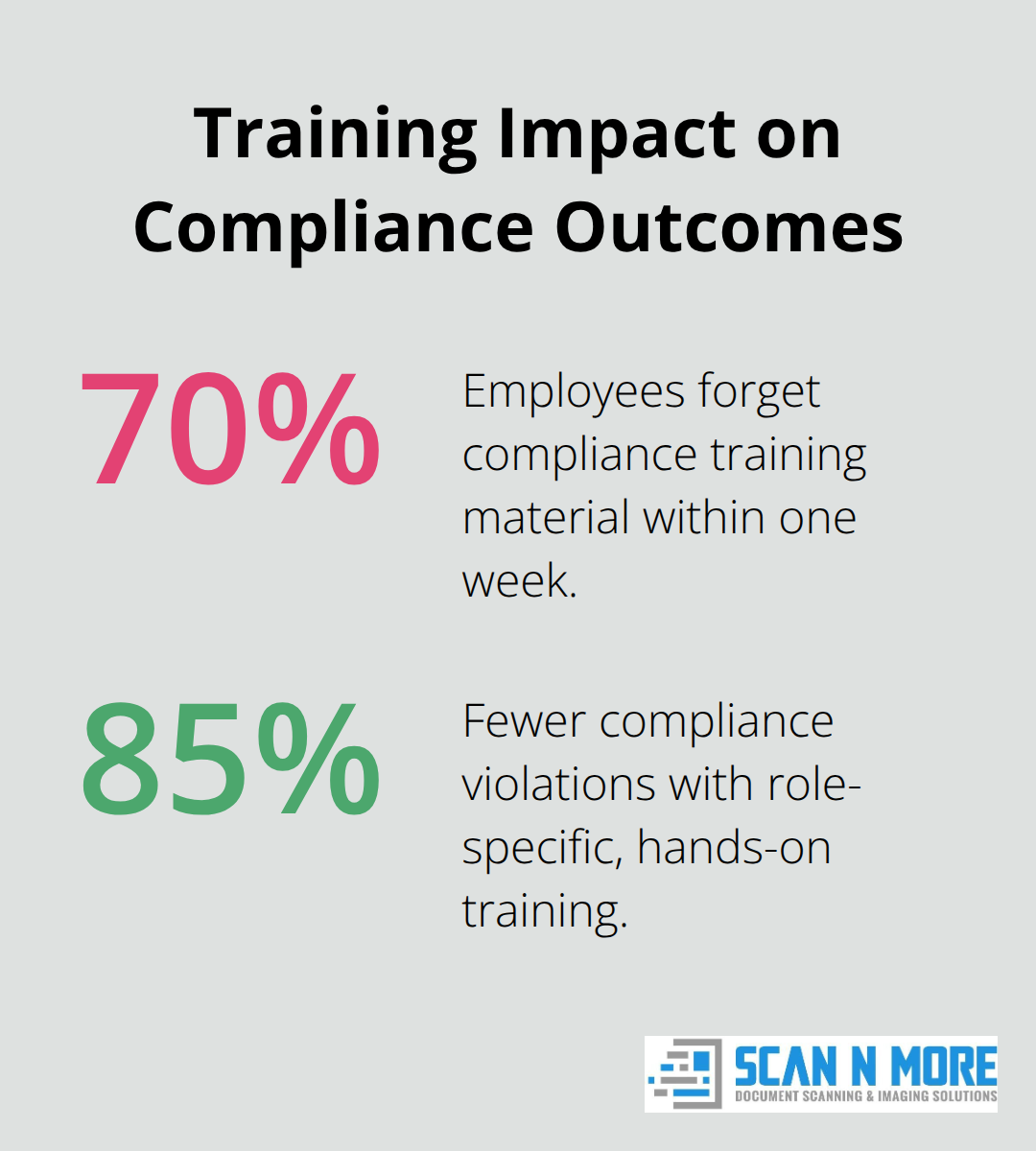
Traditional compliance training fails because 70% of employees forget the material within one week, according to McKinsey research. Most organizations waste money on generic online courses that employees click through without learning anything useful. Effective compliance training requires hands-on practice with real data scenarios, monthly refresher sessions, and immediate consequences for violations. Companies that implement role-specific training see 85% fewer compliance violations compared to those that use one-size-fits-all approaches.
Organizations that skip compliance gap assessments face 3x higher regulatory penalties when violations occur.
These compliance challenges demand strategic solutions that address both technical infrastructure and human factors. The next section explores proven practices that help organizations overcome these obstacles and maintain consistent compliance across their operations.
How Do You Build Bulletproof Compliance Systems
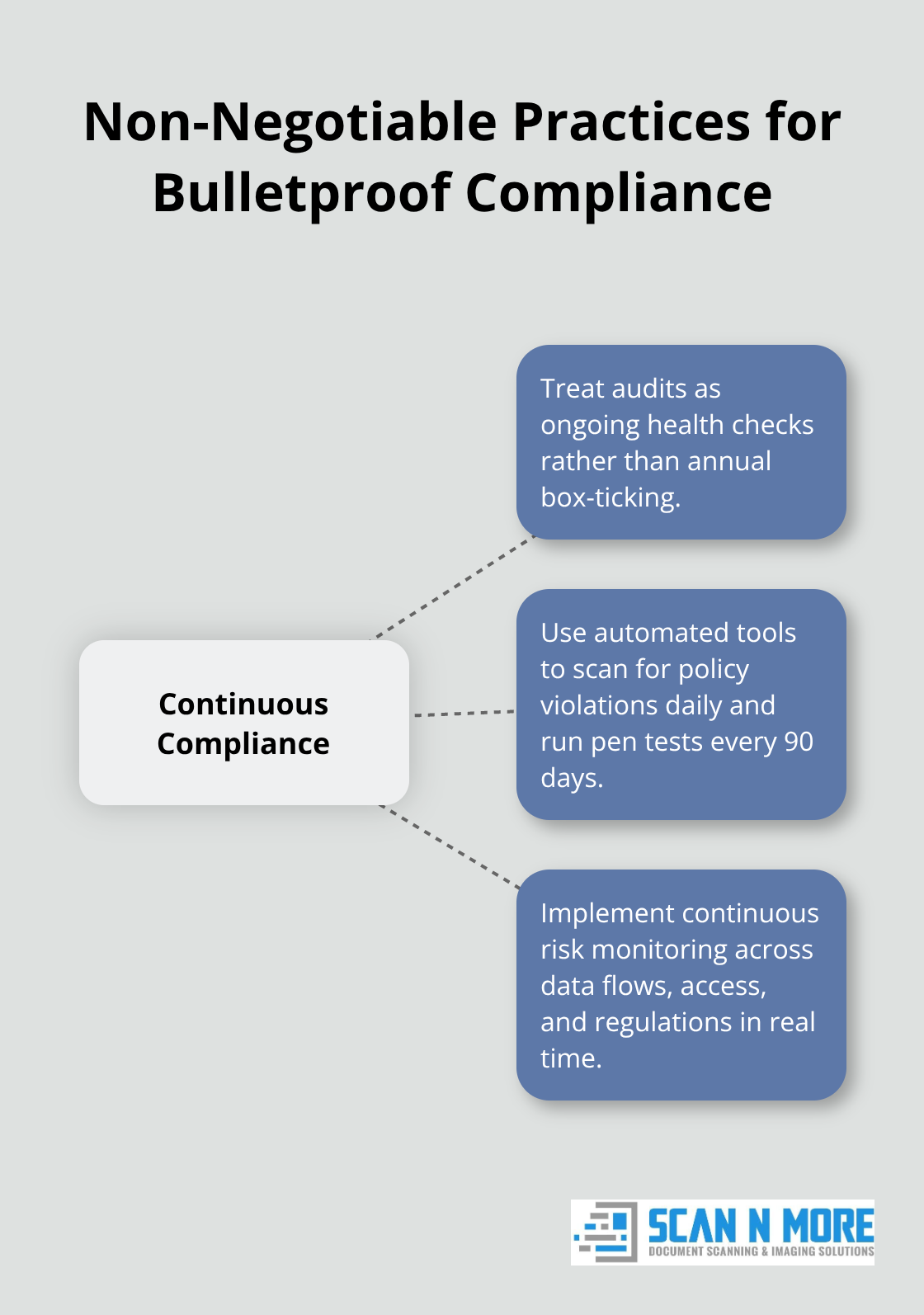
Successful compliance depends on three non-negotiable practices that organizations must implement systematically rather than sporadically. Companies that conduct quarterly security audits instead of annual reviews provide more frequent oversight, though only 15 percent are using automated risk impact assessments according to Ponemon Institute research. The most effective organizations treat audits as ongoing health checks rather than yearly box-ticking exercises. They use automated tools to scan for policy violations daily and conduct penetration tests every 90 days. Smart organizations also implement continuous risk monitoring that tracks changes in data flow, system access, and regulatory requirements in real-time rather than wait for scheduled assessments.
Data Classification Prevents Most Violations
Organizations that implement automated data classification systems benefit from improved compliance management, though regulatory challenges continue to grow with AI regulatory violations expected to result in a 30% increase in legal disputes for tech companies by 2028 according to Gartner. The key lies in tagging every piece of data at creation with sensitivity levels, retention requirements, and access permissions rather than trying to classify existing data retroactively. Companies should establish four classification tiers: public, internal, confidential, and restricted (with each tier having specific handling requirements and access controls). Automated tools can scan databases, file systems, and email archives to identify sensitive information like social security numbers, credit card data, and health records without human intervention. Organizations that combine data classification with role-based access controls reduce unauthorized data access significantly within six months of implementation.
Incident Response Speed Determines Penalties
Organizations with documented incident response plans that practice quarterly drills face lower regulatory fines when breaches occur, according to IBM Security research. The most successful companies maintain pre-written breach notification templates for each regulatory framework, legal contact lists updated monthly, and communication protocols that activate within 15 minutes of incident detection. Companies should establish detection thresholds that trigger automatic alerts when unusual data access patterns occur (rather than wait for manual discovery of potential breaches). Organizations that notify regulators within 24 hours of breach discovery receive significantly reduced penalties compared to those that delay reporting beyond regulatory deadlines.
Automated Monitoring Catches Violations Early
Real-time compliance monitoring systems detect policy violations faster than manual audits, according to Forrester research. Organizations that deploy automated compliance tools can track data access patterns, policy changes, and system configurations continuously rather than rely on periodic reviews. These systems flag suspicious activities immediately and generate compliance reports automatically for regulatory submissions. Companies that invest in automated monitoring reduce compliance management costs while they maintain higher security standards than organizations that use manual processes.
Final Thoughts
Data security compliance standards represent a fundamental business requirement rather than an optional security enhancement. Organizations that implement GDPR, HIPAA, and SOX frameworks systematically reduce their breach costs by millions while they avoid regulatory penalties that can reach 4% of annual revenue. Proactive security measures deliver measurable returns through reduced incident response costs, faster audit completions, and enhanced customer trust.
Companies that invest in automated monitoring, data classification, and regular risk assessments outperform reactive organizations that wait for violations to occur. Organizations need comprehensive data audits to identify sensitive information across all systems first. We at Scan N More provide professional document scanning services that transform paper-based processes into secure digital solutions (helping organizations maintain data security and compliance while enhancing operational efficiency).
The next step involves selecting compliance frameworks that match your industry requirements and implementing automated tools for continuous monitoring. Organizations that treat compliance as an ongoing process rather than a one-time project achieve better security outcomes. These companies face fewer regulatory challenges over time and maintain stronger competitive positions in their markets.
