Most businesses still keep sensitive documents lying around without proper controls, creating unnecessary risk. At Scan N More, we’ve seen firsthand how document scanning and shredding done right protects your company from data breaches, compliance violations, and costly mistakes.
This guide walks you through the complete process-from preparing documents for digitization to certified destruction methods-so you can eliminate paper-based vulnerabilities and build a secure digital system.
Why Your Business Needs Secure Document Management
Data Breaches Hit Hard-And Often
Data breaches affecting companies with poor document controls cost an average of USD 4.88 million per incident, according to IBM’s 2024 Data Breach Report. That figure covers forensic investigation, legal fees, regulatory fines, and lost customer trust. A single compromised customer record triggers notification requirements under state laws, HIPAA for healthcare organizations, or GDPR data protection requirements for any business handling EU residents’ data. The FTC’s disposal rule mandates that you destroy documents containing personal information using methods that provide reasonable protection against unauthorized access. Without proper controls, you gamble with your company’s finances and reputation.
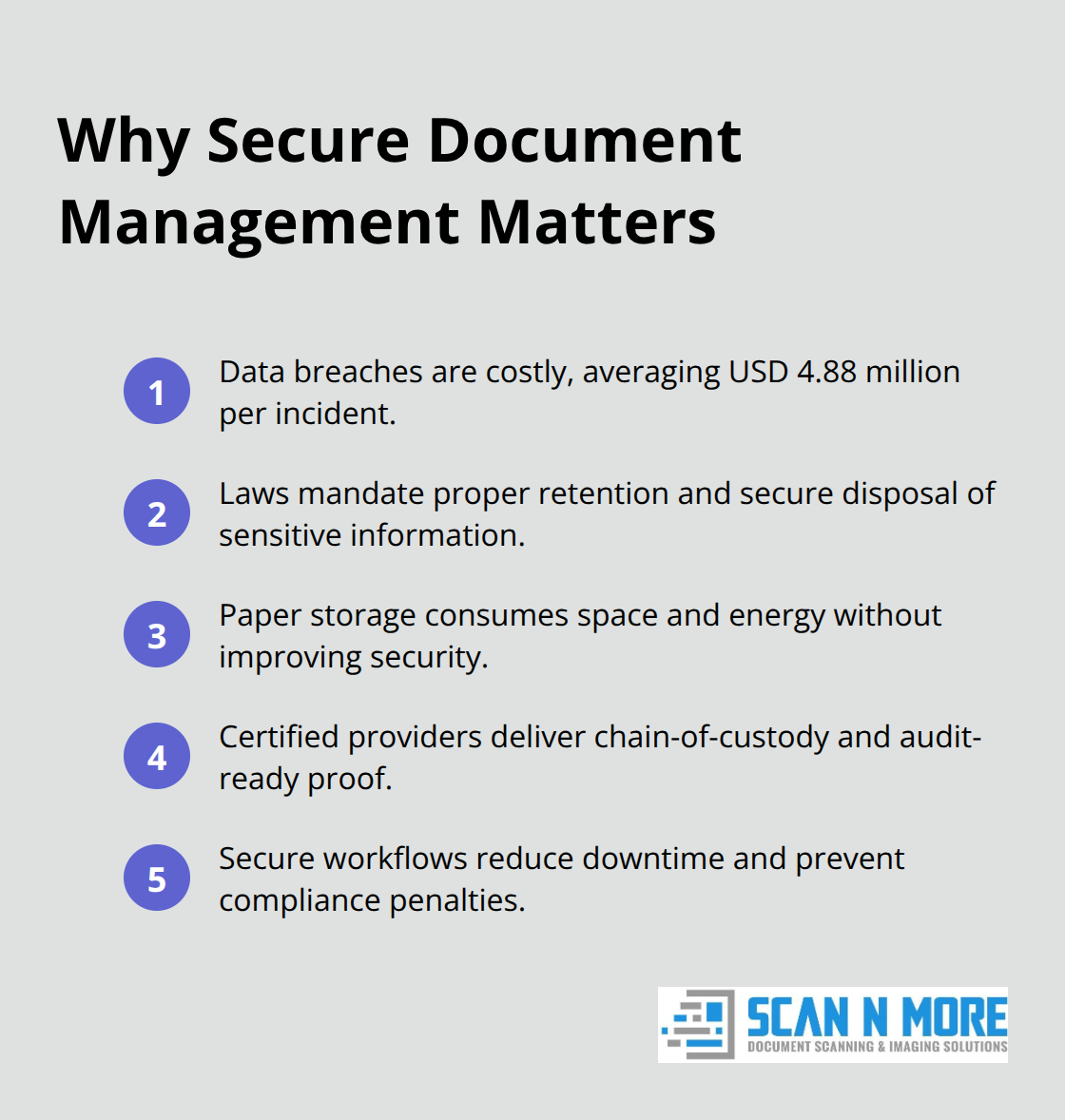
Regulatory Requirements Demand Action
Companies in regulated industries face steep compliance obligations. Healthcare providers must retain patient records for specific periods under state law-seven years from the last treatment in Texas, for example. Financial institutions fall under Gramm-Leach-Bliley Act requirements, while any company handling aircraft maintenance records must keep them for at least one year per FAA regulations. Non-compliance with these standards results in penalties that far exceed the cost of proper document management.
The Hidden Costs of Incomplete Destruction
Incomplete shredding and poorly organized digital files create openings for identity theft and fraud that extend far beyond the initial breach. A customer’s exposed medical record or financial information doesn’t just damage your business immediately-it exposes you to years of liability if that information surfaces in criminal activity. Employees whose personal data leaks from your systems face identity theft and reputational harm, increasing turnover and damaging workplace morale.
Environmental and Operational Benefits
The environmental argument for digitization adds another layer of urgency. More than 15 billion trees are cut down annually to produce paper globally, and storing physical documents consumes ongoing energy and physical space in your office. Switching to secure digital systems reduces your carbon footprint while freeing valuable square footage that your team could use productively instead of filing cabinets.
Professional Services Eliminate Vulnerabilities
Professional document scanning combined with certified destruction methods eliminates the vulnerabilities that come with DIY approaches. Certified shredding providers maintain chain-of-custody documentation and provide certificates of destruction that prove compliance during audits. Cross-cut shredding technology reduces documents to particles too small to reconstruct, far more effective than strip-cut methods that leave readable fragments. When you pair digitization with secure destruction, you create a complete lifecycle that meets regulatory requirements while improving daily operations. Your team gains instant access to searchable digital files from anywhere, reducing the time wasted hunting through filing systems for a single document. Understanding how to prepare your documents for this transformation is the next critical step.
How to Execute Scanning and Shredding Without Gaps
Assess and Classify Your Documents First
Starting the process requires honest assessment of what you actually own. Most businesses underestimate their document volume until they begin sorting. Classify documents into three categories: keep indefinitely for legal or operational reasons, scan and retain digitally, or destroy immediately. Healthcare providers must retain patient records for seven years from the last treatment under Texas law, while financial institutions must follow Gramm-Leach-Bliley retention schedules. Before scanning begins, remove staples, paper clips, and damaged pages that jam equipment-this single step prevents costly delays. Organize documents chronologically or by department to streamline the scanning workflow and maintain consistent indexing. Establish a temporary holding area with restricted access where documents await digitization, preventing unauthorized handling during the transition phase.
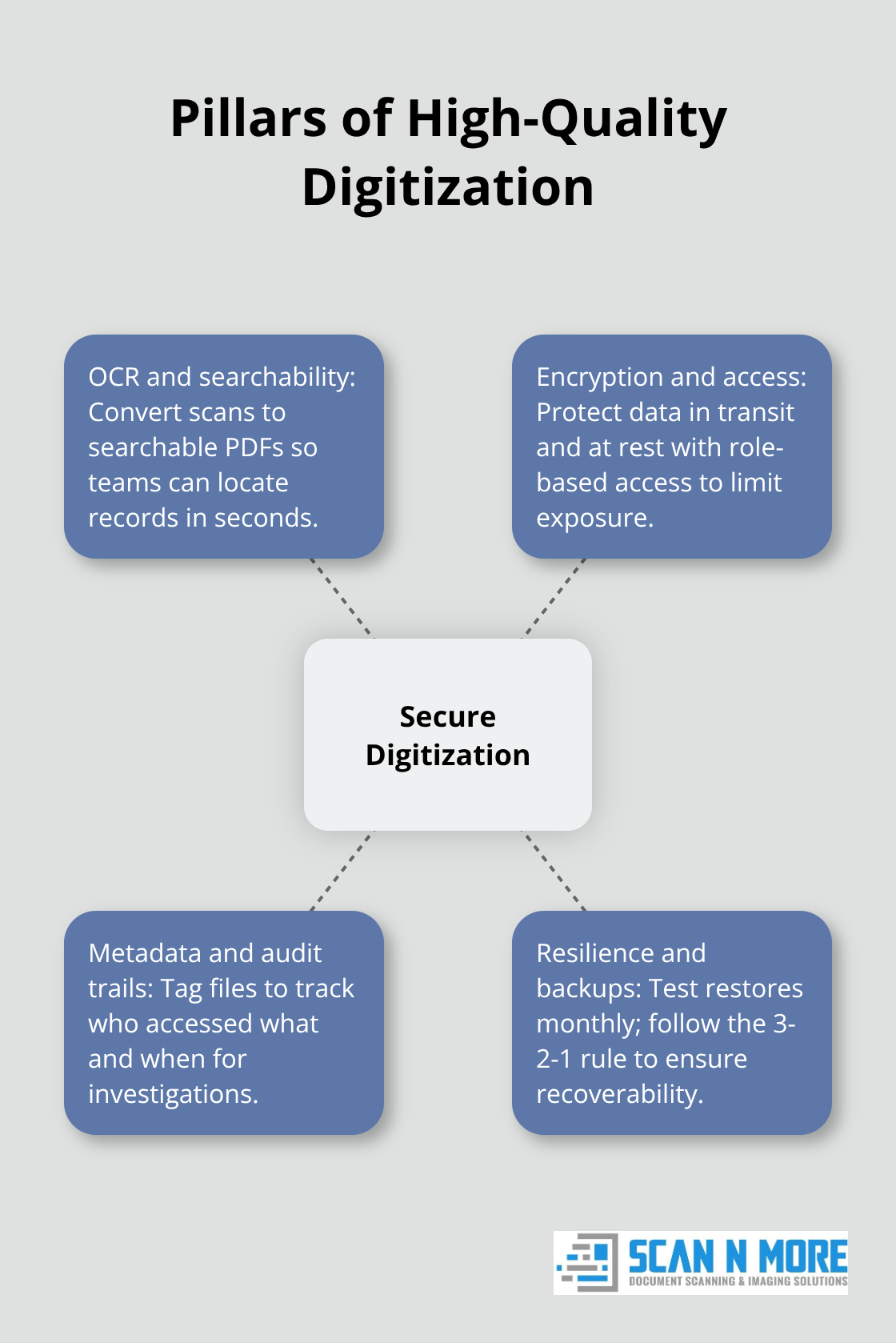
Prepare Documents for High-Quality Digitization
High-quality digitization means more than snapping photos with a smartphone. Professional scanning produces searchable PDFs through optical character recognition, allowing your team to locate customer invoices or compliance records in seconds rather than hours. Cloud-based storage with encryption in transit and at rest protects scanned files from interception, while role-based access controls ensure only authorized personnel view sensitive information. Automated metadata tagging during scanning enables audit trails that prove which employee accessed a customer record and when-critical documentation during regulatory investigations. Test restore procedures monthly to verify your backup systems actually work when disaster strikes; the 3-2-1 backup rule demands three copies on two different media types with one stored off-site.
Implement Certified Destruction Methods
Certified destruction providers maintain documented chain-of-custody from collection through shredding, providing certificates of destruction that satisfy auditors and regulators. NAID AAA-certified shredding services help businesses verify that a shredding provider meets strict disposal standards. Cross-cut shredding reduces paper to fragments approximately 2mm x 15mm, making reconstruction virtually impossible compared to strip-cut methods that leave readable strips. Request certificates detailing the destruction date, method, location, and quantity destroyed; retain these records for your compliance files. If your business handles healthcare data, demand HIPAA-compliant destruction with written proof from the vendor confirming their compliance certifications. One-time bulk shredding works for initial purges when transitioning from paper to digital, while scheduled recurring services prevent document accumulation that creates vulnerability windows. Hard drive destruction requires NIST SP 800-88 standards ensuring data is cleared, purged, or physically destroyed when decommissioning IT equipment-simple deletion leaves recoverable fragments. The cost varies from roughly $30 for basic office shredders to several thousand for high-security equipment, but outsourcing to certified providers eliminates the ongoing maintenance burden and guarantees legal compliance. With your documents scanned and destroyed, the next phase focuses on building systems that keep your digital files organized and accessible to the right people.
Common Mistakes That Expose Your Sensitive Data
Paper Documents Need Physical Controls, Not Just Good Intentions
Most businesses fail at document management not because they lack good intentions, but because they skip foundational steps that seem tedious. Storing paper documents without proper physical controls remains the most widespread vulnerability. You cannot simply stack boxes of financial records, patient files, or customer contracts in a storage closet and assume they’re safe. That approach invites theft, accidental exposure during renovations, and unauthorized access by employees who shouldn’t see the information. Establish a locked, logged storage area where only authorized personnel can retrieve documents. Track who accesses what and when through a simple sign-in sheet or digital log. More importantly, set a destruction deadline for every document the moment it arrives in your system.
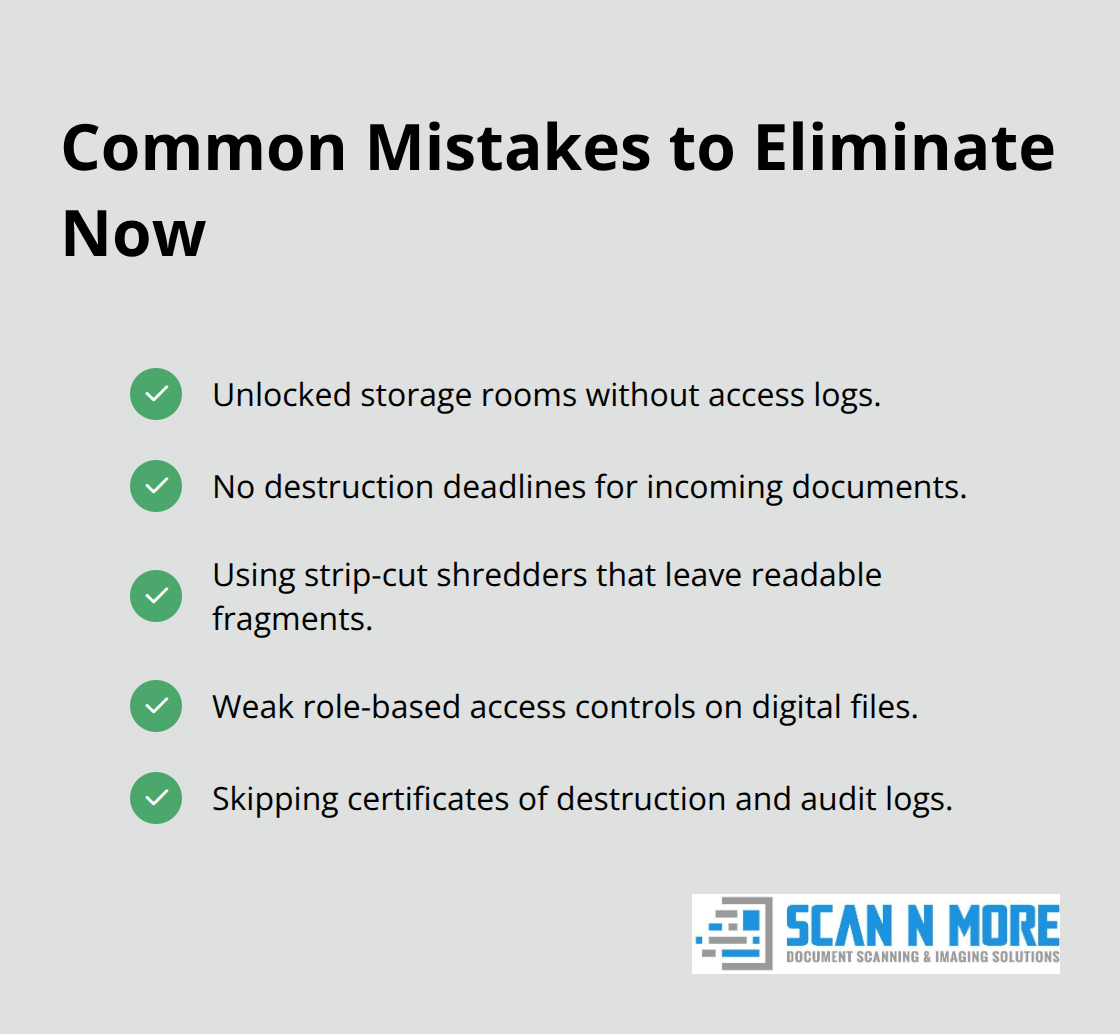
If a contract must be retained for three years, mark that date clearly and schedule shredding automatically rather than waiting until someone remembers the file exists. Without these controls, sensitive documents languish indefinitely, creating windows of vulnerability that multiply with each passing month.
Strip-cut shredders Leave Readable Fragments Behind
Incomplete shredding exposes your organization to serious risk that many businesses discover only after a breach occurs. Strip-cut shredders leave readable fragments that determined thieves can reconstruct to recover bank account numbers or medical information. Cross-cut shredding reduces documents to particles too small to piece together, yet many businesses purchase cheap equipment without understanding this critical difference. If you handle healthcare data subject to HIPAA, incomplete destruction violates federal law and exposes your organization to penalties exceeding $100,000 per violation. Certified shredding providers maintain detailed logs, provide certificates of destruction, and offer audit trail documentation that satisfy auditors and regulators. The cost of certified destruction services typically ranges from $50 to $300 per box depending on volume and frequency-a modest investment compared to the financial and reputational damage from a data breach.
Weak Access Controls Turn Digital Files Into Open Secrets
Digital files present a separate problem when access controls are weak or nonexistent. Storing scanned documents in shared folders accessible to every employee means a disgruntled worker can download payroll records, customer lists, or proprietary information with no audit trail showing they accessed the files. Implement role-based access controls where only relevant staff view specific document categories. Enable audit logging that records which employee accessed a file, when they accessed it, and what actions they performed. Test these controls monthly by attempting unauthorized access to verify they actually work. When you do digitize and destroy originals, demand written certificates of destruction from your shredding provider detailing the date, method, location, and quantity destroyed. Retain these certificates indefinitely for audit purposes, as they prove compliance if regulators investigate your document handling practices.
Final Thoughts
The shift from paper to digital records is no longer optional. Businesses that continue storing sensitive documents in filing cabinets waste money on physical space, expose themselves to compliance violations, and create unnecessary risk when a breach occurs. Professional document scanning and shredding eliminates these vulnerabilities while improving how your team actually works-employees spend less time hunting through boxes for invoices and more time on work that generates revenue.
The real question isn’t whether to digitize and shred, but whether you’ll handle it yourself or hire professionals who specialize in secure document management. DIY approaches create gaps: employees photograph documents with personal smartphones, producing poor-quality scans that OCR software struggles to read; incomplete shredding leaves readable fragments; weak digital storage practices expose files to unauthorized access. Professional services eliminate these problems through standardized workflows, certified destruction methods, and documented compliance proof.
We at Scan N More help businesses transition from paper to digital through high-quality scanning for all document formats, including legal and medical records. Our on-site and off-site scanning options fit your timeline and operational needs, and we handle the complete lifecycle from collection through secure storage. Contact us today to discuss how we can transform your document management and eliminate paper-based vulnerabilities from your operations.
