Data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 report. Most companies lack proper data security controls, leaving critical information exposed to ransomware, insider threats, and vendor vulnerabilities.
We at Scan N More have built this guide to help you understand the three layers of protection you need: administrative policies, technical encryption, and physical access management. You’ll also learn how to identify threats before they become costly problems and implement practices that actually work.
The Three Layers of Data Protection
Organizations typically fail at data security because they treat it as a single problem with a single solution. The reality is that protection requires three distinct, complementary approaches working simultaneously. Administrative controls set the rules and policies that govern how employees handle data-without them, technical and physical measures fall apart because people ignore or circumvent them. Technical controls use encryption, access management, and software tools to enforce those rules automatically, preventing unauthorized access even when people make mistakes. Physical controls restrict who can physically access servers, storage devices, and facilities where data lives.
How Each Layer Stops Different Attacks
Each layer addresses different attack vectors. A ransomware attack might exploit weak administrative policies that allow users to install untrusted software. An insider threat succeeds when physical controls fail to prevent someone from copying data to a USB drive. A vendor vulnerability matters only if technical controls don’t isolate third-party systems from sensitive information. The IBM 2024 Cost of a Data Breach report found that organizations with mature administrative, technical, and physical controls reduced breach costs by 28% compared to those with fragmented approaches. This means strong controls don’t just prevent breaches-they directly impact your bottom line when incidents do occur.
Start With Administrative Controls
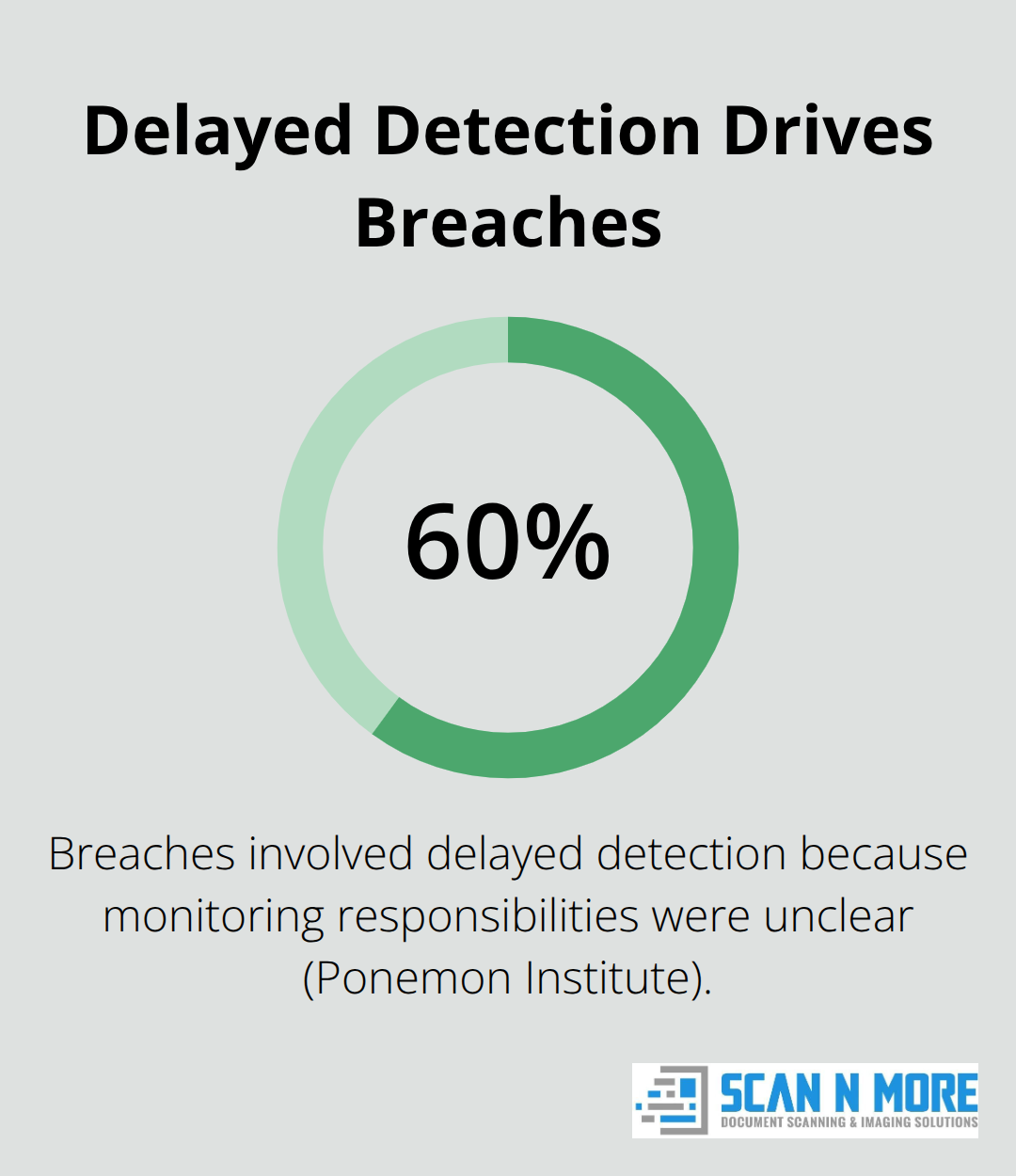
Administrative controls deserve your attention first because they define everything else. Your organization needs written data handling policies that specify who can access what, how data moves between systems, and what happens when someone leaves the company. The Ponemon Institute found that 60% of data breaches involve delayed detection, often because organizations lacked clear policies about who should monitor what.
These policies form the foundation that technical and physical controls build upon.
Layer Technical Controls Second
Technical controls come next-encryption at rest and in transit, multi-factor authentication, and role-based access control prevent most common attacks. These tools enforce your administrative policies automatically across systems and networks. Without technical controls, your policies exist only on paper and rely on human compliance, which fails consistently.
Physical Controls Protect High-Value Data
Physical controls matter most for high-value data: servers containing payment information or health records must sit in locked facilities with limited access. However, physical controls alone mean nothing if your technical systems don’t verify that the person entering the facility actually has authorization to touch that equipment. The strongest organizations integrate all three layers so they reinforce each other rather than operate independently.
Understanding how these three layers work together sets the stage for recognizing the specific threats that exploit weaknesses in each one.
What Threats Target Your Data Controls
Ransomware Attacks Exploit Network Weaknesses
Ransomware operators have shifted tactics dramatically in recent years. They no longer simply encrypt data and demand payment-they now steal information first, then threaten to publish it unless you pay. According to the 2024 Verizon Data Breach Investigations Report, ransomware and extortion breaches have accounted for almost two-thirds of breaches (fluctuating between 59% and 66%) over the past three years. The attack succeeds because organizations fail to separate critical systems from general networks. If your administrative controls don’t mandate network segmentation, and your technical controls don’t enforce it, attackers who breach one system spread laterally to everything else.
Three specific actions stop most ransomware attacks. Implement immutable backups stored offline so you can recover without paying attackers. Enforce multi-factor authentication on all administrative accounts since most ransomware gains entry through compromised credentials.
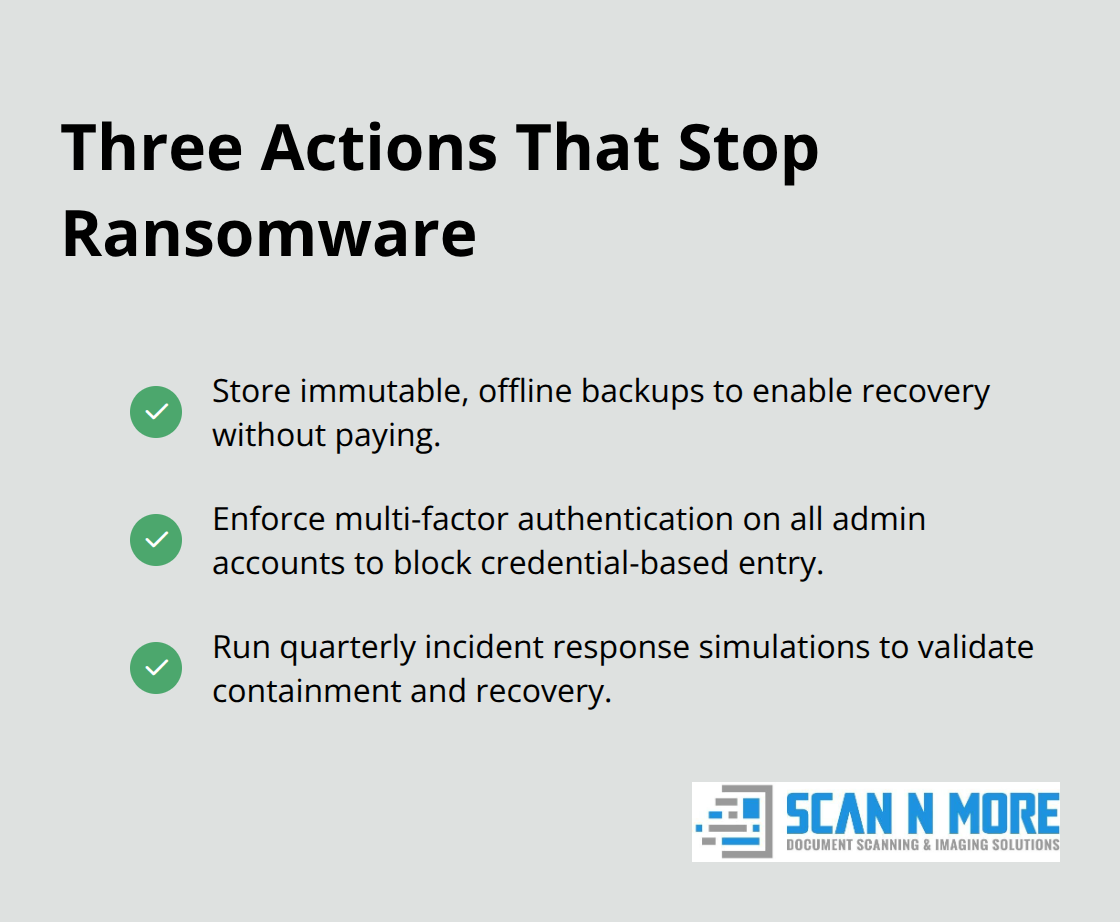
Test your incident response plan quarterly by simulating an actual attack. Organizations that run tabletop exercises to practice ransomware response reduce recovery time by 40% compared to those without formal drills.
Insider Threats Exploit Trust and Access
Insider threats represent a different problem because they exploit trust. Insider incidents cost organizations significant financial impact, making them a critical concern for security teams. These threats come from current employees who access data as part of their job, making them invisible to perimeter defenses.
Your administrative controls must enforce the principle of least privilege rigorously: employees access only the specific data required for their role, and access expires automatically when job responsibilities change. Technical controls should monitor data movement constantly through Data Loss Prevention tools that flag when someone copies large files to personal devices or emails sensitive information outside the organization. However, the most effective defense combines monitoring with accountability-when employees know that their data access is logged and reviewed, behavior changes. Organizations that implemented continuous access reviews and removed unnecessary permissions reduced insider incidents by 35% within six months.
Vendor Vulnerabilities Create Hidden Exposure
Third-party vendors present yet another vector because they often receive access to your systems but operate under different security standards. The 2023 Verizon report found that 17% of breaches involved a business partner or vendor.

Your administrative controls should require vendors to provide proof of their own security certifications before granting access. Technical controls should isolate vendor systems from your most sensitive data using network segmentation and API gateways that limit what information vendors can retrieve.
Conduct annual security assessments of critical vendors and require them to report any breaches within 72 hours. Organizations that actively managed vendor risk and enforced contractual security requirements experienced 50% fewer vendor-related breaches than those with passive vendor relationships. These three threat categories-ransomware, insider activity, and vendor exposure-demand different defensive strategies, each rooted in how well your administrative, technical, and physical controls work together.
How to Make Data Security Controls Actually Work
Conduct Continuous Assessments Instead of Annual Reviews
Auditing your controls once a year and hoping for the best is how breaches happen. Most organizations conduct security assessments so infrequently and superficially that attackers operate inside their networks for months undetected. Most security experts recommend a full-scale security audit every three years, with annual reviews of risk factors. You need a schedule that matches your threat environment, not your budget cycle.
Start with a security audit that identifies your current state, then move to quarterly vulnerability scans of your critical systems, monthly reviews of who has access to sensitive data, and weekly logs of administrative activities. These assessments should focus on the gaps between what your controls are supposed to do and what they actually do. When you discover that your multi-factor authentication policy exists on paper but half your users have it disabled, that’s the actionable finding that matters.
Assign specific people ownership of each control area so assessments actually lead to fixes rather than disappearing into a folder. Most importantly, adjust your controls immediately when assessment results reveal problems rather than waiting for the next scheduled review cycle.
Test Your Incident Response Plan With Realistic Scenarios
Your incident response plan must be tested with realistic scenarios before you face an actual attack, and tabletop exercises prove far more valuable than theoretical documents. Run quarterly simulations where your team practices detecting, containing, and recovering from a ransomware attack or data exfiltration as if it were happening in real time.
These exercises reveal which contacts are outdated, which procedures take twice as long as documented, and which team members lack the skills they need. Organizations conducting quarterly incident response drills reduced their average breach detection time from 207 days to 47 days. Your plan should specify exactly who gets called first, what communication channels you use, how you preserve evidence, and when you notify customers or regulators.
Build Security Into How Work Actually Happens
Make security part of how work actually happens rather than treating it as abstract policy. When employees see their manager asking security questions before approving new tools, when they watch data access reviews happen monthly instead of annually, when they know that violations result in actual consequences rather than warnings, behavior shifts.
Organizations that tied security performance to performance reviews and compensation saw 40% fewer security violations within a year. Make security visible and consequential-not optional or theoretical-and your team will treat it as a priority that matters to their career and the organization’s success.
Final Thoughts
Data security controls work only when all three layers operate together. Administrative policies define what protection looks like, technical tools enforce those policies automatically, and physical measures prevent direct access to sensitive systems. Organizations that integrate these layers reduce breach costs by 28% and detect incidents far faster than those treating security as separate functions.
The threats are real and evolving-ransomware operators now steal data before encrypting it, insider threats exploit legitimate access, and vendor vulnerabilities create hidden exposure. Your defenses must address each threat type with specific, tested strategies (immutable backups stop ransomware extortion, continuous access reviews catch insider activity, and vendor security assessments prevent third-party breaches). Implementation requires commitment beyond documentation: quarterly vulnerability scans, monthly access reviews, and realistic incident response drills transform security from theory into practice.
We at Scan N More understand that data security extends beyond digital controls. When you transition from paper-based processes to digital solutions, our professional document scanning services include on-site and off-site scanning for all formats, hard drive destruction, and mail scanning with data security guarantees. Digitizing your documents securely removes a major physical security vulnerability while improving operational efficiency.
