Data breaches cost companies an average of $4.45 million per incident, according to IBM’s 2024 report. The threats are real, they’re growing, and they’re targeting businesses of all sizes.
At Scan N More, we’ve seen firsthand how data security threats evolve faster than most organizations can respond. This guide walks you through the threats you’re facing, how leading companies are fighting back, and the concrete steps you need to take right now.
The Three Threats Destroying Your Data Right Now
Ransomware: The Backup-Hunting Weapon
Ransomware has become a financial weapon. In 2025, cryptocurrency heist reached $1.46 billion. Attackers now specifically target your backups-they encrypt your primary data, then hunt down and destroy your recovery copies to force payment. The average eCrime breakout time has accelerated to just 29 minutes, meaning attackers move from initial access to full encryption in less time than it takes to run a meeting.
If you’re relying on backups without testing whether they’re actually recoverable and isolated from your main network, you’re gambling with your business. Your backup strategy needs immutability built in, regular restoration tests, and physical separation from your production environment. Test your recovery process quarterly-not annually. Attackers exploit untested backups because they know most organizations never validate them until disaster strikes.
Phishing and Social Engineering: The Credential Theft Pipeline
Phishing and social engineering remain the fastest path into your systems because they exploit the one variable you can’t fully control: people. The CrowdStrike report shows that 82% of detections in 2025 were malware-free attacks, meaning attackers logged in using stolen credentials rather than forcing their way through firewalls. ChatGPT-related activity in criminal forums surged 550% compared to other AI models, enabling attackers to craft highly personalized, context-aware messages that feel legitimate.
Business Email Compromise attacks succeed because they target decision-makers with urgent requests that bypass normal verification. Your employees need real training that goes beyond generic awareness videos. They need to understand why verification matters, how to spot subtle inconsistencies in sender addresses, and what to do when something feels off. Teach them to pause before clicking links or downloading attachments, especially when requests come from unfamiliar senders or ask for unusual actions.
Insider Threats and Human Error: The Permission Problem
Insider threats and human error round out this triad-and they aren’t always malicious. Misconfigured cloud permissions, accidentally shared credentials, or an employee downloading files to an unsecured personal device create vulnerabilities that attackers exploit. The Verizon Data Breach Investigations Report confirms that human error drives a large share of cyber incidents.
Your approach here is straightforward: implement Zero Trust architecture that continuously verifies access attempts, conduct regular permission audits to eliminate over-privileged accounts, and use Identity and Access Management systems with multi-factor authentication enforced across the board. Audit permissions quarterly, not annually. Remove access the moment employees change roles. Enforce MFA on every system that holds sensitive data-no exceptions, no workarounds.
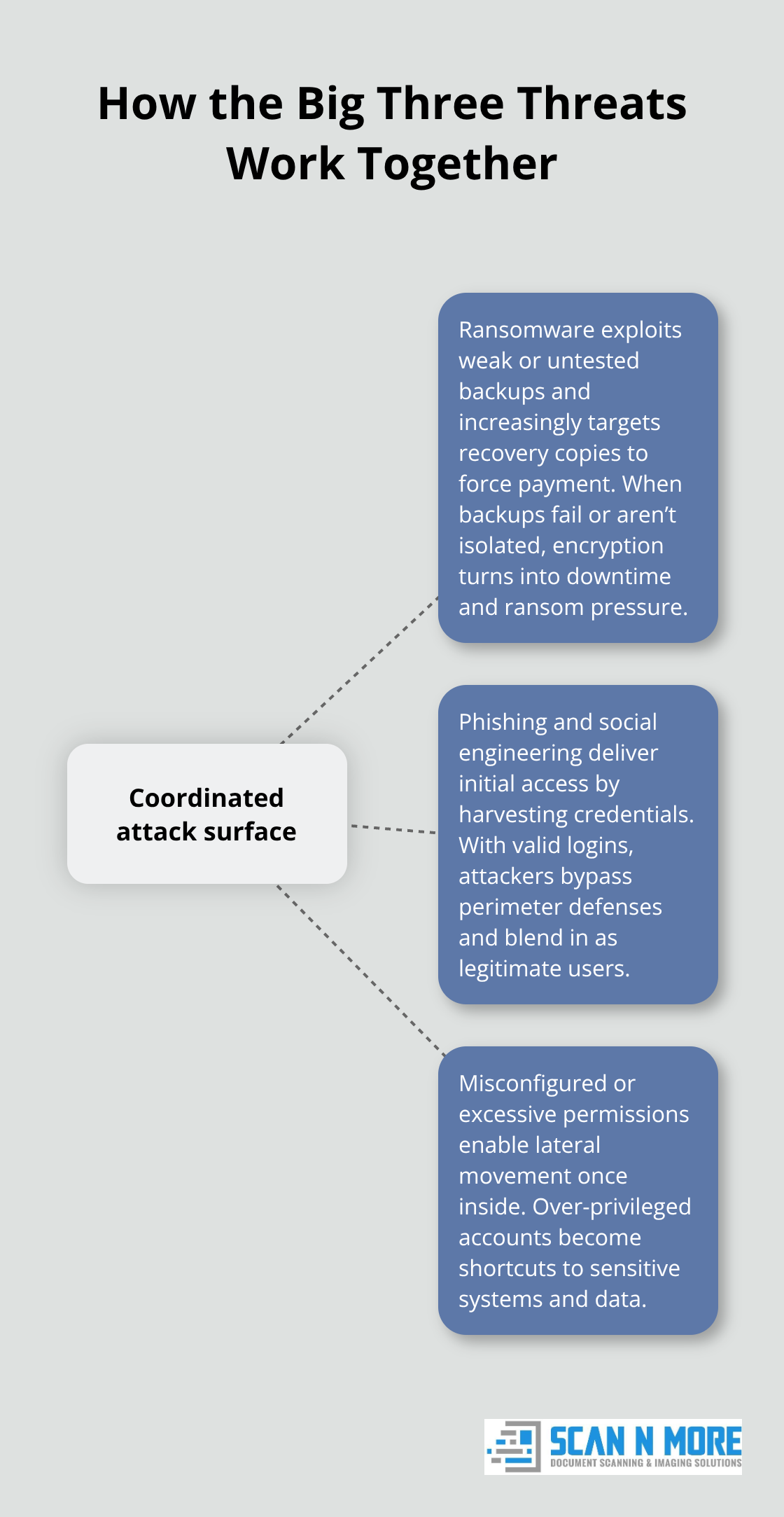
These three threats form a coordinated attack surface. Ransomware exploits weak backups, phishing delivers the initial credentials, and misconfigured permissions let attackers move laterally once inside. Understanding how businesses respond to these interconnected risks reveals where your defenses need the most attention.
How Leading Organizations Are Defending Their Data
Zero Trust and Continuous Verification
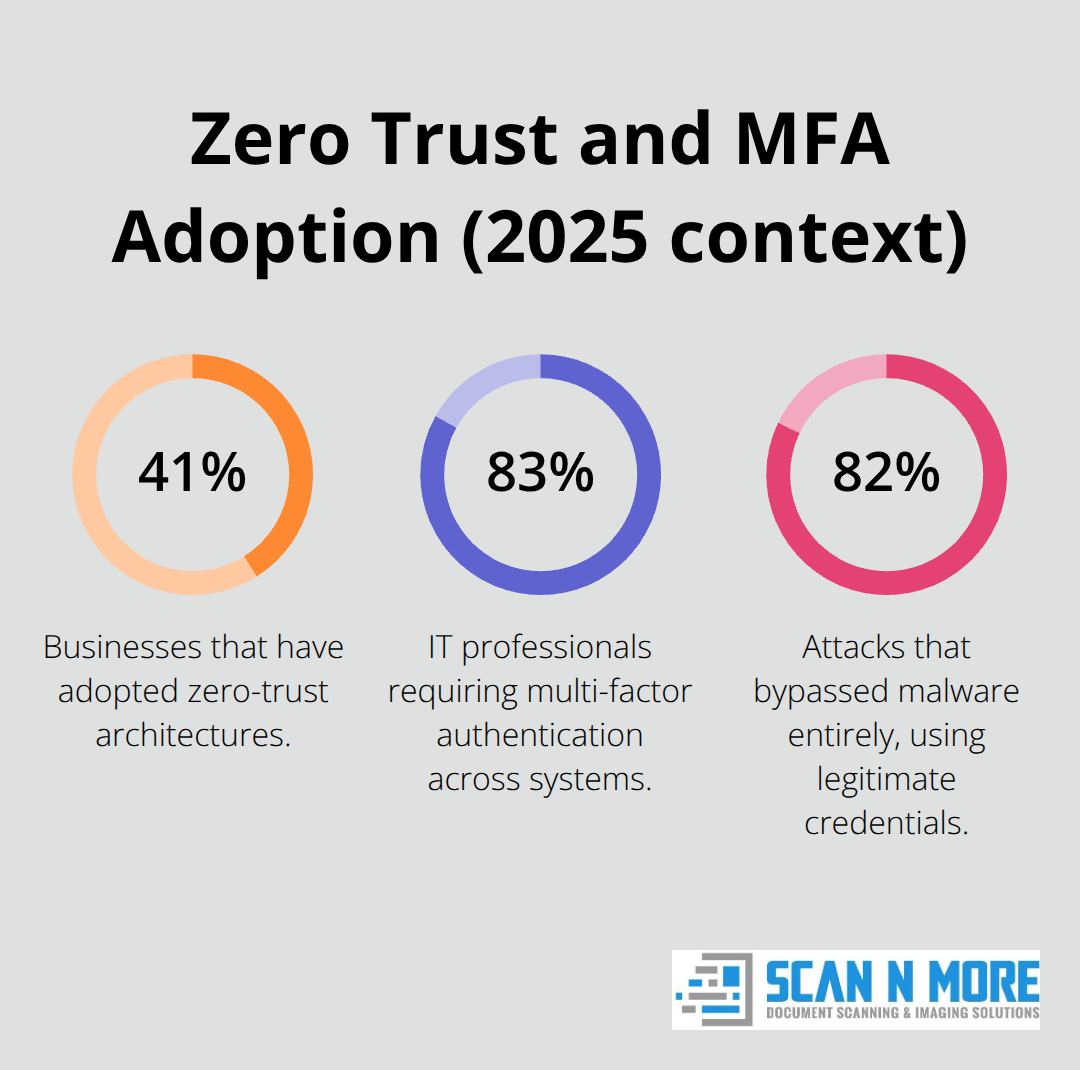
Organizations fighting back against these threats reject single-layer defenses and stack controls that make lateral movement and data exfiltration progressively harder. Zero Trust architecture sits at the core of this strategy, requiring continuous verification across every user, device, and workload rather than trusting anything inside the perimeter. Capgemini’s research shows that 41% of businesses have already adopted zero-trust architectures, and 83% of IT professionals now require multi-factor authentication across systems. This shift matters because 82% of 2025 attacks bypassed malware entirely-attackers logged in using legitimate credentials. Without MFA and continuous verification, stolen credentials become master keys to your entire infrastructure.
The fastest organizations audit permissions quarterly, removing access the moment an employee changes roles or leaves the company. They use Identity and Access Management systems that enforce least-privilege access, ensuring no one holds more permissions than their role requires. This directly counters insider threats and human error because over-privileged accounts become targets and liabilities.
Backup Isolation and Restoration Testing
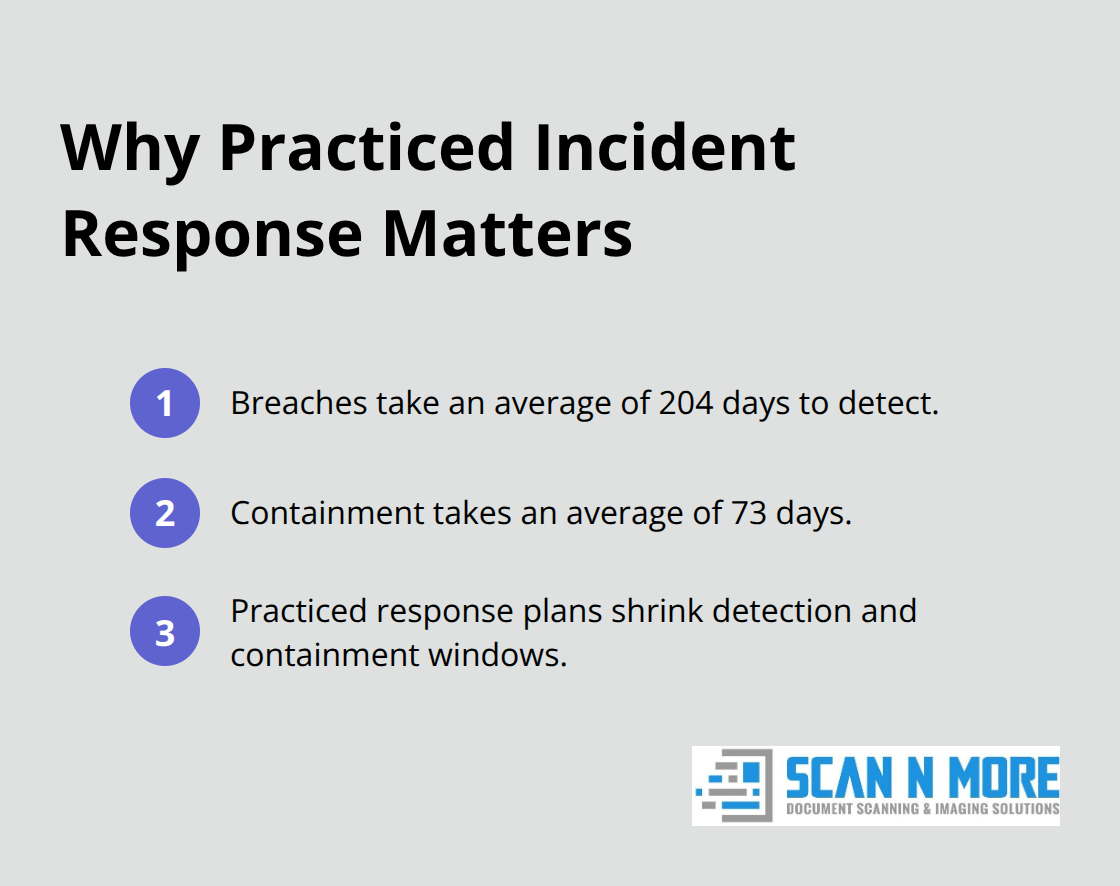
Leading organizations treat incident response as a living process, not a document gathering dust on a server. They establish cross-functional response teams before incidents occur, assign clear ownership to IT, legal, communications, and HR, and run tabletop exercises at least twice annually to test their actual response speed. The Verizon Data Breach Investigations Report shows that breaches take an average of 204 days to detect and 73 days to contain, but organizations with practiced response plans shrink that window significantly.
Ransomware-specific readiness requires maintaining isolated, immutable backups that live completely separate from production networks. Organizations test restoration capabilities quarterly rather than annually and document exactly which systems they can recover in what order. This preparation prevents attackers from destroying backup copies and forcing payment through encryption.
Cloud Security and Configuration Management
Cloud security adds another layer of complexity because 61% of organizations report at least one cloud attack per year. Leading organizations deploy dedicated controls like Cloud Security Posture Management tools that continuously scan for misconfigurations, excessive permissions, and unencrypted data. These tools identify drift before attackers exploit it, catching the gaps that human oversight misses.
Employee training moves beyond generic awareness videos toward practical, threat-aware instruction that teaches teams to recognize subtle phishing indicators, understand why verification matters, and know exactly what to do when something feels wrong. Organizations that treat security as a shared responsibility across departments, invest in real-time threat monitoring and automated response capabilities, and treat security audits as continuous rather than annual checkpoints build resilience that actually holds.
The most effective organizations combine these defenses with a clear understanding of which data matters most and where it lives. This foundation-knowing your data landscape-determines whether your controls protect what actually needs protection or leave critical assets exposed.
How to Lock Down Access, Encrypt Everything, and Respond When Attacks Happen
Control Who Accesses Your Sensitive Data
Access control failures destroy more organizations than flashy zero-day exploits ever will. The moment you grant someone permission they don’t need, you’ve created a liability. Start by mapping every system that holds sensitive data and documenting exactly who accesses it. Then audit those permissions ruthlessly.
Remove access the instant someone changes roles or leaves your company. Enforce MFA on every system holding sensitive data without exceptions.
Conduct quarterly permission reviews, not annual ones, because drifting permissions are how attackers move laterally through networks. Use Identity and Access Management systems configured for least-privilege access, meaning employees receive only the permissions their specific role requires. If someone in marketing doesn’t need access to customer payment data, they shouldn’t have it. Period.
Implement Least-Privilege Access Across Your Organization
Restricted permissions directly counter both insider threats and human error because limited access constrains the damage any single compromised account can inflict. Over-privileged accounts create unnecessary risk; attackers exploit them because they provide wider lateral movement and faster access to sensitive systems.
Start with your highest-risk roles: database administrators, system engineers, and anyone with access to customer data or financial records. These positions need the tightest controls and the most frequent audits. Review their permissions monthly rather than quarterly. Remove standing administrative access and replace it with just-in-time elevation that requires approval and logging for each use.
This approach (sometimes called zero standing privilege) forces attackers to compromise multiple accounts or exploit additional vulnerabilities to move through your network. A single stolen credential becomes far less valuable when that account holds minimal permissions.
Encrypt data in transit and at rest
Encryption and incident response separate organizations that survive attacks from those that don’t. Encrypt data in transit using TLS across all connections and encrypt data at rest on servers, databases, and cloud storage using AES-256 or equivalent standards. This meets compliance requirements and prevents attackers from reading stolen data even when they breach your systems.
Encryption doesn’t stop attackers from stealing files, but it renders those files unreadable without the decryption keys. This distinction matters because ransomware operators often exfiltrate data before encrypting it, threatening to sell or publish sensitive information if you refuse payment. Encryption eliminates that secondary extortion vector.
Test your encryption implementation quarterly. Verify that all databases use encryption, that cloud storage buckets have encryption enabled, and that TLS certificates remain valid and properly configured. Many organizations encrypt data but misconfigure the process, leaving gaps that attackers exploit.
Establish and Test Your Incident Response Plan
Establish a cross-functional incident response team before you need it, assigning clear ownership to IT, legal, communications, and HR. Run tabletop exercises at least twice yearly to test your actual response speed. Organizations with practiced response plans can significantly reduce detection and containment times.
Maintain isolated, immutable backups completely separate from production networks and test restoration capabilities quarterly. Document exactly which systems you can recover and in what order. This preparation prevents attackers from destroying backup copies and forces them to abandon encryption attacks when recovery proves possible without payment.
Most organizations fail at incident response not because they lack plans but because they never test them until disaster strikes. Your response plan is worthless if you discover during an actual breach that your backups are corrupted or your recovery procedures don’t work. Test them now, quarterly, under realistic conditions with real data and real timelines.
Validate Recovery Before You Need It
The difference between a contained breach and a catastrophic one often comes down to whether your backups actually work. Organizations that recover quickly from ransomware attacks share one trait: they validated their recovery process before attackers encrypted their systems.
Schedule quarterly restoration tests where you select random systems, attempt full recovery from backup, and verify that recovered data matches the original. Document the time required for each recovery and identify bottlenecks. If recovery takes longer than your business can tolerate downtime, your backup strategy needs redesign (perhaps through faster storage, better network bandwidth, or more frequent incremental backups).
Test your incident response procedures under pressure. Simulate a breach scenario with your response team, measure how quickly you detect the simulated attack, and track how long containment takes. These exercises reveal gaps in communication, unclear ownership, and missing tools that only surface when you practice under realistic conditions.
Final Thoughts
The data security threats outlined in this guide aren’t theoretical risks. Ransomware operators actively target backups right now, attackers log into systems using stolen credentials from phishing campaigns, and misconfigured permissions sit in your cloud environment waiting for exploitation. These threats hit businesses across every industry and size, and they evolve faster than most organizations can respond.
The organizations that survive attacks treat security as a continuous process rather than a checkbox exercise. They audit permissions quarterly instead of annually, test backups before disaster strikes, run incident response drills under realistic conditions, and enforce multi-factor authentication across every system holding sensitive data. These practices cost far less than recovering from a breach, yet most organizations skip them entirely.
Start with three high-impact actions: audit your permissions and remove access people no longer need, test your backup restoration process this quarter, and enforce MFA on systems holding sensitive data. Scan N More provides professional document scanning services with built-in data security and compliance, protecting your digitized documents from the moment they’re scanned and eliminating vulnerabilities that emerge when organizations mishandle the shift to digital environments.
