Organizations running workloads across multiple cloud platforms face a fragmented security landscape. Data stored in AWS, Azure, Google Cloud, and other providers creates blind spots that attackers exploit.
At Scan N More, we’ve seen firsthand how multi-cloud data security failures expose sensitive information and violate compliance requirements. This guide walks you through proven strategies to protect your distributed infrastructure.
Why Organizations Struggle With Multi-Cloud Security
Eighty-six percent of organizations now operate across multiple cloud providers. They split workloads between AWS, Azure, Google Cloud, and others for flexibility, cost optimization, and vendor independence. The reality proves harsher: this distribution creates security gaps that traditional point solutions cannot manage. Each cloud provider enforces different encryption standards, access control models, and compliance frameworks. Your data in AWS follows different protection rules than data in Azure, and your security team likely lacks visibility into all of it simultaneously.
The Real Cost of Fragmented Infrastructure
The numbers reveal why this matters. Forty-five percent of all data breaches occur in cloud environments, and eighty percent of organizations experienced at least one cloud breach in the past year. The average cost of a cloud data breach reaches 4.44 million dollars globally, with US organizations facing nearly 10.22 million dollars per incident.
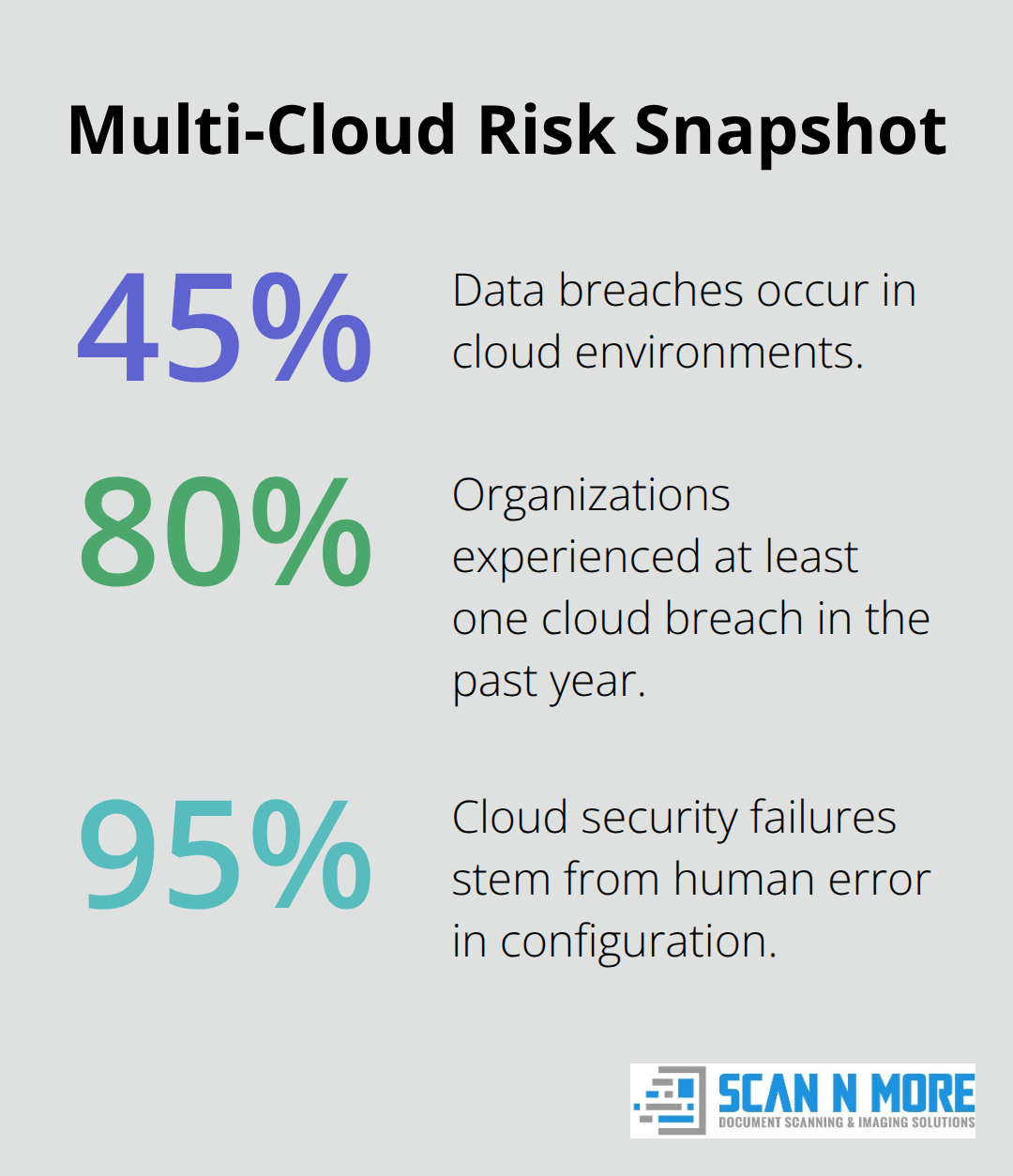
These aren’t theoretical risks. When your infrastructure spans multiple clouds, misconfigurations become exponentially more dangerous. Ninety-five percent of cloud security failures stem from human error in configuration, not sophisticated attacks. A single misconfigured S3 bucket in AWS or an overly permissive IAM role in Azure exposes millions of records. The problem intensifies because your security team must manage different configuration standards across providers, each with its own terminology and control mechanisms.
Identity and Access Management Across Boundaries
Seventy percent of cloud breaches originate from compromised identities. This statistic alone should drive your multi-cloud strategy. When identities aren’t synchronized across cloud platforms, attackers exploit the gaps. An employee with access to production data in one cloud might retain dormant credentials in another. Seventy-seven percent of organizations identify identity and access management as their top cloud-native risk. The challenge intensifies because cloud providers handle identity federation differently (AWS uses IAM roles, Azure uses managed identities, and Google Cloud uses service accounts). Without a unified approach to multi-factor authentication and single sign-on across all platforms, you run separate identity systems that don’t communicate. This fragmentation creates opportunities for lateral movement and credential reuse that attackers actively hunt.
Why Unified Access Control Matters
Organizations that fail to synchronize access controls across clouds face exponential risk. An attacker who compromises credentials in one environment gains leverage to attack others. Your team cannot manually track which users hold active access across AWS, Azure, and GCP simultaneously. Dormant accounts accumulate in forgotten cloud environments, and permissions granted months ago persist without review. Implementing single sign-on and multi-factor authentication across all platforms eliminates these blind spots. Least-privilege access principles-granting only the minimum permissions necessary-reduce the blast radius when a breach occurs. Regular access reviews and pruning of dormant accounts prevent credentials from becoming weapons in attackers’ hands.
The Path Forward Requires Unified Visibility
Multi-cloud security demands more than patching individual cloud environments. Your organization needs centralized visibility into every identity, every permission, and every data access event across all platforms. This unified view enables your team to detect anomalies, enforce consistent policies, and respond to threats before they spread. The next section explores the essential security strategies that transform fragmented infrastructure into a cohesive, defensible environment.
How to Protect Data Consistently Across Multiple Clouds
Encryption across multiple cloud providers fails when organizations treat each platform independently. AWS KMS, Azure Key Vault, and Google Cloud KMS operate as separate systems with different key rotation schedules, access policies, and audit trails. This fragmentation means your encryption strength depends on your weakest cloud environment. Fifty-five percent of organizations use cloud encryption tools to manage and rotate private keys, but only 21 percent have encrypted over 60 percent of their classified cloud data. The gap reveals the real problem: encryption deployment remains inconsistent and incomplete.
Centralized Key Management Controls All Platforms
You need a centralized key management approach that controls encryption across all platforms simultaneously. Implement a bring-your-own-key (BYOK) strategy where your organization retains the master encryption key outside any single cloud provider. This approach gives you immediate revocation capability if a breach occurs and prevents cloud providers from accessing your encrypted data. When your master key stays off-cloud, a compromised AWS account or Azure subscription does not expose your encryption keys.
Rotate keys across all clouds on a defined schedule (quarterly or more frequently for sensitive data) using automated processes. Manual rotation across three or more cloud environments introduces human error and creates windows where old keys remain active. Test key revocation procedures annually to confirm you can rapidly re-encrypt data and deny access if attackers obtain credentials. Organizations that maintain keys in a centralized, off-cloud key management system reduce breach impact significantly compared to those relying on cloud-provider-managed keys.
Identity Synchronization Prevents Lateral Attacks
Compromised identities account for 70 percent of cloud breaches according to SentinelOne research. Single sign-on (SSO) and multi-factor authentication (MFA) must span AWS, Azure, Google Cloud, and any other platforms your organization uses. Implement identity federation using standards like SAML or OAuth 2.0 so that a single credential set controls access across all clouds. When an employee leaves your organization, deprovisioning from one system automatically revokes access everywhere.
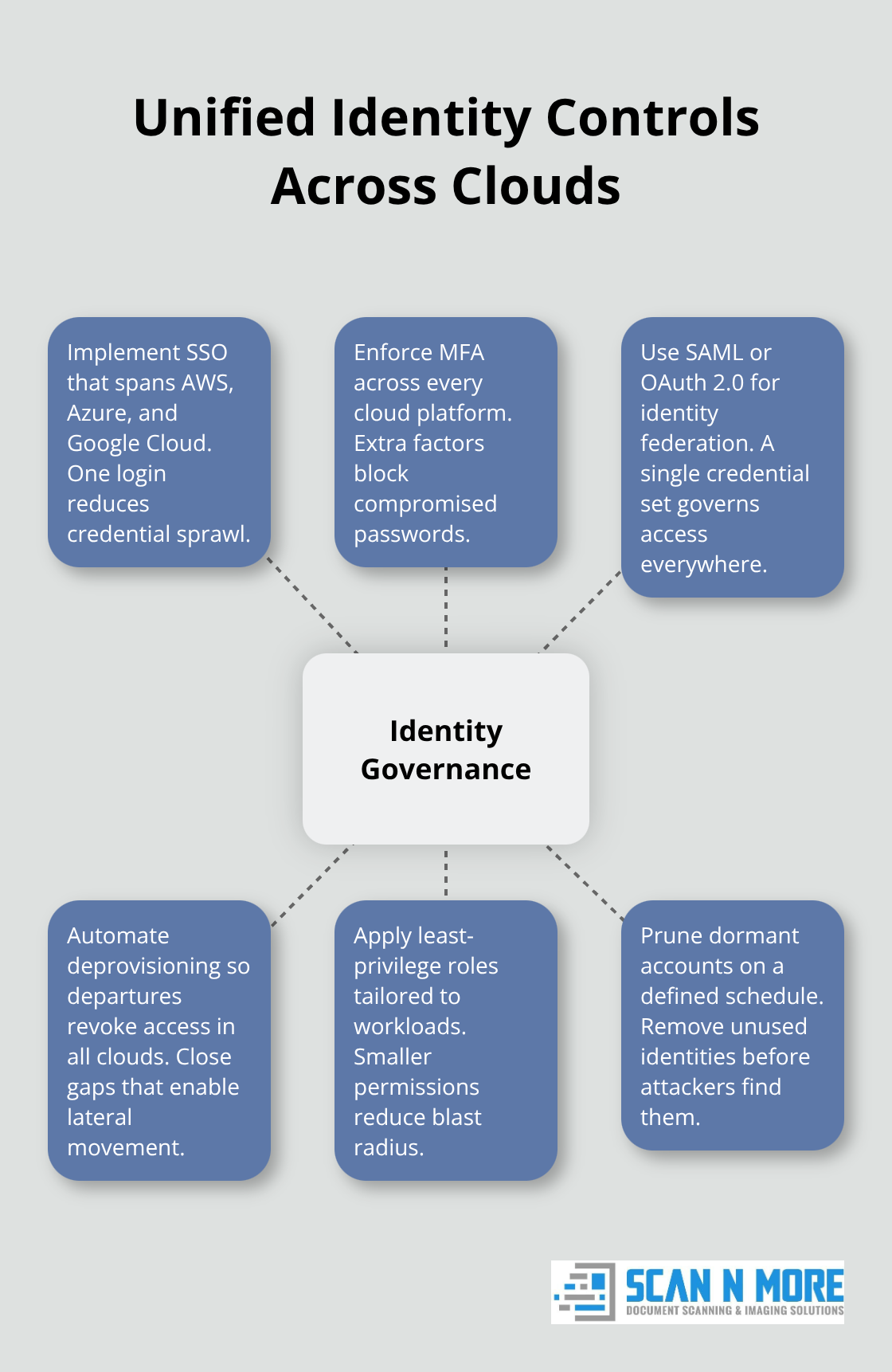
Dormant accounts that accumulate in forgotten cloud environments become attack vectors. Establish a quarterly access review process that identifies and removes unused identities across all platforms. Apply least-privilege access by granting roles that permit only necessary actions for specific workloads. An application server in AWS needs read access to specific S3 buckets, not full administrative permissions. Service accounts that authenticate applications to cloud services should rotate credentials every 90 days and use temporary tokens instead of long-lived keys. Organizations that enforce MFA lose 99.9 percent fewer accounts to compromise than those relying on passwords alone.
Real-Time Threat Detection Across All Platforms
Visibility gaps plague multi-cloud environments. Sixty-nine percent of organizations report tool sprawl and visibility gaps due to non-integrated monitoring across cloud providers. Your security team cannot protect what it cannot see. Deploy a unified security information and event management (SIEM) system that aggregates logs from AWS CloudTrail, Azure Activity Log, and Google Cloud Audit Logs into a single dashboard. Configure continuous compliance scoring that automatically checks configurations against CIS benchmarks and industry standards across all clouds simultaneously.
Automated misconfiguration detection catches overly permissive security groups, publicly accessible storage buckets, and unencrypted databases before attackers find them. Alert on suspicious patterns such as unusual data access volumes, failed login attempts from unexpected locations, or privilege escalation within service accounts. Integrate threat intelligence feeds that identify known malicious IP addresses and domains attempting to reach your cloud infrastructure. Organizations that maintain real-time visibility detect breaches in days rather than months; the average dwell time for undetected breaches exceeds 200 days, giving attackers extensive time to extract data and move laterally.
Automation Reduces Human Error Across Environments
The next critical step involves automating security controls across your multi-cloud infrastructure. Manual processes fail at scale, especially when your team manages three or more cloud platforms simultaneously.
Selecting Tools That Unify Multi-Cloud Protection
Cloud Security Posture Management platforms form the foundation of any defensible multi-cloud strategy, yet most organizations deploy them reactively rather than strategically. CSPM tools continuously scan your AWS, Azure, and Google Cloud environments to detect misconfigurations, unencrypted data, and excessive access permissions before attackers exploit them. The problem with many CSPM implementations stems from tool sprawl: organizations purchase separate solutions for each cloud platform, creating fragmented reporting and inconsistent remediation workflows. Gartner’s Market Guide for Cloud-Native Application Protection Platforms emphasizes that unified platforms reduce integration complexity and accelerate time-to-value. Your security team should prioritize CSPM solutions that scan all three major cloud providers from a single console, apply consistent policy frameworks like CIS benchmarks across platforms simultaneously, and automate remediation for low-risk misconfigurations such as public-facing storage buckets.
Real-Time Protection Across All Clouds
SentinelOne’s CWPP offering demonstrates unified protection by providing real-time defense across AWS, Azure, and GCP with continuous compliance scoring and automated misconfiguration checks. The critical differentiator lies in coverage: platforms that detect over 750 types of hardcoded secrets before production deployment prevent developers from embedding credentials in application code, a mistake that accounts for significant breach vectors. Configure your CSPM to alert immediately on critical issues (unencrypted databases, overly permissive IAM roles, disabled logging) while batching lower-priority findings into weekly reports to prevent alert fatigue.
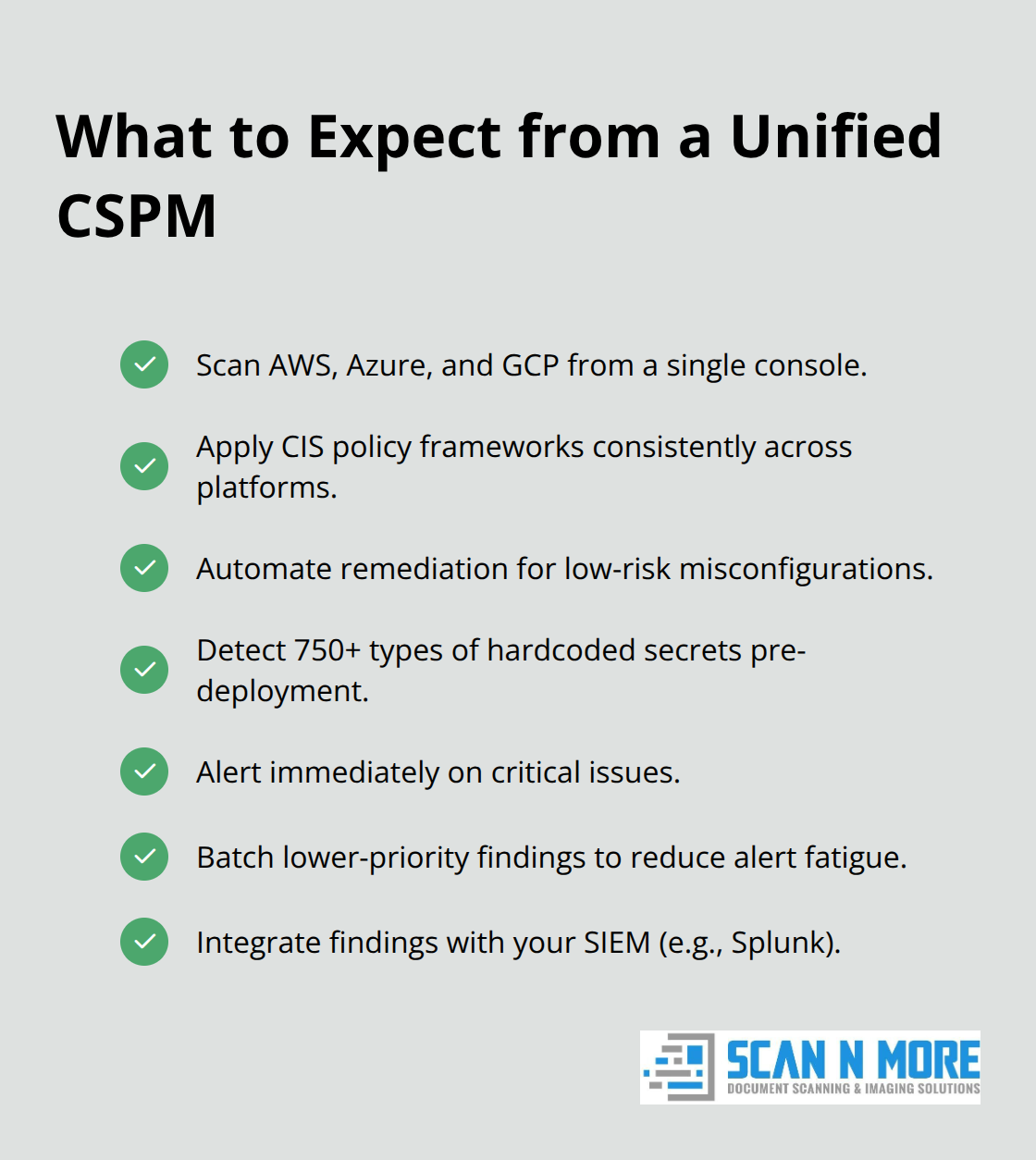
Integration with your existing SIEM system matters enormously; tools that feed compliance data and misconfiguration findings into Splunk or similar platforms enable your security operations center to correlate cloud events with network activity and endpoint telemetry.
Data Loss Prevention Across Multi-Cloud Architectures
Data Loss Prevention requires architectural thinking rather than tool selection alone. Organizations that implement DLP across multiple clouds often fail because they treat each platform’s data flows independently rather than monitoring data movement between clouds and external destinations. Backup solutions must protect not just against accidental deletion but against ransomware targeting cloud backups specifically; 78 percent of companies experienced ransomware impact in the past year, with attackers increasingly targeting backup infrastructure as their primary objective. Deploy immutable backup copies stored in a separate cloud account or region that restricts deletion permissions to prevent attackers from destroying recovery options.
Incident Response Planning Across Platforms
Your incident response plan should include predefined procedures for breach containment across multiple clouds: immediate isolation of affected resources, credential rotation across all platforms simultaneously, and forensic capture of logs from CloudTrail, Activity Log, and Audit Logs before attackers delete them. Organizations that maintain documented runbooks for common scenarios (compromised service account, unauthorized data access, misconfigured security group) respond to incidents in hours rather than days, significantly reducing breach impact and regulatory exposure. Test your incident response procedures annually through simulated breach scenarios across your multi-cloud infrastructure; this reveals gaps in communication between teams, missing access to log data, and tooling limitations before a real incident occurs.
Final Thoughts
Multi-cloud data security demands consistent execution across every platform your organization uses. The strategies in this guide address the core vulnerabilities that plague distributed infrastructure: fragmented encryption, inconsistent access controls, visibility gaps, and reactive incident response. Organizations that implement centralized key management, unified identity governance, and real-time threat detection across AWS, Azure, and Google Cloud transform their security posture from reactive to proactive.
Your immediate priorities should focus on three critical areas. First, audit your current encryption approach across all cloud platforms and implement a bring-your-own-key strategy that keeps master keys outside any single provider. Second, deploy single sign-on and multi-factor authentication across every cloud environment to eliminate identity fragmentation and reduce breach risk by 99.9 percent. Third, establish a unified SIEM system that aggregates logs from all platforms into one dashboard, enabling your team to detect anomalies and respond to threats before they spread.
The statistics prove unambiguous: 45 percent of data breaches occur in cloud environments, and the average breach costs 4.44 million dollars globally. These incidents stem primarily from misconfigurations and compromised identities, both preventable through the strategies covered in this guide. At Scan N More, we help organizations strengthen their overall security posture by transforming paper-based vulnerabilities through professional document scanning services that ensure data security and compliance.

