Data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2023 report. Yet many companies still treat data warehouse security as an afterthought.
At Scan N More, we’ve seen firsthand how weak security practices expose sensitive information to unauthorized access, insider threats, and ransomware attacks. The good news is that protecting your data warehouse doesn’t require expensive overhauls-it requires the right strategy and tools.
The Real Threats Lurking in Your Data Warehouse
Unauthorized Access: The Most Common Entry Point
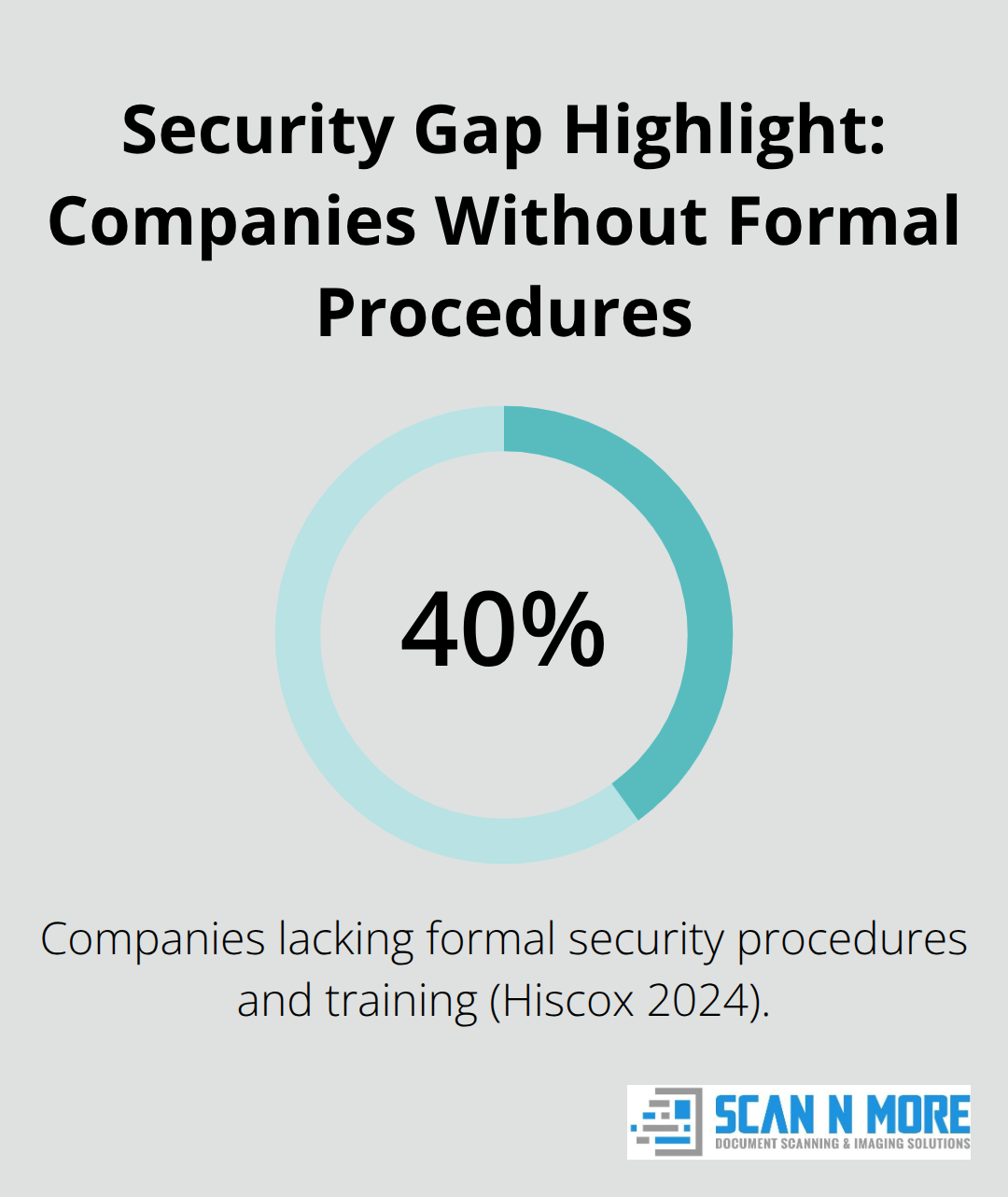
Unauthorized access remains the most common entry point for data warehouse breaches, and it happens in ways most organizations don’t anticipate. External attackers exploit weak credentials and misconfigured permissions, but the Hiscox 2024 cybersecurity study of over 4,000 companies revealed something more troubling: 40% lack formal security procedures and training. This gap means attackers often find their way in through compromised employee accounts rather than sophisticated hacking techniques. Misconfiguration stands as the leading cause of data warehouse breaches, with default settings and overly broad permissions creating massive exposure.
Real-world scenarios illustrate how easily this happens. A department manager changes a URL parameter to access confidential reports that weren’t theirs. Attackers manipulate directory paths to retrieve account summaries through a compromised web application. These aren’t hypothetical scenarios-they occur regularly because organizations fail to implement the principle of least privilege, where employees receive only the minimum permissions needed for their role. Insider threats pose an equally serious risk as external attacks.
The Insider Threat Problem
Your own staff can alter data, export sensitive information, or manipulate queries to access restricted records. The problem intensifies when access controls rely solely on authentication without monitoring what employees actually do once they’re inside the system. Organizations that grant broad permissions without oversight create conditions where insiders exploit their legitimate access to steal or compromise data. This risk demands more than just strong passwords-it requires continuous monitoring and activity logging that tracks who accesses what and when.
Malware and Ransomware: High-Value Targets
Malware and ransomware attacks specifically targeting data warehouses have accelerated as attackers recognize the concentration of valuable information. Ransomware operators know that data warehouses hold centralized data from multiple sources, making them high-value targets that organizations will pay substantial sums to recover. These attacks typically exploit unpatched vulnerabilities in front-end applications or weak input validation-attackers inject SQL code into applications to gain control of the database, or they exploit default DBMS configurations that still have unnecessary features enabled.
The attack surface expands dramatically when organizations add web-enabled applications, cloud services, and wireless access without hardening those connection points. Temporary files and unencrypted caches left on disk create additional vulnerability windows. Organizations that haven’t removed sample code, debug functionality, and nonessential admin features from their systems essentially leave doors open for attackers. If your warehouse stores unencrypted data, a successful breach means immediate exposure of sensitive information.
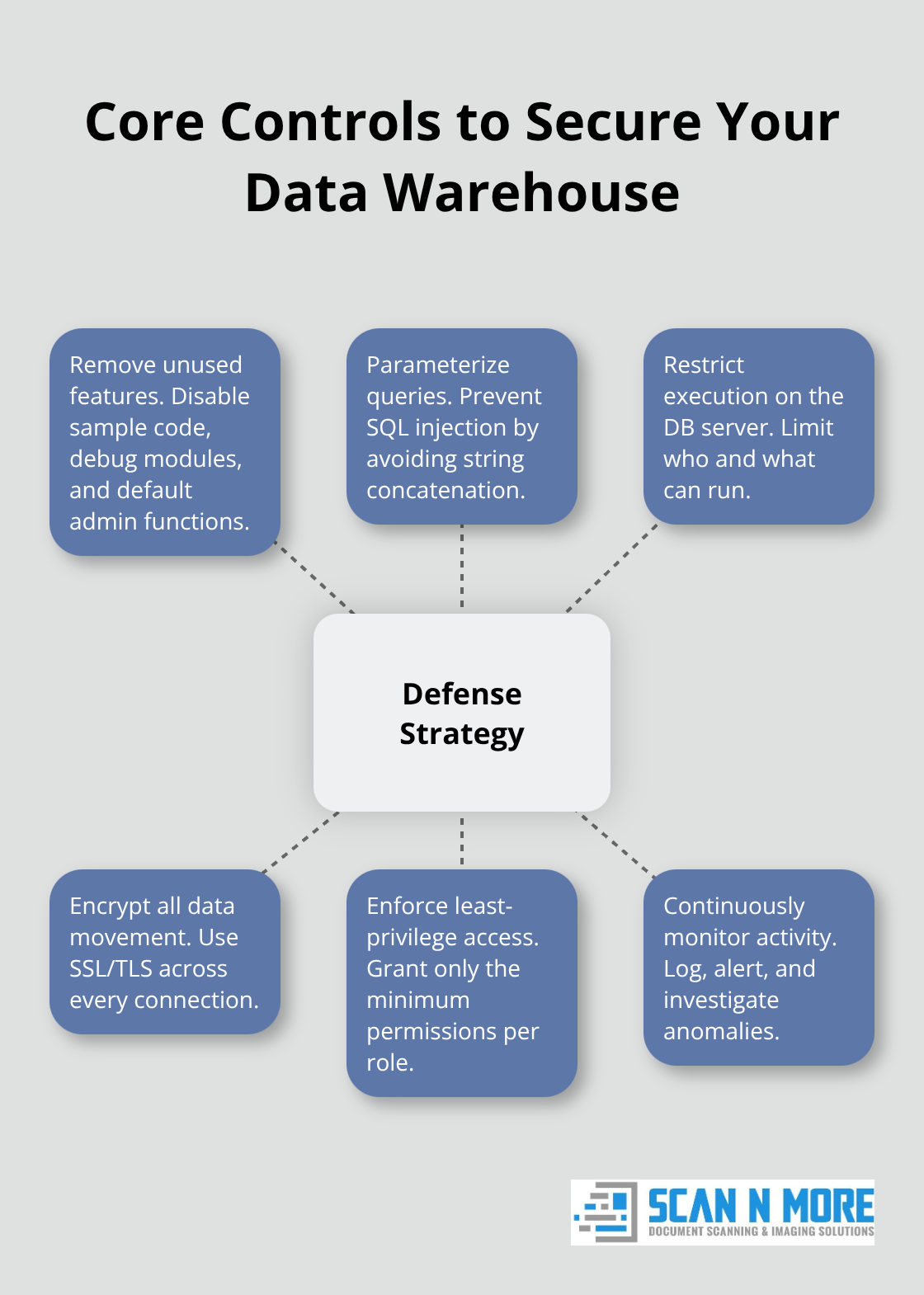
Building Your Defense Strategy
A robust security posture requires removing unused features, implementing parameterized queries to prevent SQL injection, restricting what can execute on your database server, and ensuring all data movement happens through encrypted channels using SSL/TLS protocols. These technical controls form the foundation, but they only work when combined with proper access management and continuous monitoring. Understanding these threats sets the stage for implementing the specific security practices that actually stop attackers from exploiting these vulnerabilities.
How to Lock Down Access and Protect Data
Enforce Multi-Factor Authentication Across All Access Points
Multi-factor authentication prevents unauthorized access to your data and applications by requiring a second method of verifying your identity, making you much more secure. The Hiscox 2024 study found that 40% of companies lack formal security procedures, and weak authentication tops the list of preventable failures. Implement MFA across all data warehouse access points immediately-this means requiring a second form of verification beyond passwords, whether through authenticator apps, hardware tokens, or biometric methods. Organizations that skip MFA essentially hand attackers a golden ticket when they compromise employee credentials through phishing or malware.
Apply the Principle of Least Privilege
Access controls must follow the principle of least privilege, granting each user only the minimum permissions required for their specific role. A finance analyst should never access marketing data; a junior developer shouldn’t modify production schemas. Review and revoke permissions quarterly, especially when employees change roles or leave your organization. This practice prevents insiders from exploiting outdated access grants to steal sensitive information.
Encrypt Data at Rest and in Transit
Encryption transforms data into unreadable information without the correct decryption key, making it worthless to attackers even if they breach your systems. Encrypt all data at rest using AES-256 or FIPS 140-2 certified methods, and encrypt data in transit using SSL/TLS protocols across all network connections. If your organization uses cloud-based data warehouses, verify that encryption happens by default and that you maintain control over encryption keys through customer-managed key options when compliance requirements demand it.
Monitor Activity and Set Real-Time Alerts
Activity logging creates the audit trail that transforms a security incident from catastrophic to manageable. Monitoring tools must capture who accessed what data, when they accessed it, what queries they ran, and whether access succeeded or failed. Set up real-time alerts for suspicious patterns-multiple failed login attempts, unusual query volumes, access attempts outside business hours, or attempts to export large datasets. Organizations that only review logs after a breach has already occurred have already lost. Schedule weekly or monthly log reviews depending on your data sensitivity, and maintain audit records for at least one year to support compliance investigations and incident response.
Test Your Defenses Regularly
Combine these technical controls with regular security assessments and penetration testing to identify weaknesses before attackers do. Test your incident response procedures annually to ensure your team knows exactly how to isolate compromised systems, preserve evidence, and restore operations from encrypted backups. These defensive measures form the foundation of protection, but they only work when organizations pair them with robust backup and disaster recovery systems that ensure data survives attacks intact.
Tools That Actually Stop Data Warehouse Breaches
Configure Firewalls and Intrusion Detection Systems Correctly
Network firewalls and intrusion detection systems form your first line of defense, but they only work if configured correctly. Most organizations deploy firewalls with default settings that leave unnecessary ports open, defeating their purpose entirely. Your firewall should restrict inbound traffic to only essential ports and services your data warehouse requires, block all outbound connections except those explicitly approved, and segment your network so that data warehouse traffic flows through isolated channels separate from general company traffic. Intrusion detection systems monitor network traffic for attack signatures and anomalous behavior patterns, but they generate thousands of alerts daily if not properly tuned.
Configure these systems to alert on high-confidence threats only, then investigate every alert within 24 hours. A 2024 Verizon report found that organizations detecting breaches within days suffered significantly less damage than those taking weeks to notice, which means your detection speed directly impacts your financial exposure. Set up automated responses that immediately isolate suspicious connections and trigger incident response workflows without waiting for manual review.
Deploy Data Loss Prevention Software
Data loss prevention software prevents sensitive information from leaving your data warehouse through unauthorized channels. These tools monitor outbound traffic, email attachments, and file transfers to identify when someone attempts to export datasets containing personal information, financial records, or trade secrets. Configure DLP rules based on your data classification system so that highly sensitive data triggers immediate blocks while moderate-sensitivity data generates alerts for supervisor review. Test your DLP policies quarterly by attempting controlled data exports to verify they actually stop unauthorized movement.
Implement Encrypted Backup and Disaster Recovery Systems
Backup and disaster recovery systems separate from your primary warehouse infrastructure determine whether a ransomware attack becomes a recoverable incident or permanent data loss. Encrypt all backups using customer-managed keys stored in a separate system, store backup copies in geographically distant locations, and restrict access to backup systems to only authorized personnel. Test your recovery procedures monthly by restoring data to a test environment and verifying its integrity and completeness.
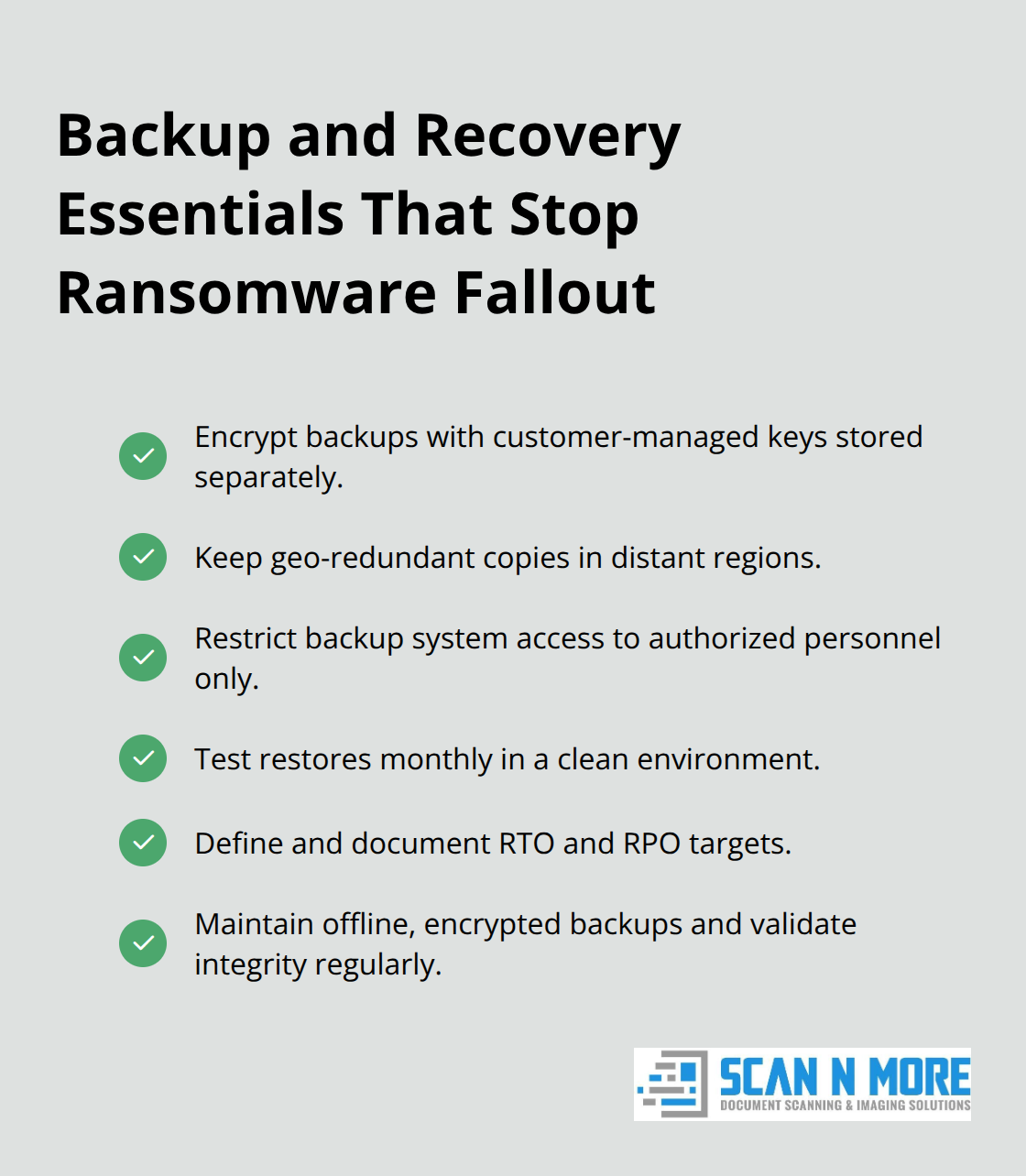
Organizations that discover their backups are corrupted or inaccessible only after a breach has already occurred have wasted their entire backup investment. Document your recovery time objectives and recovery point objectives upfront, then design your backup strategy to meet those targets. A robust backup system means maintaining offline, encrypted backups of critical data and regularly testing their availability and integrity in a disaster recovery scenario.
Final Thoughts
Data warehouse security demands ongoing attention, not a one-time effort that you complete and forget. The threats evolve constantly, and your defenses must adapt to match them. Organizations that treat security as a continuous responsibility-scheduling quarterly permission reviews, testing incident response procedures annually, and monitoring backup systems monthly-experience far fewer breaches than those treating it as a checkbox exercise.
The financial case for prevention is overwhelming. Data breaches cost organizations an average of $4.45 million per incident, while implementing proper controls costs a fraction of that amount. We at Scan N More recognize that data warehouse security extends beyond your digital systems; paper documents containing sensitive information represent an equally serious vulnerability. Our professional document scanning services transform paper-based processes into secure digital solutions with hard drive destruction to eliminate physical data exposure, creating a complete protection strategy.
Start your assessment today by identifying which access controls are missing, where encryption gaps exist, and which monitoring systems need improvement. Assign clear ownership so someone maintains these controls as threats change and your organization grows. Your data warehouse security posture determines whether your organization survives a breach or becomes another statistic in next year’s incident reports.

