Data breaches cost companies an average of $4.45 million in 2023, according to IBM’s Cost of a Data Breach Report. Small businesses face even higher risks, with 60% closing within six months of a cyberattack.
We at Scan N More understand that effective data protection and cyber security requires more than just installing antivirus software. Modern threats demand comprehensive strategies that protect your business from financial loss and reputation damage.
What Protection Methods Actually Work?
Password Security That Stops 99% of Attacks
Companies lose $18.1 billion annually due to weak password practices, according to the Verizon Data Breach Investigations Report. Passwords shorter than 12 characters break within hours when attackers use modern tools. We recommend passphrases with at least 16 characters that combine unrelated words, numbers, and symbols.
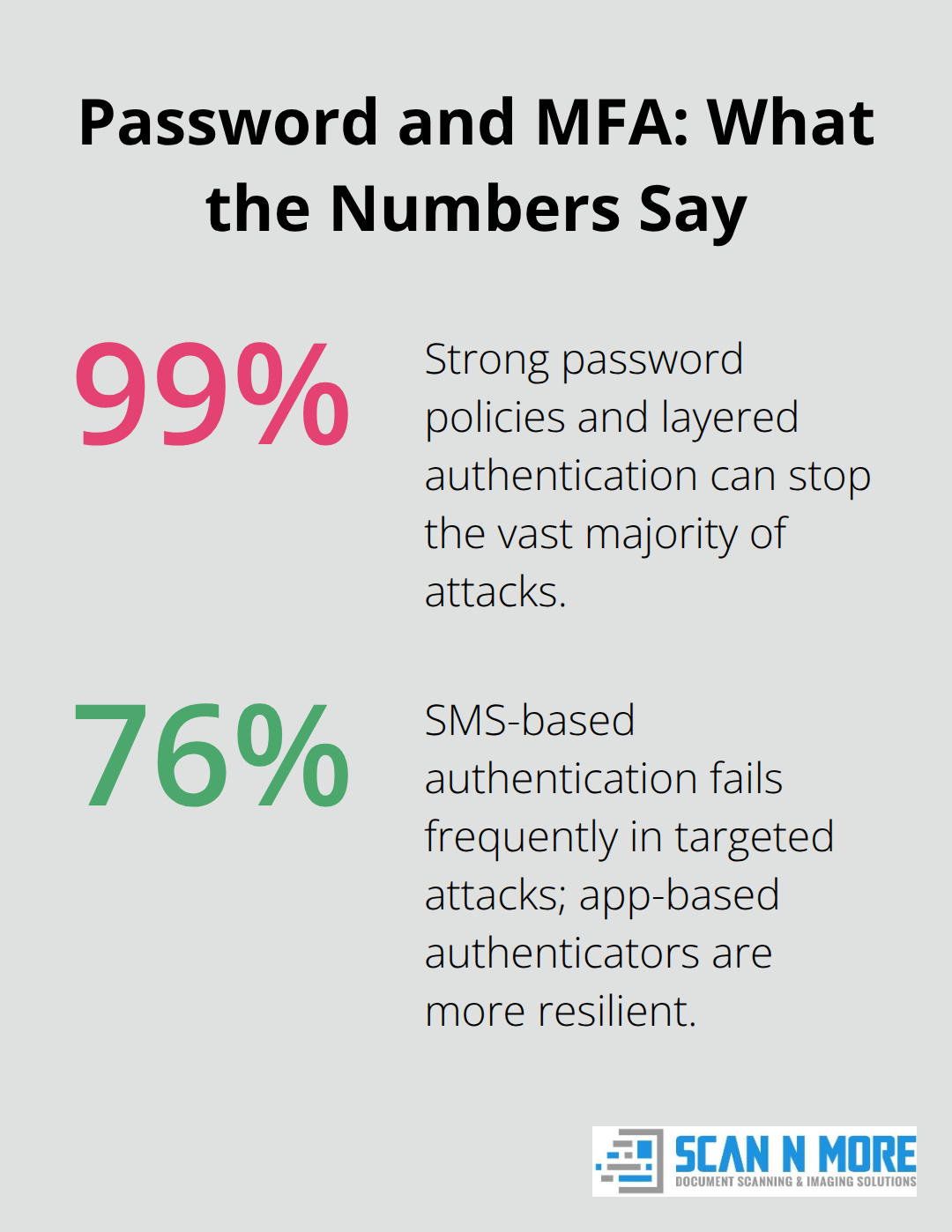
Research shows that multi-factor authentication provides effective protection against cyberattacks, even when passwords face compromise. SMS-based authentication fails in 76% of targeted attacks, so authenticator apps like Microsoft Authenticator or Google Authenticator provide better protection. Biometric authentication provides the highest security level because attackers cannot steal or share these factors.
Backup Strategies That Actually Restore Your Business
The 3-2-1 backup rule is a simple guideline for protecting data: keep 3 copies of your data on two different media types with one copy stored off-site. Test your backup restoration process monthly because 43% of companies discover their backups contain corruption only when emergencies hit. Cloud storage costs dropped 23% in 2023, which makes automated daily backups affordable for small businesses. Recovery time objectives should never exceed four hours for mission-critical systems. When disposing of old storage devices, use secure hard drive disposal services to prevent data breaches.
Employee Training That Changes Behavior
Phishing simulation training reduces successful attacks by 87% when companies conduct it quarterly, according to Proofpoint research. Generic cybersecurity presentations fail to change behavior in 68% of cases. Focus training on real examples from your industry and require employees to identify threats in simulated scenarios. Companies that track click-through rates on simulated phishing emails see 5x better results than those that use passive training methods. Remote document handling demands aggressive security measures that go beyond basic password protection.
These foundational protections create the framework for advanced security measures, but modern threats require additional layers of defense against sophisticated attack vectors.
How Do Modern Cyber Threats Actually Work?
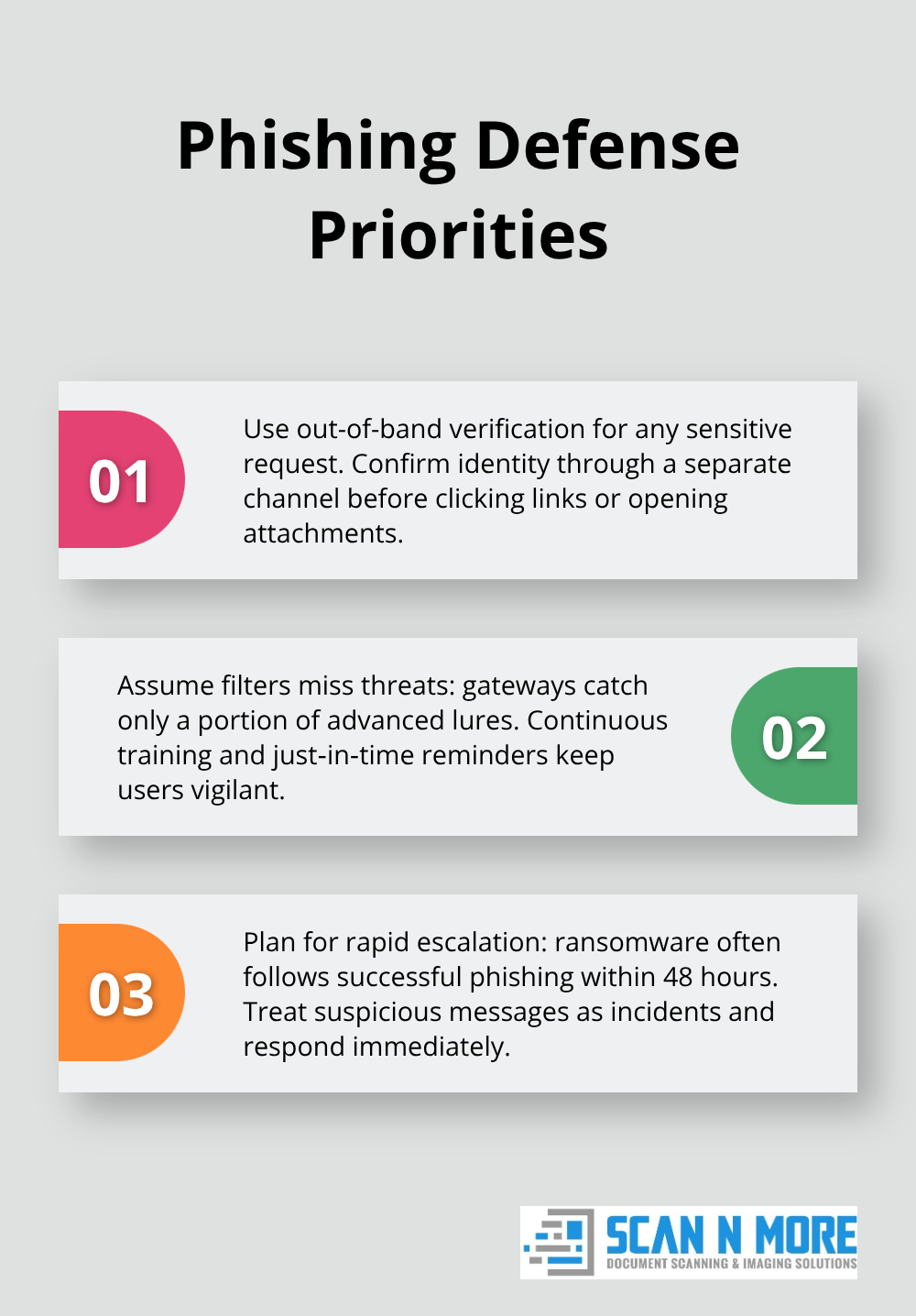
Phishing Attacks Target 83% of Organizations
Phishing remains the most dangerous attack vector because it exploits human psychology rather than technical vulnerabilities. Cybersecurity Ventures provides comprehensive statistics on cybercrime trends, with spear-phishing that targets specific employees reaching success rates of 53%. Attackers now use AI to create personalized emails that reference recent company news or social media activity.
Email security gateways catch only 47% of advanced phishing attempts, according to Proofpoint research. Train employees to verify sender identity through separate communication channels before they click links or download attachments. Ransomware follows 67% of successful phishing attacks within 48 hours.
Firewall Configuration Blocks 94% of Network Intrusions
Default firewall settings provide inadequate protection against modern threats because manufacturers prioritize ease of use over security. Configure firewalls to block all connections that come from outside except those explicitly required for business operations. Next-generation firewalls with deep packet inspection cost 40% more than basic models but prevent 89% more attacks (according to Fortinet research).
Update firewall rules monthly and remove unused port exceptions that create security gaps. Network segmentation through firewall zones prevents lateral movement when attackers breach perimeter defenses. Antivirus software detects only 25% of zero-day malware, so endpoint detection and response solutions provide superior threat identification through behavioral analysis rather than signature matching.
Access Control Systems Stop 91% of Unauthorized Access
Zero-trust architecture requires verification for every network access request, regardless of user location or device status. Companies that implement zero-trust principles experience 68% fewer successful breaches than those that use traditional perimeter security (according to Microsoft research). Role-based access control limits employee permissions to only necessary systems and data.
Privileged access management solutions monitor administrative accounts that attackers target in 74% of data breaches. Network access control systems automatically quarantine devices that lack current security patches or exhibit suspicious behavior.
These technical defenses form your primary protection layer, but regulatory compliance adds another dimension that requires specific documentation and response procedures to avoid legal penalties. When disposing of storage devices, ensure you safely destroy external hard drives to prevent data recovery by unauthorized parties.
What Compliance Requirements Actually Cost You?
GDPR violations can lead to fines of up to €20 million or 4% of global turnover, with Amazon receiving the largest penalty of €746 million according to the European Data Protection Board. US companies face additional risks under state privacy laws, with California’s CCPA imposing fines up to $7,500 per violation. Healthcare organizations must comply with HIPAA requirements that mandate encryption for all patient data transmissions and impose penalties reaching $1.5 million per incident. Financial services firms operate under SOX regulations that require documented data handling procedures and face criminal charges for executives when compliance failures occur.
Documentation Systems That Survive Legal Scrutiny
Audit trails must capture user access attempts, data modifications, and system changes with timestamps that courts accept as evidence. The Federal Rules of Evidence require digital records to include metadata that proves authenticity and prevents tampering.
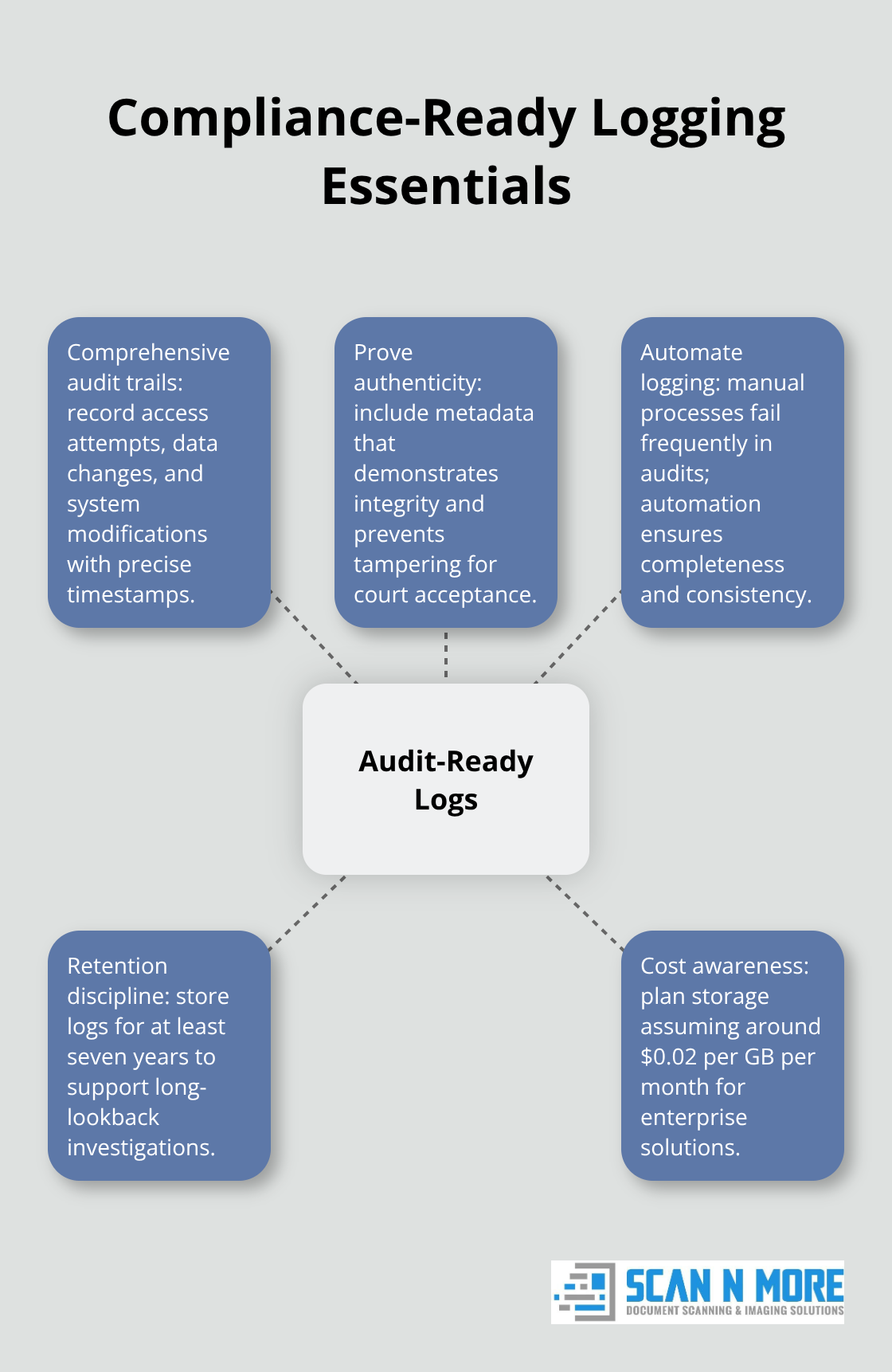
Companies need automated logging systems because manual documentation fails in 89% of compliance audits according to Deloitte research.
Organizations must store audit logs for seven years minimum because regulatory investigations often examine historical patterns spanning multiple years. Data retention policies should specify destruction schedules that balance compliance requirements with storage costs (averaging $0.02 per gigabyte monthly for enterprise solutions).
Breach Response Plans That Minimize Legal Exposure
GDPR requires breach notifications within 72 hours, while state laws impose varying timeframes that create confusion for multi-state operations. Incident response teams must include legal counsel because 67% of data breach lawsuits target companies that delayed notifications beyond regulatory requirements.
Cyber insurance policies cover legal costs averaging $2.4 million per breach but exclude coverage when companies fail to follow documented response procedures. Forensic investigation costs reach $500,000 for enterprise breaches (making rapid containment procedures financially critical for business survival).
Privacy Impact Assessments That Prevent Violations
Companies must conduct privacy impact assessments before they implement new data processing systems or modify existing procedures. These assessments identify potential compliance gaps that could trigger regulatory penalties. Organizations that skip this step face 3x higher violation rates according to privacy consulting firm research.
Assessment documentation must detail data flows, processing purposes, and retention periods with specific legal justifications for each activity. Regular reviews of these assessments help companies adapt to changing regulations and avoid costly compliance failures.
Final Thoughts
Data protection and cyber security demands continuous investment and vigilance rather than one-time implementations. Companies that combine strong password policies, regular backups, and employee training with advanced threat detection reduce breach risks by 85% according to recent industry research. Organizations must adapt their security strategies as new threats emerge and technology evolves.
Security teams catch threats that static defenses miss through active monitoring systems. Network behavior analysis identifies unusual patterns within 24 hours, while quarterly security assessments reveal new vulnerabilities before attackers exploit them. Organizations that conduct monthly penetration tests experience 60% fewer successful attacks than those that rely on annual reviews (making frequent assessment a proven defense strategy).
Digital transformation strengthens security when companies execute it properly. Scan N More provides professional document scanning services that eliminate paper-based vulnerabilities while maintaining data security and compliance standards. Their secure digitization processes reduce physical document risks and support modern access control systems that protect sensitive information more effectively than traditional filing methods.
