Cloud data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 Data Breach Report. Yet many companies still lack solid cloud data security best practices in place.
At Scan N More, we’ve seen firsthand how organizations struggle to balance security with operational efficiency. This guide walks you through the concrete steps needed to protect your data, meet compliance requirements, and build a security culture that actually works.
Understanding Cloud Data Security Threats
Misconfigurations remain the leading cause of cloud data breaches, and organizations are slow to recognize the damage. According to the Verizon 2024 Data Breach Investigations Report, misconfiguration accounts for a significant portion of cloud-related incidents, yet many teams treat security posture management as optional rather than essential. Weak identity and access management compounds this problem.
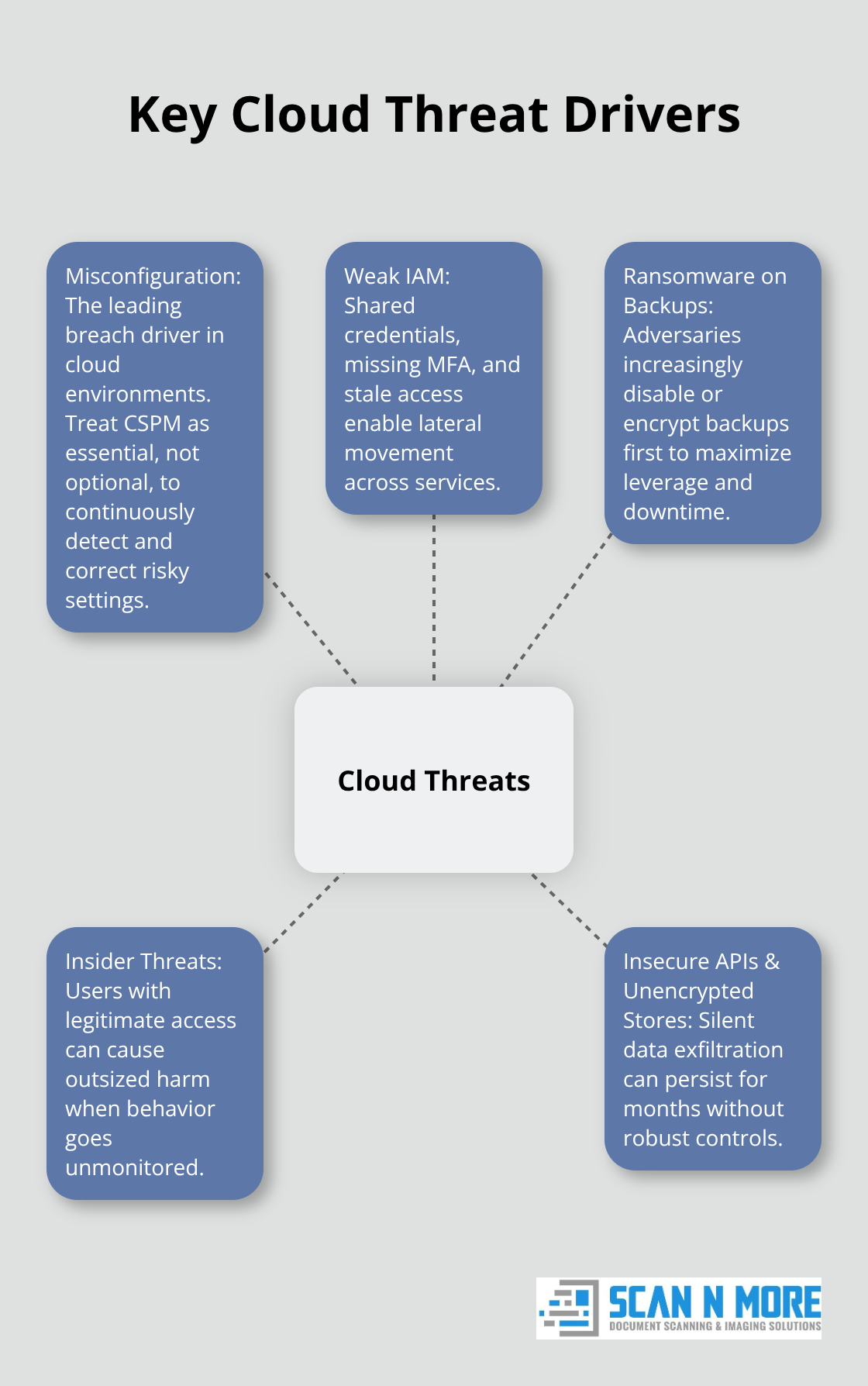
When employees share credentials, fail to use multi-factor authentication, or retain access after role changes, attackers gain footholds that spread across your entire cloud infrastructure.
The Evolving Threat Landscape
Ransomware targeting cloud environments has evolved dramatically, with attackers now focusing on backup systems specifically to maximize leverage. Insider threats from employees with legitimate access represent another critical risk that most organizations underestimate. The 2024 Insider Threat Report from Verizon shows that malicious insiders cause significant damage, yet many companies lack adequate monitoring of user behavior within cloud systems. Data exfiltration through insecure APIs and unencrypted data stores happens silently, sometimes remaining undetected for months.
Compliance Violations and Financial Impact
Compliance violations carry steep consequences beyond financial penalties. GDPR fines reach up to 20 million euros or 4 percent of global revenue (whichever is higher), while HIPAA violations cost healthcare organizations an average of 100,000 to 50 million dollars per breach depending on scope. PCI-DSS non-compliance results in fines starting at 5,000 dollars monthly and can escalate dramatically. Your responsibility under the shared responsibility model means that cloud providers handle infrastructure security, but you must secure your configurations, data encryption, access controls, and applications.

This distinction matters enormously because misconfigured storage buckets, unencrypted databases, and overly permissive IAM policies fall squarely on your shoulders.
Immediate Vulnerabilities in Your Environment
Most organizations discover their vulnerabilities only after an incident occurs. Publicly accessible S3 buckets, unencrypted databases, and excessive IAM permissions represent the fastest path to breach. Credential compromise happens through phishing attacks that target your employees with alarming success rates. Once attackers obtain valid credentials, they move laterally through your cloud environment with minimal friction. DDoS attacks against cloud infrastructure can cost 5,000 to 100,000 dollars per hour in downtime and remediation (depending on your service scale and response capabilities). Supply chain attacks now frequently target cloud infrastructure, with attackers compromising third-party vendors to gain access to your systems.
Frameworks That Guide Your Defense
Frameworks like NIST CSF 2.0, CIS Benchmarks, and CSA CCM provide structured approaches to identifying and closing gaps. CIS Benchmarks specifically offer secure baseline configurations for AWS, Azure, and Google Cloud that you can implement immediately. Organizations that align with these standards reduce their breach risk significantly while demonstrating due diligence to regulators and customers. Without this alignment, you operate without clarity on what constitutes adequate protection. Understanding these threats sets the stage for implementing the specific security measures that actually stop attackers from reaching your data.
How to Implement Encryption, Access Control, and Real-Time Monitoring
Encryption Protects Data at Every Stage
Encryption stands as your first line of defense, yet most organizations encrypt only a fraction of their cloud data. Start with encryption at rest using AES-256 for all databases, storage buckets, and file systems. AWS KMS, Azure Key Vault, and Google Cloud KMS provide native encryption services that integrate directly into your infrastructure without requiring separate tooling. The cost remains negligible compared to breach remediation expenses.
Encryption in transit must use TLS 1.2 or higher for all API calls and data transfers between services. Many teams assume their cloud provider handles this automatically, but you need to verify that all connections use strong ciphers and that certificate validation occurs on both ends. This verification step catches misconfigurations that leave data exposed during transmission.
Access Control Limits Damage When Breaches Occur
Access control requires enforcing the principle of least privilege across every service account, user role, and application. An employee accessing customer databases should have read-only permissions to specific tables, not blanket database access. AWS IAM, Azure Entra ID, and Google Cloud Identity integrate with your on-premises Active Directory through single sign-on to maintain consistent credential management across environments.
Regular permission audits catch role creep where employees retain access from previous positions. Multi-factor authentication becomes non-negotiable for all production cloud access, particularly for privileged accounts. Attackers with valid credentials and MFA-protected access face dramatically higher barriers to entry, making your systems far less attractive targets.
Real-Time Monitoring Stops Attackers Before They Spread
Real-time monitoring detects breaches while damage remains contained rather than weeks later. Real-time monitoring with Cloud Security Posture Management tools continuously scan configurations against security baselines and alert when deviations occur. CIS Benchmarks provide the exact configurations you should enforce across AWS, Azure, and Google Cloud.
Behavioral analytics identify unusual login patterns, impossible travel scenarios, and anomalous data access that signature-based detection misses entirely. Centralized logging sends all cloud activity to a single repository where you can correlate events and identify attack chains. Most breaches involve lateral movement that spans multiple services, and centralized logs reveal these patterns immediately.
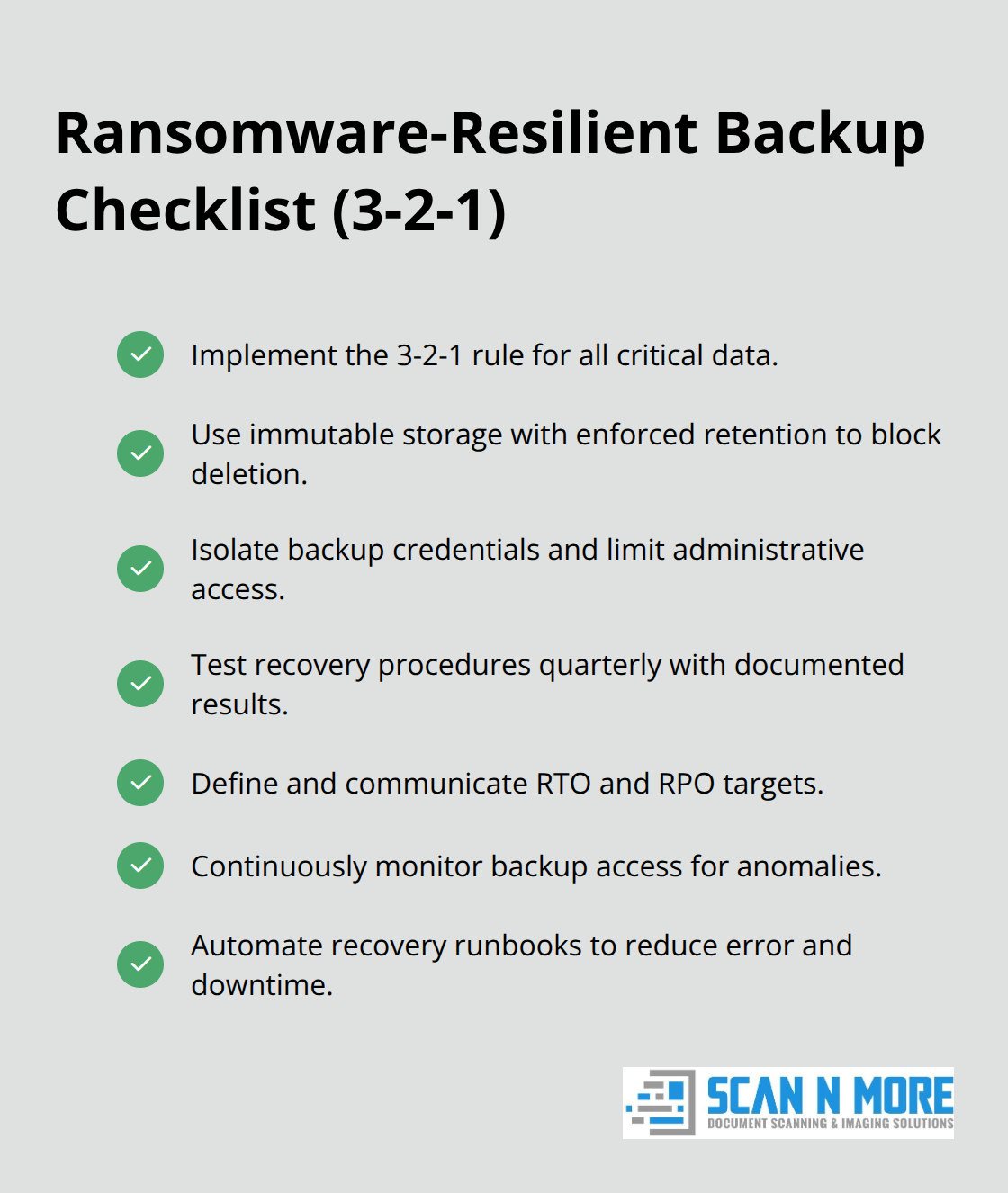
Backup and Disaster Recovery Survive Ransomware Attacks
Backup and disaster recovery strategies must operate independently from your primary cloud infrastructure to survive ransomware attacks that encrypt entire environments. The 3-2-1 rule requires three copies of your data, stored on two different media types, with one copy offsite. Test recovery procedures quarterly because untested backups fail when you need them most.
Ransomware attackers specifically target backup systems to eliminate recovery options, so restrict backup access through separate credentials and immutable storage settings that prevent deletion for a defined retention period. Document your recovery time objective and recovery point objective so teams understand acceptable data loss and downtime before implementing systems. With these technical controls in place, your organization now needs the human element to complete the security picture-which means building a culture where employees actively protect data rather than inadvertently expose it.
How to Build Security Into Your Organization’s DNA
Technical controls only work when your team actively supports them. The FBI IC3 reported that Business Email Compromise caused significant losses during 2022, and most of those incidents succeeded because employees clicked malicious links or shared credentials without questioning the request. Organizations with strong security cultures experience far fewer breaches than those relying solely on technology. Your employees represent either your strongest defense or your greatest vulnerability, depending on how you approach training and culture.
Phishing Simulations Reduce Employee Vulnerability
Phishing remains the most effective attack vector because it exploits human psychology rather than technical flaws. Conduct phishing simulations monthly and track which employees consistently fall for fraudulent messages, then provide targeted training to those individuals rather than generic company-wide sessions that bore experienced staff. Organizations that implement this approach see phishing click rates decrease through repeated exposure to phishing simulation exercises. Require multi-factor authentication specifically for email and cloud access because compromised email credentials grant attackers the ability to reset passwords and access sensitive systems.
Vendor Selection Demands Transparency and Proof
When selecting cloud providers, demand detailed security documentation including penetration testing results, vulnerability disclosure policies, and third-party security audits. Ask vendors directly whether they conduct regular penetration testing and whether they’ll share SOC 2 Type II reports that validate their security controls. Providers who refuse transparency on these points deserve immediate elimination from consideration. This vetting process prevents partnerships with vendors who cut corners on security.
Leadership Actions Shape Security Culture
Security culture develops when leadership demonstrates that data protection matters through actions, not just policy documents. Allocate budget specifically for security tools and training rather than treating it as an afterthought. When your CEO visibly supports security initiatives and holds department leaders accountable for compliance metrics, employees recognize that protecting data affects their performance evaluations. Establish clear consequences for security violations, including credential sharing or bypassing MFA, so employees understand that these actions carry real weight.
Security Champions Prevent Bottlenecks and Spread Knowledge
Create dedicated security champions within each department who receive advanced training and serve as first-line resources for colleagues facing security decisions. These champions prevent bottlenecks where overly strict policies force employees into workarounds that compromise security. Rotate security responsibilities across teams so knowledge spreads beyond a single individual who might leave the organization. Document your cloud security policies using policy-as-code frameworks that automatically enforce restrictions rather than relying on manual compliance checks that consistently fail.
Final Thoughts
Cloud data security best practices require commitment across three dimensions: technology, process, and people. Technical controls matter enormously-encryption, access management, real-time monitoring, and backup systems form your foundation. Yet these tools fail without processes that enforce consistent implementation and people who understand why security decisions matter to their daily work.
Start by auditing your current state against CIS Benchmarks for your cloud provider and identify which configurations deviate from secure baselines. Implement Cloud Security Posture Management tools that continuously monitor for drift rather than relying on annual assessments that miss changes happening between reviews. Enforce multi-factor authentication immediately for all production access because this single control blocks the majority of credential-based attacks that plague organizations today.
Organizations with strong cloud data security practices experience faster incident response times, reduced regulatory scrutiny, and improved customer trust. If your organization still manages paper-based documents alongside cloud systems, consider how Scan N More transforms document security through professional scanning services that eliminate physical data exposure while ensuring compliance with encryption and secure destruction protocols. Start implementing these practices this week, not next quarter.

