Data security regulations keep getting stricter every year. Companies that ignore them face hefty fines, lawsuits, and damaged reputations.
At Scan N More, we’ve seen firsthand how confusing these rules can be. This guide breaks down what you actually need to do to stay compliant and protect your data.
Which Regulations Actually Apply to Your Business
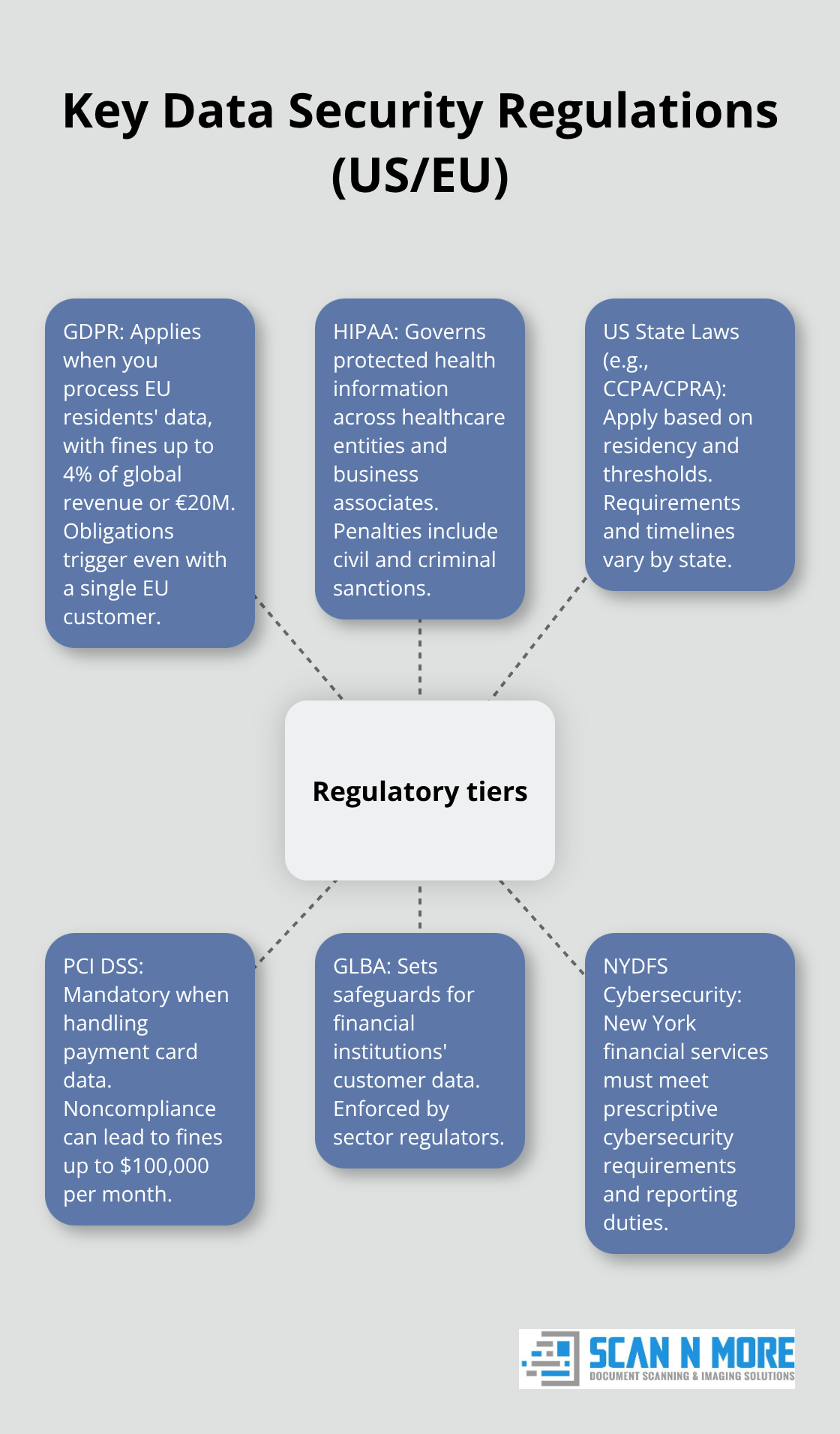
The regulatory landscape splits into three tiers, and knowing which applies to you determines your compliance costs and timeline. GDPR applies if you process data of European Union residents, regardless of where your company operates. The threshold is strict: even a single customer in the EU triggers GDPR obligations. Fines reach up to 4% of annual global revenue or €20 million, whichever is higher. Meta paid €1.2 billion in 2023 for GDPR violations, and Amazon faced €746 million in 2021. These weren’t small oversights-they involved systemic data handling failures.
If you operate in healthcare, HIPAA covers patient data for any organization handling electronic health information, from hospitals to insurance providers to business associates. HIPAA violations carry civil penalties up to $1.5 million per year and criminal penalties up to 10 years imprisonment.
The second tier covers US state laws. California’s CCPA applies to any for-profit business collecting data from California residents if you hit revenue thresholds or process data of 100,000+ people. Since 2024, 22 US states have enacted comprehensive privacy laws, with 15 considered fully comprehensive. Colorado, Connecticut, Virginia, Utah, and Texas all passed laws with different scopes and timelines. CCPA penalties range from $2,500 to $7,500 per violation, plus statutory damages of $100 to $750 per consumer per incident for unencrypted data breaches.
The third tier involves industry-specific rules. PCI DSS applies if you handle payment card data, with fines up to $100,000 monthly for noncompliance. Sector regulators enforce GLBA for financial institutions and NYDFS cybersecurity rules for New York-based financial services.
Map Your Data Systems
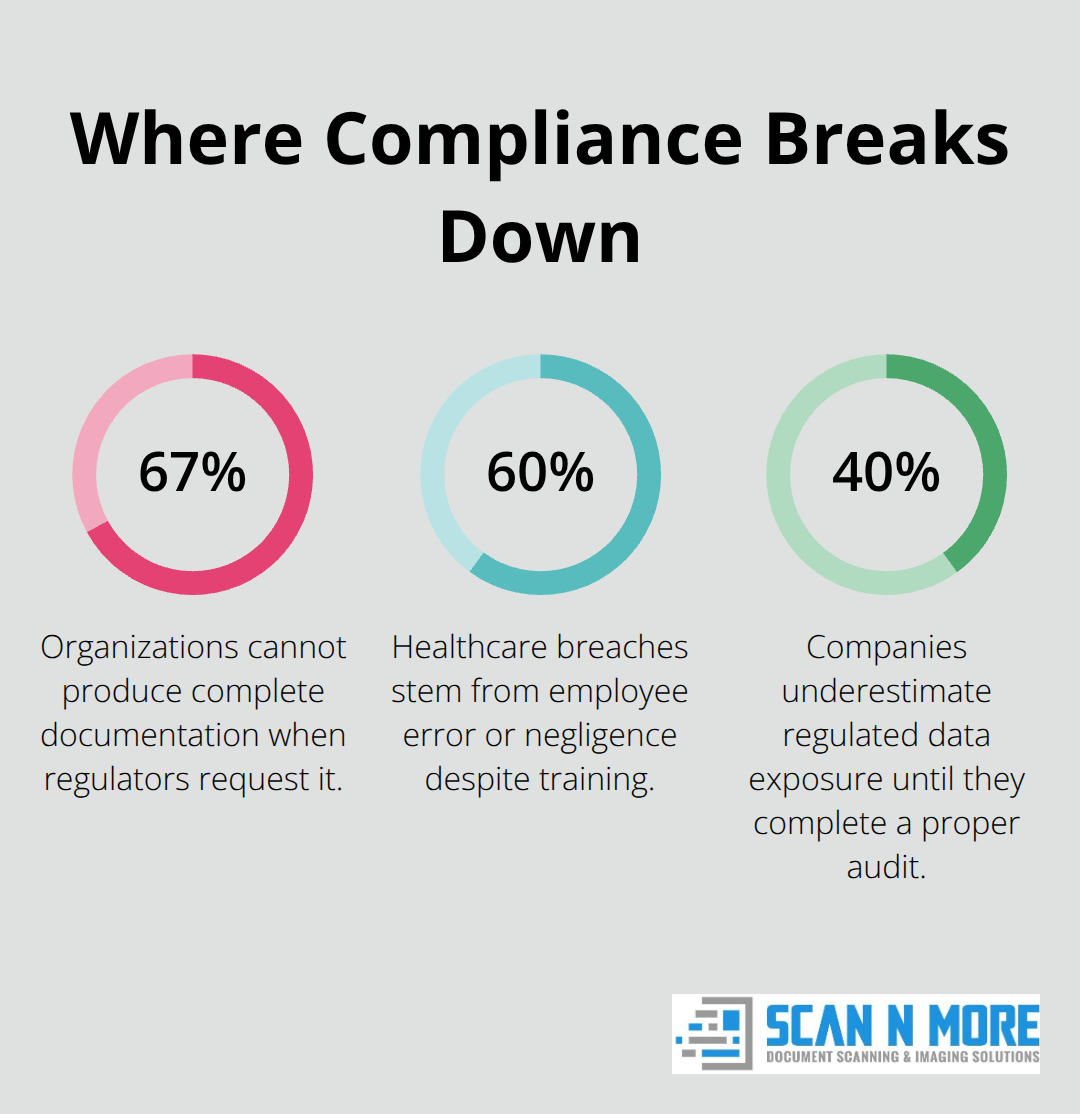
Your first action should be mapping what data you actually collect and where it flows. Most companies underestimate their regulated data exposure by 40% until they conduct a proper audit. You need to document every system storing personal information: customer databases, employee records, vendor files, backup systems, cloud storage.
Classify each data type by sensitivity. NIST frameworks suggest labeling data as public, internal, confidential, or restricted. Restricted data includes payment card information, health records, and precise geolocation data. This classification directly drives which controls apply and which regulations take precedence.
If you collect geolocation data, Connecticut, Utah, and other states define precise geolocation as highly sensitive if it narrows location to a specific radius. Know your exact definitions.
Control Who Accesses What
Access controls matter more than most companies realize. You should enforce least-privilege access: employees access only the data required for their role. Use role-based access control combined with contextual signals like device posture, location, and time. This zero-trust approach catches unauthorized access attempts before data leaves your systems.
GDPR requires you to document your lawful basis for processing each data type. HIPAA mandates minimum necessary standards for healthcare data. If you cannot justify why a person needs access to specific data, they should not have it.
Test your access controls quarterly. Many breaches involve inactive accounts or people accessing data months after they changed roles. This simple practice prevents the majority of insider-risk incidents.
Enforce Data Classification Rules
Once you classify data, you must enforce rules that match sensitivity levels to access restrictions. Restricted data requires multi-factor authentication and encryption at rest and in transit. Confidential data needs role-based access with audit logging. Public data can flow more freely, but you still track who accesses it.
The enforcement step separates compliant organizations from those that fail audits. You can have perfect policies on paper, but without technical controls that prevent violations, regulators will find gaps. Implement attribute-based access control (ABAC) to automate these rules across your systems and cloud platforms.
Your next step involves building the broader compliance framework that ties these access controls to documented policies and regular testing.
Building Your Compliance Framework
Your access controls and data classification only work if they sit within a structured compliance framework that you test regularly. Most companies treat compliance as a one-time project rather than an ongoing operation, which is why they fail audits two years after implementation. You need three specific mechanisms: a baseline audit to identify your current state, technical controls that enforce your policies automatically, and documented retention policies that you actually execute.
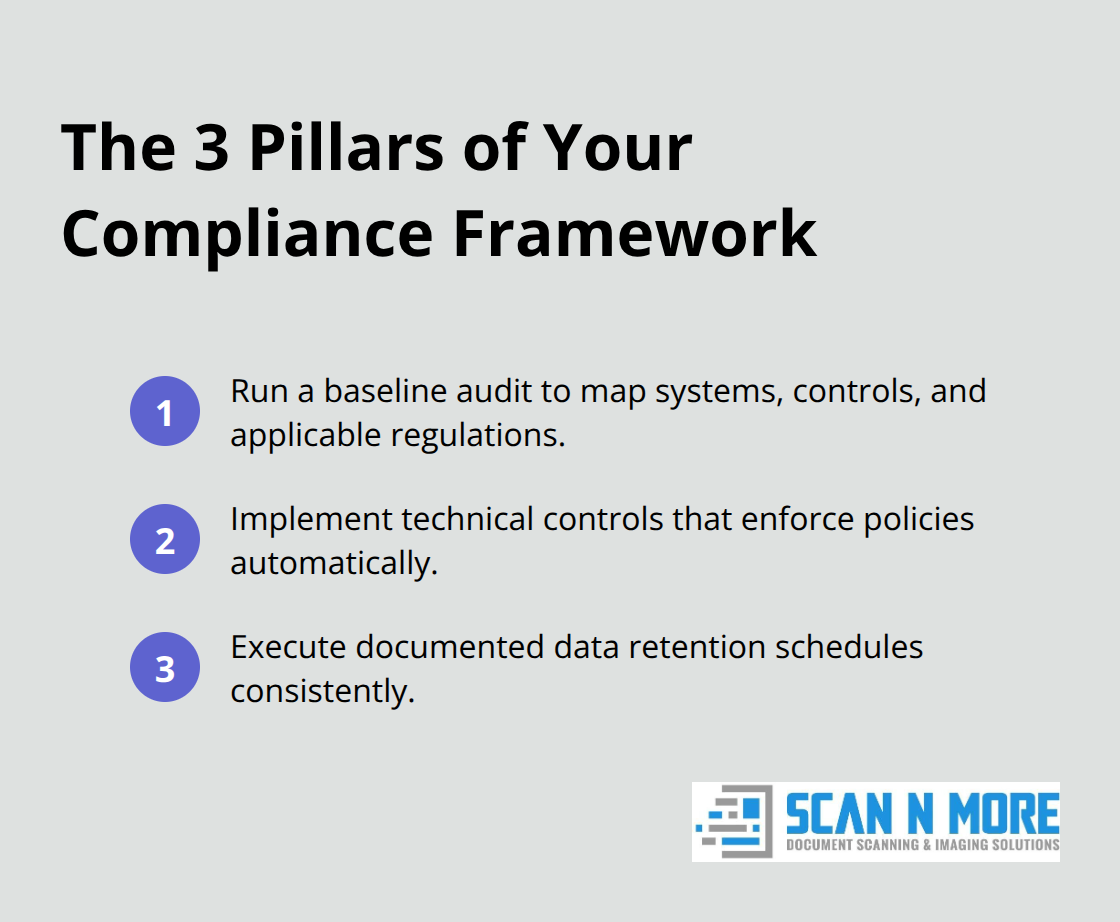
Conduct an honest audit of your current state
Schedule a data security audit within the next 60 days if you haven’t completed one in the past year. This isn’t optional if you handle regulated data. The audit should inventory every system storing personal information, document your current access controls, and identify which regulations apply to each data type. NIST SP 800-53 provides the framework most auditors use, and it includes specific control families for data protection, access management, and incident response.
During the audit, test whether your documented policies actually match what happens in practice. You’ll almost always find gaps. One healthcare organization discovered that 23% of their employee accounts retained database access six months after the employee left the company. Another financial services firm found backup systems with unencrypted customer data stored in a secondary location that nobody had documented. These aren’t rare exceptions-most audits uncover similar oversights.
Document everything you find, prioritize the highest-risk gaps, and assign owners to fix them within 90 days. If you lack internal audit expertise, hire external consultants for at least the first audit. The cost typically ranges from $15,000 to $50,000 depending on organization size, but it prevents far more expensive regulatory penalties later.
Encrypt data at rest and in transit with verified key management
Encryption stands as the single most important technical control you can implement. GDPR, HIPAA, PCI DSS, and CCPA all expect encryption for sensitive data. Use AES-256 for data at rest and TLS 1.2 or higher for data in transit. Your cloud providers and database vendors handle most of this for you.
The real work involves key management. Many organizations encrypt their data but store encryption keys in the same location, which defeats the purpose. Separate key storage from data storage. Use dedicated key management services like AWS Key Management Service or Azure Key Vault. Test your encryption quarterly by attempting to access encrypted data without the proper keys. If you can still read the data, your encryption isn’t working.
For non-production environments like development and testing systems, stop using real customer data. Mask sensitive fields or use synthetic data instead. This reduces your compliance burden significantly. If a developer’s laptop gets stolen, you’re not notifying customers of a breach because the laptop contained only masked data. HIPAA allows this approach and actively encourages it.
Delete data according to documented retention schedules
Document how long you keep each data type. GDPR requires you to delete personal data when you no longer need it. CCPA gives California residents the right to deletion. Yet most companies keep data indefinitely because deletion requires work.
Set specific retention periods: customer payment data might stay for 7 years for tax purposes, but marketing email lists should be deleted 24 months after last contact. Write these policies down and assign someone to execute them quarterly. Automated deletion works better than manual processes. Configure your systems to automatically purge data after the retention period expires.
Test the deletion process to confirm data actually gets removed. Many organizations delete database records but forget about backups, archived logs, or cached copies. When regulators ask for proof of deletion, you need to show that data is gone from every copy, not just the primary system. Document each deletion cycle and retain those records for audit purposes.
Prepare for the compliance testing phase ahead
These three mechanisms-audits, encryption, and deletion-form the foundation that regulators expect to see. The next phase involves testing these controls under real conditions and documenting your compliance evidence for audits and assessments.
Where Compliance Programs Actually Fail
Most organizations fail audits not because they lack policies, but because they never test whether those policies work in practice. Documentation gaps represent the largest compliance failure across industries. GDPR requires you to maintain records proving you have a lawful basis for processing each data type, document your data protection impact assessments, and keep evidence of consent when required. HIPAA demands you document every access to patient data, maintain audit logs, and prove you trained staff on security. Yet 67% of organizations cannot produce complete documentation when regulators request it. The problem isn’t that these records don’t exist somewhere-it’s that they’re scattered across email threads, spreadsheets, forgotten shared drives, and people’s heads.
Create a Central Compliance Register
Start documenting now by creating a central compliance register. List every data type you collect, the regulation governing it, your lawful basis for processing, the retention period, and who can access it. Update this register quarterly as your systems change. This single document becomes your foundation for every audit and assessment. When regulators ask for proof of compliance, you pull this register and show exactly what you collect, why you collect it, and how you protect it. Organizations that maintain this register pass audits 3x faster than those scrambling to reconstruct their data practices from scattered sources.
Train Your Team on Real Scenarios, Not Annual Checkboxes
Employee training fails because most organizations treat it as a checkbox item rather than ongoing reinforcement. You conduct annual training, employees click through a quiz they don’t read, and nothing changes. Healthcare organizations with mandatory HIPAA training still experience 60% of breaches from employee error or negligence. The issue isn’t that people are careless-it’s that training happens once yearly while employees face daily decisions about data.
Train staff quarterly on scenarios specific to their role. A developer needs different training than an accountant. Show them real examples of what compliance violations look like in your systems. Have your finance team practice identifying phishing emails targeting payment data. Have customer service representatives demonstrate proper handling of customer deletion requests under CCPA. Track who completes training and when, then follow up with anyone overdue. Make training mandatory for access to sensitive systems. If someone hasn’t completed quarterly training, their access to customer databases or health records should be suspended. This creates immediate accountability rather than abstract compliance concepts.
Assess Vendor Security Before You Sign Agreements
Third-party vendors create your largest compliance liability. If your payment processor gets breached, regulators ask why you didn’t verify their security controls beforehand. If your cloud provider experiences data loss, you’re responsible for not assessing their backup procedures. Yet most companies sign vendor agreements without reviewing security practices.
Before engaging any vendor with access to regulated data, require them to complete a vendor security assessments covering encryption, access controls, incident response, and data retention. Ask for SOC 2 Type II reports or ISO 27001 certifications. Request their breach notification timeline-if they won’t commit to notifying you within 24 hours of a breach, find another vendor. Document everything and maintain a vendor risk register listing each vendor, the data they access, their certification status, and when you last assessed them. Reassess vendors annually or whenever they notify you of security changes. This prevents the common scenario where your vendor’s security posture degrades over time and you discover it during an audit.
Final Thoughts
Compliance with data security regulations requires ongoing operational discipline rather than a one-time project completion. Organizations that avoid regulatory penalties maintain a central compliance register listing every data type and its governing rules, train staff quarterly on real scenarios rather than annual checkbox exercises, and assess vendor security before signing agreements. Start with your data inventory this month, classify what you collect by sensitivity level, and assign someone to own your compliance register.
The cost of non-compliance far exceeds the cost of compliance itself. GDPR fines reach 4% of annual revenue, HIPAA penalties climb to $1.5 million yearly, and CCPA statutory damages accumulate across affected consumers. Beyond financial penalties, breaches damage customer trust and your market reputation. Compliance also creates operational benefits: stronger access controls reduce insider-risk incidents, documented data flows help you respond faster to customer deletion requests, and regular audits catch security gaps before attackers find them.
We at Scan N More understand that data security extends beyond digital systems. When you transition from paper-based processes to digital solutions, you need partners who handle sensitive documents with compliance in mind. Our document scanning services ensure your paper records are digitized securely while maintaining the data protection standards your compliance program requires.
