Data breaches cost organizations an average of $4.45 million per incident, according to IBM’s 2024 Cost of a Data Breach Report. The stakes have never been higher for businesses protecting sensitive information.
At Scan N More, we know that implementing enterprise data security solutions isn’t optional anymore-it’s a business requirement. This guide walks you through selecting, deploying, and maintaining security systems that actually work for your organization.
Understanding Enterprise Data Security Threats
Ransomware, Phishing, and Lateral Movement
Ransomware attacks hit 2,777 organizations in the United States during 2024. These attacks encrypt critical business data and demand payment, forcing companies to choose between paying criminals or losing access to essential operations. Phishing remains the entry point for most breaches, with attackers using fake emails and social engineering to trick employees into revealing credentials or downloading malware.
When credentials fall into the wrong hands, attackers move laterally through your network, accessing databases, cloud storage, and file servers without triggering traditional security alerts. The IBM 2024 Cost of a Data Breach Report revealed that the average dwell time for undetected breaches is 207 days-meaning attackers operate inside your systems for months before discovery, exfiltrating sensitive customer data, financial records, and intellectual property.
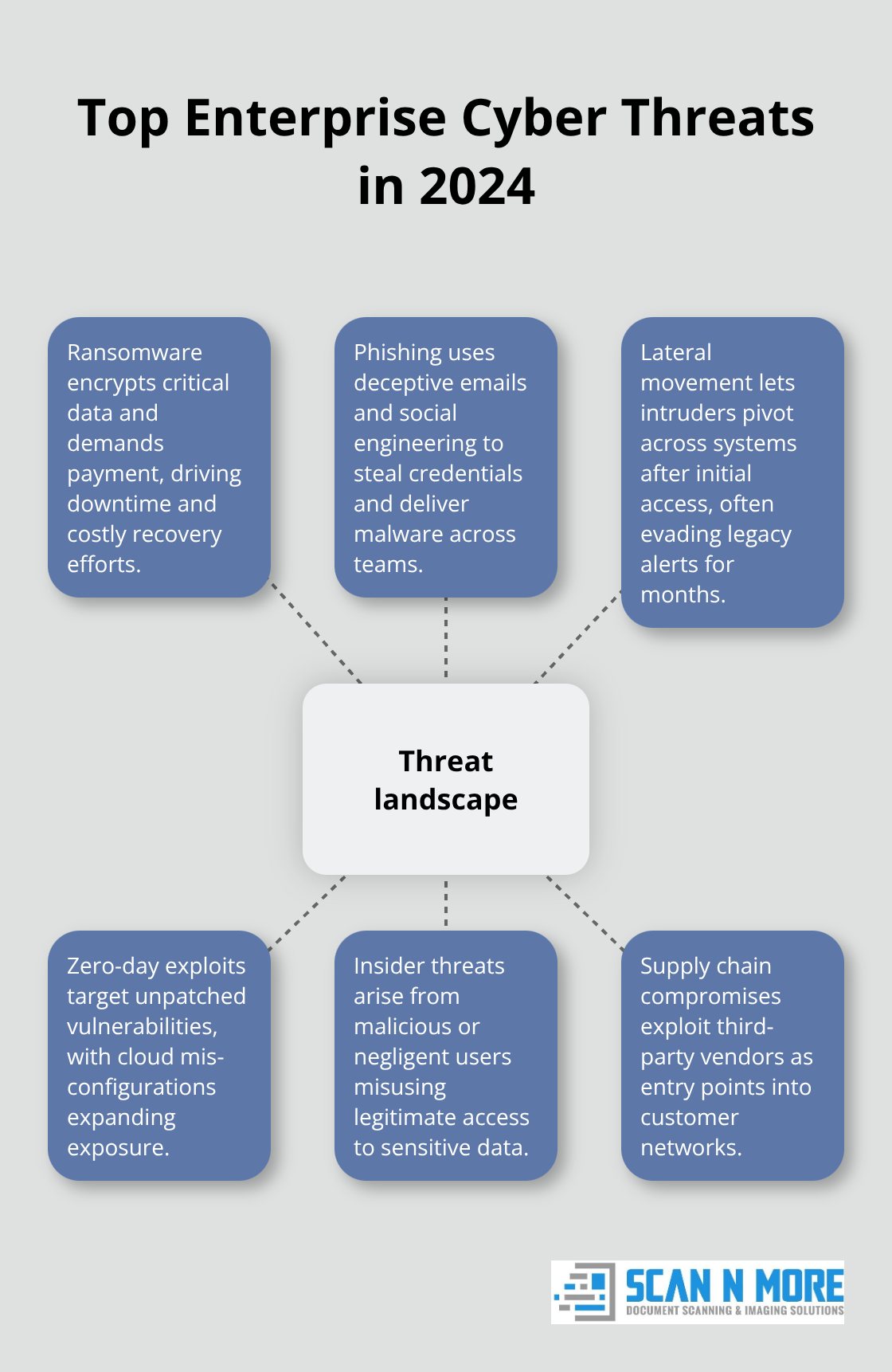
Zero-Day Exploits and Configuration Failures
Zero-day exploits targeting unpatched software vulnerabilities create additional exposure, especially in cloud environments where configuration mistakes leave storage buckets and databases exposed to the internet. Insider threats pose a different challenge entirely. Disgruntled employees or contractors with legitimate access intentionally steal data, or negligent staff accidentally share sensitive information through unsecured channels.
Supply chain compromises add another layer of risk, where attackers infiltrate third-party vendors to gain access to their customers’ networks. Your organization faces threats from multiple angles simultaneously, which is why a layered defense strategy matters far more than relying on any single security tool.
Regulatory Penalties Drive Real Financial Consequences
GDPR violations cost organizations up to 20 million euros or 4 percent of annual revenue, whichever is higher. HIPAA breaches affecting 500 or more individuals trigger mandatory federal notifications and potential fines exceeding 1.5 million dollars per violation category. PCI DSS compliance is non-negotiable for any organization processing payment card data, with penalties reaching 100,000 dollars per month for non-compliance.
These represent real financial consequences that directly impact your bottom line. Organizations that suffer data breaches face additional costs from notification requirements, credit monitoring services, legal fees, and reputational damage. A single breach can destroy customer trust, drive away business, and take years to recover from.
Building Visibility Across Your Data Landscape
The regulatory landscape continues tightening. California’s CCPA and similar state privacy laws create fragmented compliance requirements that demand comprehensive data governance. Your organization needs visibility into where sensitive data exists, who accesses it, and how it moves across on-premises systems, cloud platforms, and third-party vendors.
Without this visibility, you cannot demonstrate compliance to auditors or protect data effectively. Building enterprise data security means treating compliance as a driver for security architecture rather than a checkbox exercise. The next step involves assessing what your organization actually needs to defend against and which security solutions fit your specific risk profile.
Choosing the Right Security Technologies for Your Organization
Start with Data Discovery and Classification
Start with a data inventory before evaluating any vendor or technology. You cannot select appropriate security solutions without knowing what you are protecting. Conduct an automated discovery across your entire IT environment to identify where sensitive data lives, including shadow IT applications and unsanctioned cloud services that employees use without approval. Classify this data by sensitivity level and business criticality, creating categories like public, internal, confidential, and highly confidential. This classification determines which security controls matter most.
Organizations that skip this step waste money on tools they do not need while leaving critical gaps unprotected. The NIST Cybersecurity Framework explicitly emphasizes asset discovery and classification as foundational to all other security controls. Once you understand your data landscape, you gain the foundation needed to make informed technology decisions.
Assess Your Organization’s Specific Threat Profile
Assess which specific threats pose the greatest risk to your organization. A healthcare provider faces different threats than a financial services firm or a manufacturing company. Ransomware poses an existential threat to hospitals, while payment card theft dominates risk discussions in banking. Zero-day exploits matter more to organizations running outdated legacy systems than to those with modern infrastructure.
Insider threats become critical when you employ contractors with broad system access. This risk assessment shapes your technology priorities and prevents you from purchasing expensive solutions addressing threats that do not apply to your business. Your threat profile determines which capabilities matter most in your security stack.
Demand Proof of Detection Capabilities
Evaluate vendors based on their actual detection and response capabilities rather than marketing claims. Request proof that their tools identify real attacks in your environment through proof-of-concept testing. Ask vendors to demonstrate how their solution would have detected the 2024 ransomware attacks that hit 2,777 U.S. organizations, or the specific phishing campaigns targeting your industry. Demand concrete numbers about detection rates, false positive rates, and response time.
Many vendors inflate statistics or measure success differently than you do. When comparing endpoint detection and response (EDR) solutions, ask how quickly the tool detects lateral movement after initial compromise, since the average dwell time of 207 days shows attackers operate inside networks undetected for months. For data loss prevention (DLP) tools, test whether they accurately identify your most sensitive data without generating alert fatigue that forces your team to ignore warnings.
Prioritize Integration Over Point Solutions
Budget constraints matter, but they should never drive you to purchase fragmented point solutions that do not integrate. A single powerful platform costs less to operate and maintain than multiple disconnected tools requiring different teams and training. Align your solution selection with your organization’s remediation capacity.
If your security team has only two people, enterprise-grade solutions generating thousands of daily alerts will overwhelm them. Choose technology that matches your team’s size and skill level, or budget for managed security services to supplement internal resources. Your next step involves evaluating specific vendors and understanding how their solutions fit into your broader security architecture.
How to Deploy Security Without Overwhelming Your Team
Match Implementation Pace to Your Team’s Capacity
Deployment success depends on building a realistic timeline that your organization can actually execute. Many companies purchase enterprise security solutions only to watch them sit partially configured because the deployment process demands more expertise and resources than available. Start deployment with your highest-risk assets and most critical data first, then expand methodically to lower-risk areas. This approach delivers immediate protection where threats matter most while your team masters new tools before scaling further.
IBM’s 2024 Cost of a Data Breach Report shows that the average global breach cost has reached USD 4.88 million. This maturity develops through sustained implementation effort rather than rushed deployments that leave gaps in your defenses.
Target Security Training to Real Vulnerabilities
Security awareness training must address specific behaviors that create vulnerability, not generic compliance lectures that employees forget immediately. Phishing remains the entry point for most breaches, and training that shows employees real examples of attacks targeting your industry works far better than abstract threat descriptions.
Conduct phishing simulations monthly and track which departments click suspicious links most frequently, then target training toward those groups specifically. Quarterly security awareness training increases employees’ understanding of security instructions, with an average clarity rating of 70 out of 100. Your team learns faster when training connects directly to threats they actually face.
Tune Monitoring Tools to Your Environment
Your security team needs real-time monitoring capabilities that surface genuine threats without drowning in false positives. Deploy your monitoring tools with baseline configurations that match your specific environment, then gradually tune detection rules based on actual network behavior. This prevents alert fatigue that forces your team to ignore warnings when genuine attacks occur.
Testing your security systems monthly through tabletop exercises and annual penetration testing prevents failures during actual incidents. Validate whether detection rules function properly before attackers strike, not after a breach exposes gaps in your defenses.
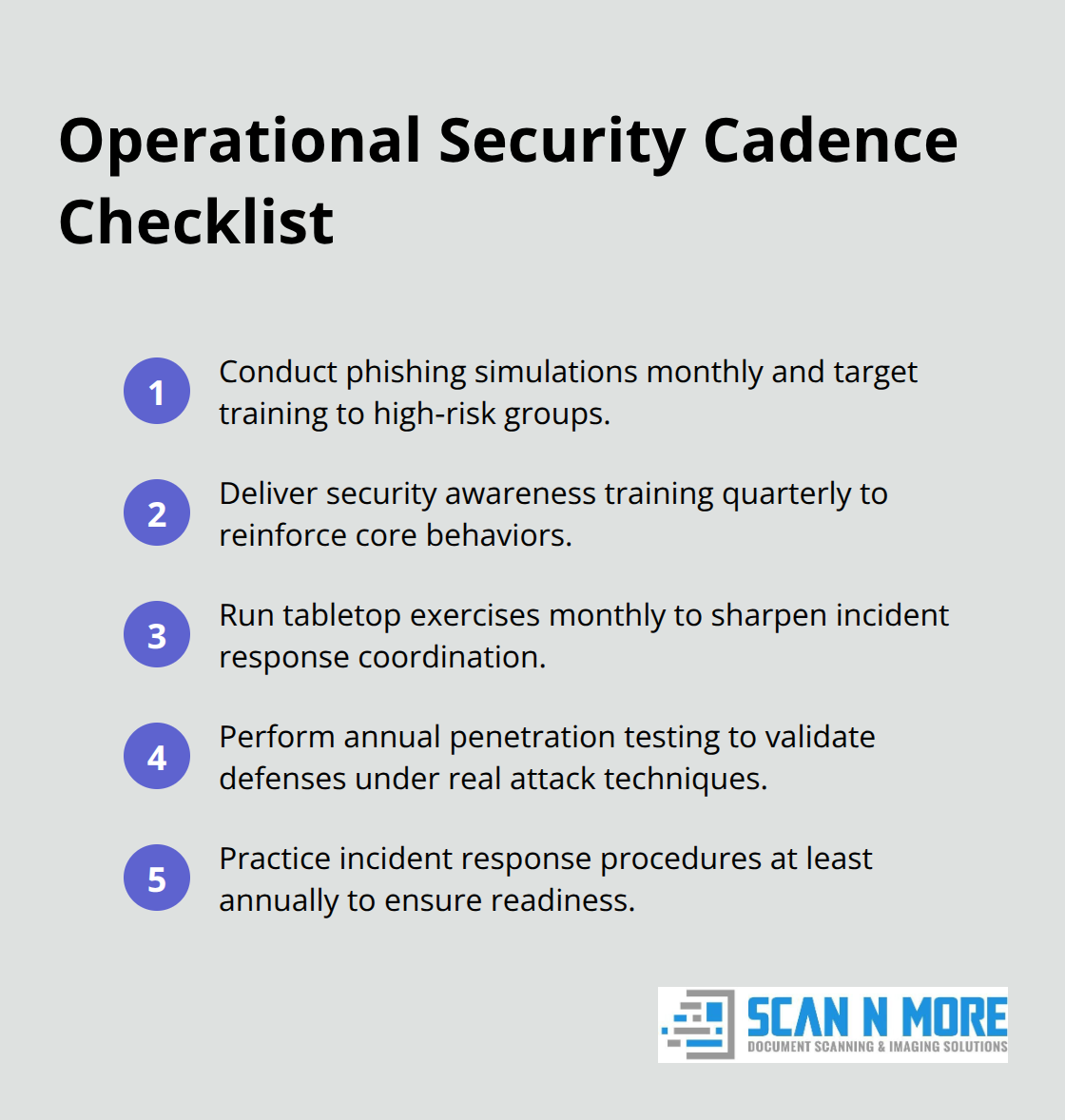
Document and Practice Incident Response Procedures
Document your incident response procedures in written playbooks that assign specific roles and responsibilities before crises occur. Practice your response procedures at least annually so your team knows exactly what to do when attackers strike. This preparation transforms chaotic reactions into coordinated responses that contain damage and accelerate recovery.
Incident response playbooks should address the specific threats your organization faces, not generic attack scenarios. A healthcare organization’s response to ransomware differs significantly from a financial services firm’s approach to payment card theft. Before finalizing your procedures, conduct a comprehensive data security assessment to identify the vulnerabilities your team must prioritize in response planning.
Final Thoughts
Enterprise data security solutions require ongoing commitment long after deployment completes. Your organization’s security posture deteriorates without continuous maintenance, regular updates, and sustained investment in people and processes. Establish a regular patch management schedule that addresses vulnerabilities before attackers exploit them, deploying security updates for operating systems, applications, and security tools within defined timeframes based on severity. Organizations that delay patching create windows where known exploits work reliably, and attackers actively scan for unpatched systems.
Rotate encryption keys annually and review access permissions quarterly to prevent former employees or contractors from retaining system access. Conduct annual penetration testing to validate whether your security controls actually work against real attack techniques, and these tests reveal gaps that internal assessments miss. Employees who understand why data protection matters and recognize their role in defending sensitive information become your strongest defense against phishing, social engineering, and accidental data exposure. Reinforce this culture through regular communication about security incidents, showing how specific behaviors prevented or enabled attacks.
At Scan N More, we understand that protecting sensitive data extends beyond digital systems to physical documents containing confidential information. Our document scanning services transform paper-based processes into secure digital solutions while ensuring compliance with regulatory requirements, and we handle secure digitization that complements your enterprise data security solutions. Measure your progress through concrete metrics like mean time to detect, patch deployment rates, and employee training completion, then review these metrics quarterly and adjust your approach based on what the data reveals about your actual security posture.

